Discover OpenID Connect endpoints and configurations¶
When building OpenID Connect (OIDC) login in your application using Asgardeo as your identity provider, your application needs the relevant OIDC endpoints and configurations. Your application can get these endpoints in two main steps:
-
Discover the issuer (Optional):
When the issuer URL of the OpenID Provider is not known in advance, your application can dynamically discover it using the WebFinger endpoint.
-
Retrieve the OpenID Connect metadata from the issuer:
Once your application discovers the issuer URL (either via WebFinger or because it’s already configured), your application can fetch the OpenID Connect metadata. This includes all the necessary endpoints (authorization, token, introspection, revocation, logout, etc.), supported scopes, response types, claims, and client authentication methods.
For clients or SDKs that cannot dynamically fetch these endpoints, you can get them manually from the Asgardeo Console.
This guide explains how to discover the OpenID Connect endpoints of Asgardeo using both the API and the Console.
Prerequisites¶
To get started, you need to have an application registered in Asgardeo:
- Register a single-page app with OIDC.
- Register a web app with OIDC.
Use the API¶
This section explains how your application can dynamically discover the OpenID Connect endpoints.
Step 1: Discover the issuer¶
OpenID Provider issuer discovery, process allows a client application to automatically find the location (issuer URL) of the OpenID Provider.
You can use the following endpoint to retrieve the issuer information.
The endpoint accepts the following required parameters.
| Parameter | Description | Sample Value |
|---|---|---|
resource |
The identifier of the user whose OpenID Provider (issuer) you want to discover. | acct:admin@localhost |
host |
Specify the domain or server that hosts the WebFinger service. | localhost:9443 |
rel |
Specify the URI that identifies the type of service you want to locate. | http://openid.net/specs/connect/1.0/issuer |
Sample request¶
var settings = {
"url": "https://api.asgardeo.io/t/bifrost/.well-known/webfinger/openid-configuration",
"method": "GET",
"timeout": 0,
"headers": { "Accept": "application/json" },
"data": {
"resource": "acct:admin@localhost",
"rel": "http://openid.net/specs/connect/1.0/issuer"
}
};
$.ajax(settings).done(function (response) {
console.log(response);
});
var axios = require('axios');
var config = {
method: 'get',
url: 'https://api.asgardeo.io/t/bifrost/.well-known/webfinger/openid-configuration',
params: {
resource: 'acct:admin@localhost',
rel: 'http://openid.net/specs/connect/1.0/issuer'
},
headers: { 'Accept': 'application/json' }
};
axios(config)
.then(function (response) {
console.log(JSON.stringify(response.data));
})
.catch(function (error) {
console.log(error);
});
Sample response¶
{
"subject": "acct:admin@localhost",
"links": [
{
"rel": "http://openid.net/specs/connect/1.0/issuer",
"href": "https://api.asgardeo.io/t/bifrost/oauth2/token"
}
]
}
Step 2: Discover the issuer metadata¶
OpenID Connect Discovery allows you to discover the metadata such as endpoints, scopes, response types, claims, and supported client authentication methods of identity providers such as Asgardeo.
Applications can dynamically discover the OpenID Connect identity provider metadata by calling the OpenID Connect discovery endpoint. The structure of the request URL is as follows: <issuer>/.well-known/openid-configuration.
-
Issuer of Asgardeo
-
Discovery endpoint of Asgardeo
Sample request¶
var axios = require('axios');
var config = {
method: 'get',
url: 'https://api.asgardeo.io/t/bifrost/oauth2/token/.well-known/openid-configuration',
headers: {}
};
axios(config)
.then(function (response) {
console.log(JSON.stringify(response.data));
})
.catch(function (error) {
console.log(error);
});
Sample response¶
{
"introspection_endpoint" : "https://api.asgardeo.io/t/bifrost/oauth2/introspect",
"end_session_endpoint" : "https://api.asgardeo.io/t/bifrost/oidc/logout",
"registration_endpoint" : "https://api.asgardeo.io/t/bifrost/api/identity/oauth2/dcr/v1.0/register",
"token_endpoint" : "https://api.asgardeo.io/t/bifrost/oauth2/token",
"jwks_uri" : "https://api.asgardeo.io/t/bifrost/oauth2/jwks",
"revocation_endpoint" : "https://api.asgardeo.io/t/bifrost/oauth2/revoke",
"authorization_endpoint" : "https://api.asgardeo.io/t/bifrost/oauth2/authorize",
"issuer" : "https://api.asgardeo.io/t/bifrost/oauth2/token"
}
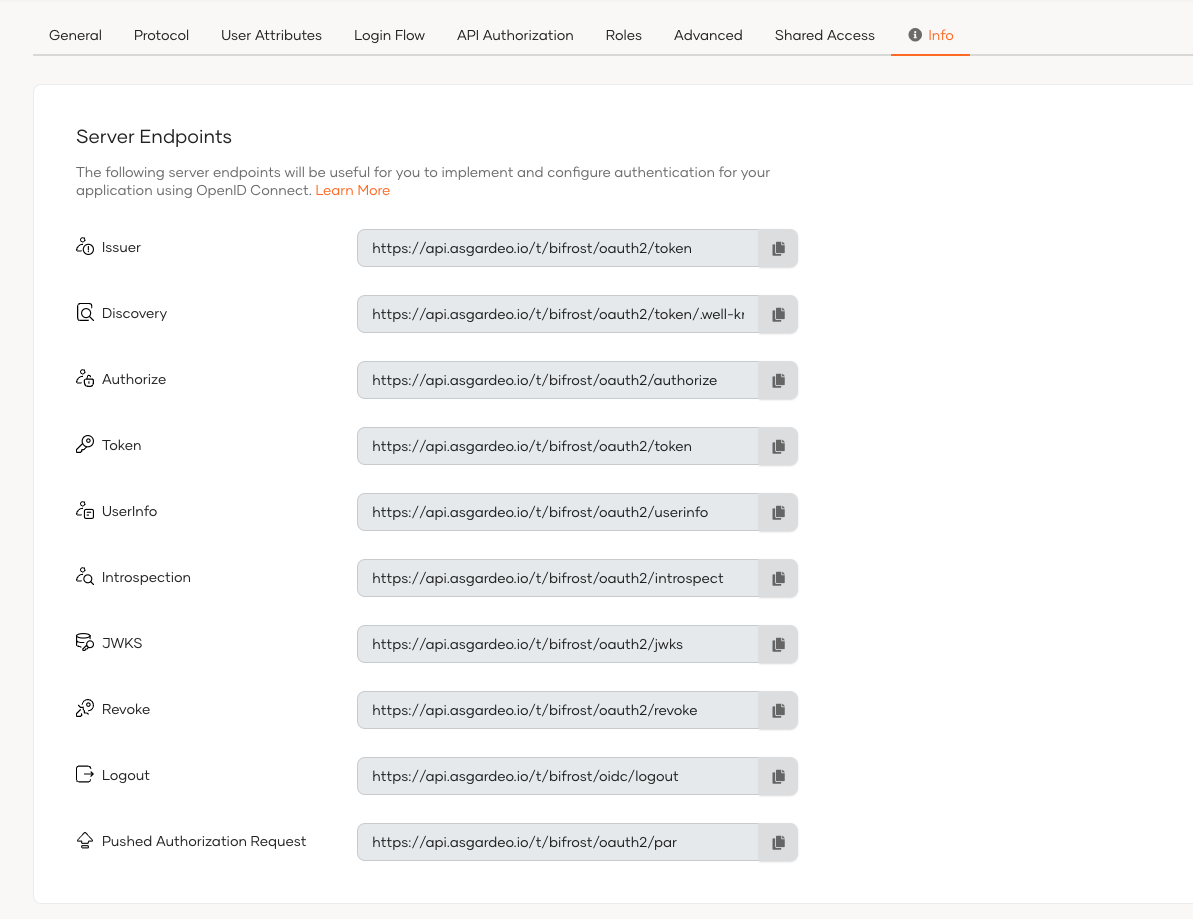
Use the Console¶
For applications and SDKs that can't dynamically resolve OpenID Connect endpoints, you can manually copy the relevant information from the Console. To do so,
-
On the Asgardeo, go to Applications.
-
Select your OIDC application from the list.
-
Go to the Info tab of the application and find the server endpoints to your organization.
What's next?¶
Explore how OpenID Connect endpoints are used when you implement login to your applications:
- Implement login for single-page applications using the authorization code flow with PKCE.
- Implement login for traditional web applications using the authorization code flow.