Add concurrent sessions based access control
# Add concurrent sessions based access control
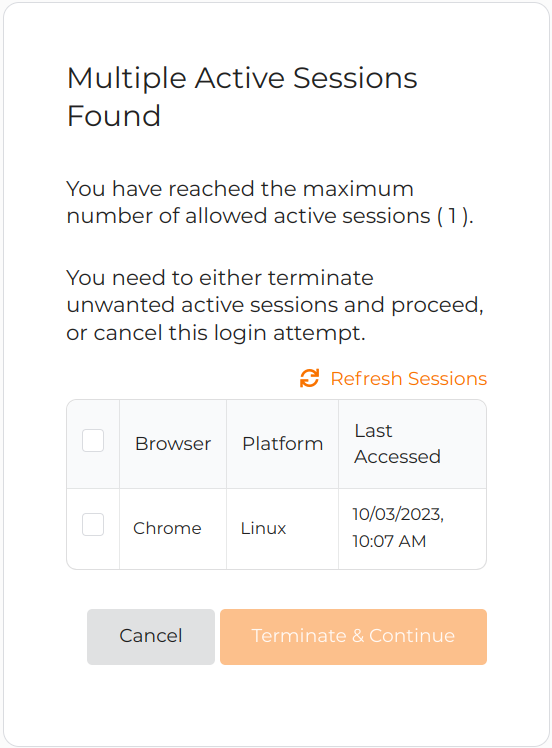
You can effectively control the number of concurrent user sessions for an application by implementing the Session-Based conditional authentication template. Users are redirected to a dedicated page where they can manage their existing sessions or cancel the current authentication request if they exceed the number of allowed concurrent sessions.
# Scenario
Consider a scenario with two user groups, admin and manager. Users belonging to these groups are limited to having only one active session at a time. If they try to initiate a second session, they will be presented with a list of their current sessions and offered with the following two options:
- Terminate any of their existing sessions.
- Cancel their current authentication attempt.
# Prerequisites
You need to register an application with Asgardeo. You can register your own application or use one of the sample applications provided.
Create two user groups named
adminandmanagerand assign user accounts to them. For instructions, see the following:
# Configure the login flow
To configure the login flow with concurrent session-based access control:
On the Asgardeo Console, click Applications.
Select the relevant application and go to it's Login Flow tab.
Add concurrent session-based access control using your preferred editor:
Using the Classic Editor
To add session-based access control using the classic editor:
Click Start with default configuration to define the login flow starting with the
username and passwordlogin.Turn on Conditional Authentication by switching the toggle on.
Select the Access Control > Session-Based template.
Using the Visual Editor
To add session-based access control using the visual editor:
Switch to the Visual Editor tab, and expand Predefined Flows > Conditional Login Flows > Access Control.
Click + ADD next to Session-Based to add the session-based access control authenticator.
Click Confirm to replace any existing script with the selected predefined script.
Update the following parameters in the script.
Parameter Description groupsToStepUpAn array of user groups that can access the application. For this scenario, enter adminandmanager.maxSessionCountThe number of allowed sessions for the user
For this example scenario, enter1as we allow only one concurrent active sessions per user.Click Update to confirm.
# How it works
Shown below is the script of the session-based conditional authentication template.
// This script will prompt concurrent session handling
// for any user who belongs to one of the given groups
// If the user is a member of the following groups, concurrent session handling will be prompted
// and it will either kill sessions or abort login based on number of active concurrent user sessions
var groupsToStepUp = ['admin', 'manager'];
var maxSessionCount = '1';
var onLoginRequest = function(context) {
executeStep(1, {
onSuccess: function (context) {
// Extracting authenticated subject from the first step
var user = context.currentKnownSubject;
// Checking if the user is assigned to one of the given groups.
var isMember = isMemberOfAnyOfGroups(user, groupsToStepUp);
if (isMember) {
Log.info(user.username + ' belongs to one of Groups: ' + groupsToStepUp.toString());
executeStep(2, {
authenticatorParams: {
local: {
SessionExecutor: {
MaxSessionCount: maxSessionCount
}
}
}
}, {});
}
}
});
};
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
Let's look at how this script works.
- When step 1 of the authentication flow is complete, the onLoginRequest function retrieves the authenticating user from the context.
- The function verifies whether the authenticating user is a member of the groups listed in
groupsToStepUp. - If the authenticating user is a member of one or more groups in
groupsToStepUp, authentication step 2 is prompted withmaxSessionCountbeing passed as a parameter to the Active Sessions Limit handler.
Find out more about the scripting language in the Conditional Authentication API Reference.
# Try it out
Follow the steps given below.
Access the application URL.
Log in to the application as a user belonging to the
adminormanager.Attempt to log in as the same user from a second browser.
Now, the user will receive a prompt, allowing them to either terminate one of their existing sessions or cancel the authentication request for the second session.