All Users Deserve Seamless and Secure Digital Experiences
Achieving exceptional digital experiences can be challenging, whether for employees, consumers, business customers, or partners. IAM is fundamental, and you need a flexible, extensible IAM solution to realize your vision. WSO2 offers the open-source IAM solution you require.
IAM Solutions
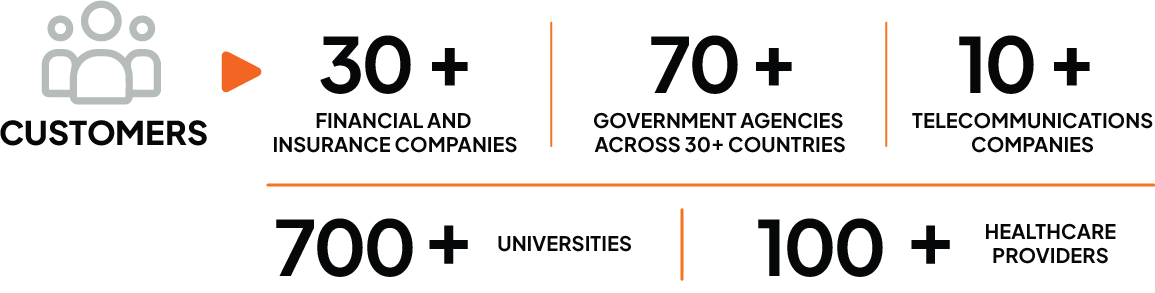
Over 1 Billion Managed Identities Across
1500+ Commercial Deployments Globally
Customer Identity
Create frictionless, secure and private access for your consumers and business customers.
Learn More
For Consumers
(B2C)
Launch your consumer-facing applications confidently and securely, so you can identify, convert, and retain the right consumers.
Learn MoreFor Business Customers
(B2B)
Enable secure access for your B2B business customers and their consumers with flexible organization management capabilities.
Learn MoreFor Citizens
(G2C)
Accelerate government digital transformation to empower citizens with frictionless, safe access to public services.
Learn MoreWorkforce Identity
Empower your employees with secure access to corporate apps, no matter where they work.
Learn More
Unlock Secure Workforce Productivity
Give your workforce effortless, secure access to the apps they need. Enforce the right level of security for every action, including passwordless authentication.
Onboard Users and Integrate Apps Seamlessly
Automate user management and access rights using our built in user management tools or by integrating your own identity providers.
Secure Access Priced Affordably for your Growing Business
Take advantage of WSO2’s flexible, affordable pricing. It’s also easy to extend licensing for external customers.
API Access Management
Protect critical APIs by ensuring only authenticated and authorized clients can gain access.
Learn More
Enforce API Access Security with WSO2’s Comprehensive IAM Solution
Far more than simply managing tokens, WSO2 enables authentication, authorization, federation, privacy, and more.
APIs are Key to any Digital Transformation Journey
APIs are consumed by people, devices, or things. Managing all digital identities is critical in any API-based solution.
Ensure Effective, Efficient API Security at any Scale
Hundreds of organizations worldwide, from small startups to national governments, depend on WSO2 to secure trillions of API transactions annually.
One Solution, Multiple Deployment Options
Deploy how and where you need
Learn how WSO2 is the best choice for your access management needs
Advantage WSO2 in vendor support, deployment options, API security, and CIAM capabilities.
Learn MoreThe Foundation for Identity-led Digital Transformation
WSO2 IAM helps take your digital transformation projects to the next level, with richer, more interactive, and highly personalized user interactions. Build identity-aware cloud native applications for your consumers, business customers, and employees.
WSO2’s Integrated Platform