Create an application in an organization¶
Organization administrators can create and mange applications directly within their organizations. These applications can access and consume the organization’s API resources. To create an application, it must meet the following conditions:
-
Use OAuth2.
-
Use only the following grant types: authorization code, client credentials, password, and refresh token.
-
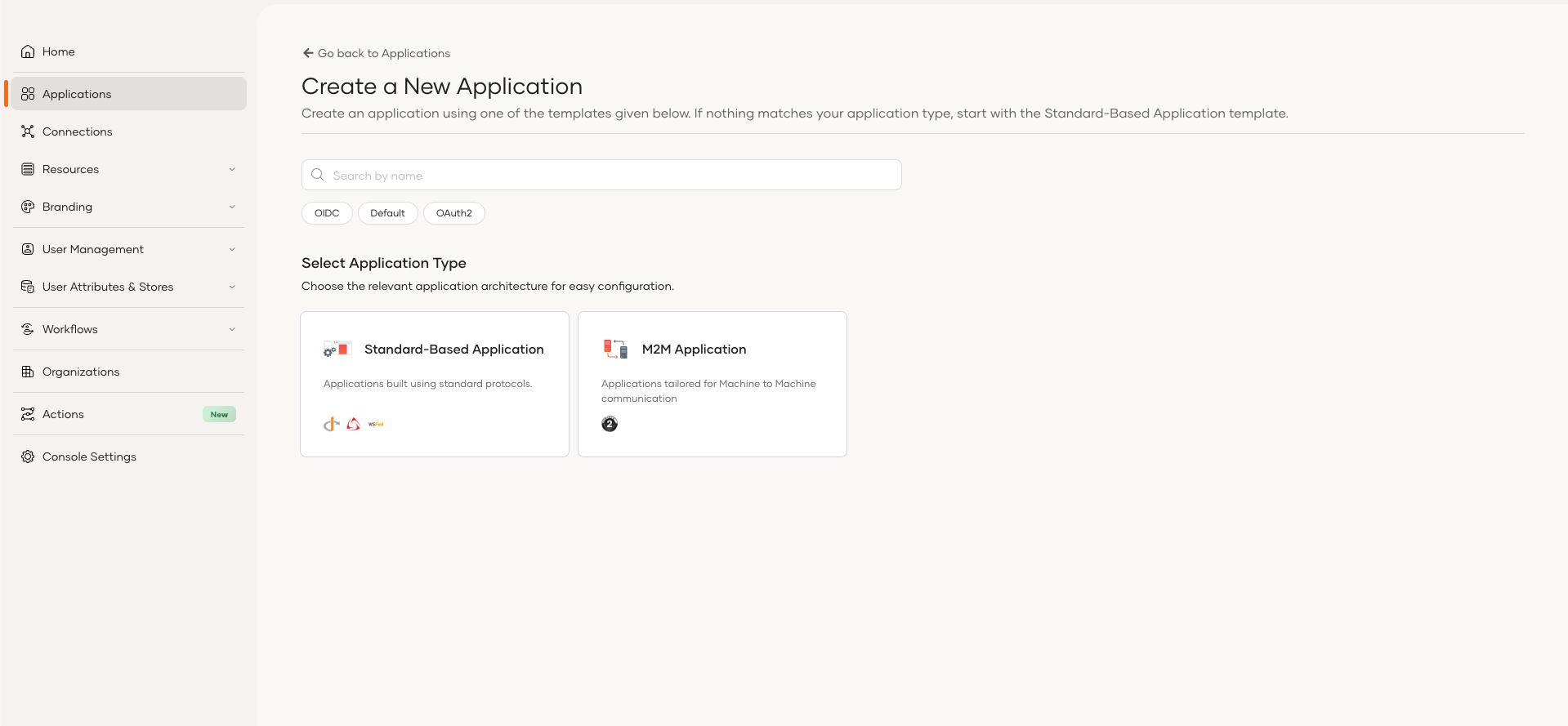
Use a standard-based application or an M2M application template.
You can use either the Console or the API to create an application in an organization.
To create an application,
-
On the Asgardeo Console, go to Organizations and switch to your desired organization.
-
In the organization, go to Applications.
-
Click Add Application and use either the Standard-Based Application or M2M Application template to create your application.
To create an application,
-
Get a bearer token with the
internal_org_application_mgt_createscope. Learn more about [accessing organization APIs] (/asgardeo/docsapis/organization-apis/authentication/) -
Use the Application management REST API to create an application in an organization.
Edit an application¶
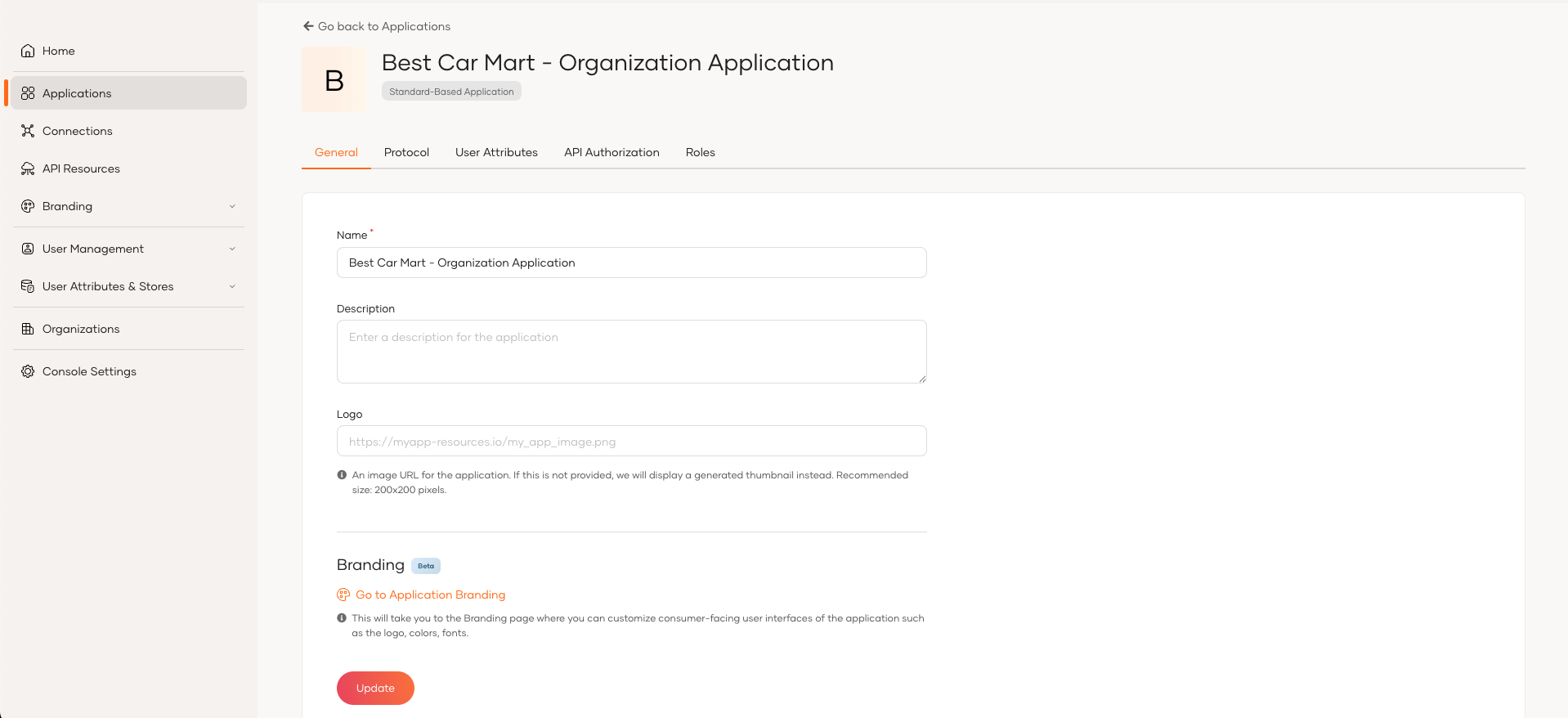
You can find the created applications in the Application section of your organization's Console. You can use the Console to make the following changes to these applications.
- Protocol level configurations
- User attributes related configurations
- Login Flow configurations
- API Authorization for organization application
- Role management for organization application
- Advanced configurations