The Ultimate Guide to Cybersecurity

- Gomathy Kumarakuruparan
- Technical Writer, WSO2
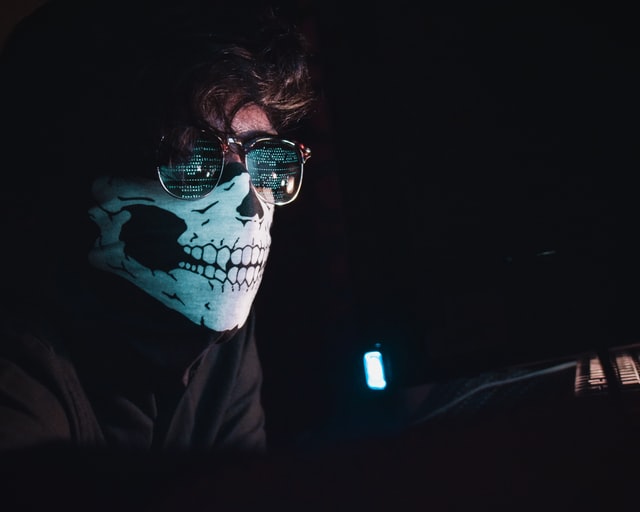
Image credits: Nahel Abdul Hadi on Unsplash
Cybersecurity Vocabulary
Cybersecurity is the practice of protecting our computers, networks, mobile phones, and any other related electronic devices from malicious attacks. It can be treated as a subcategory of information security. At the same time, it deals with more than just information. While information security focuses on securing information in all forms, including both analog and digital, cybersecurity focuses on securing digital information, along with protecting physical devices from threats.
Let's start with an introduction to some commonly used terms:
The CIA Triad
This framework is considered to be the backbone of both information security and cybersecurity.
- Confidentiality - The right level of access to the right people. Privacy is key. This is achieved using passwords, encryption, security tokens, biometrics, etc.
- Integrity - Data consistency. No alterations during the data transfer. This is ensured using methods like checksums and user access controls.
- Availability - Data should be available to the concerned parties at all times. This is taken care of by the means of continuous IT support, regular hardware and software checkups, disaster recovery, and contingency plans.
Encryption
Encryption is a combination of two words, en, and crypto that together mean “make hidden”. The data you want to transfer over a network is encrypted using a key. The converted secure text is called ciphertext. Decryption is the process of converting it back to understandable data. This is again done using a key. If the same key is used for both encryption and decryption, it is a symmetric encryption. If two different keys are used, it is asymmetric encryption.
Obfuscation
Obfuscation is similar to encryption but instead of hiding it, the data is made unclear and hard to interpret.
Hack
Exploiting a weakness in software, device, or a network to gain access to it.
Hackers
They are skilled people who are capable of finding vulnerabilities, bugs, and loopholes in systems. This enables them to gain access to the device, network, and in certain cases even the network of networks.
Hactivists
The intention of these people is usually centered around politics or religion. They are a nuisance to the government but are not frowned upon by the public since the information they gather ends up exposing societal injustice at times.
Ethical hackers
These guys are the “good guys”. They hack systems to find the vulnerabilities in it so that the organizations can patch those issues before releasing it to the public. This is a professional role in many organizations.
Important note: Please note that the terms "black hat hackers" and "grey hat hackers" are used in this blog since alternatives do not exist in the industry to my knowledge. We're certainly not associating certain colors with poor ethics. We've removed prejudicial terms and descriptions from the entire body of source code across our products and projects. You can read more about it here.
Black hat hackers
In simple terms, “the bad guys”. They hack systems with the intention of causing danger for mere personal gain.
Grey hat hackers
These individuals are just keen to know what they can do with some free time and devices with instabilities. Most of them end up reporting them to the organizations. While few organizations would be accepting of this as it benefits their businesses, a few others might end up taking it more personally. Hacking without the consent of the concerned party is a punishable offense.
Skript kiddie
Amateurs in hacking. They usually do not know to hack systems using their code chunks, so instead they use what’s available online.
Malware
Malicious software. A code chunk that makes the system behave in a way it is not expected to.
Keylogger
A program that monitors and records key strikes to steal user information.
Hacking: The Basics
This is the basic flow of hacking - please keep in mind that there can be many other sophisticated methods. The most basic method of hacking is “footprinting”. Using this, hackers get the fundamental information they require to hack an overall system. The most common way of doing this would be browser searches. If hackers have already decided that their target will be a certain organization, they obtain their information using the whois lookup option on the ICANN website. They can also get some information about what kind of software the organization uses by going through the skill requirement section of the career vacancies the company posts. Once they have this passive information, they start observing the target. This is carried out by scanning the ports or using ping sweeps.
The next method would be enumeration, famously known as social engineering. This has threatened our globalized world more than once (though we only know of the widely spoken about Facebook crisis). Some hackers are gifted with great communication skills and all they need to do to get information about the person or their organization is to talk to them. Once they hack the system based on all these methods, they can gain more control over the systems by self promoting them as the admin.
Expert hackers barely leave any tracks of their intrusion and they always build a backdoor so that they can revisit the target. What we must note is that all hackers don’t follow all of these steps - it is usually just a combination of one or two ways if the system is unstable by itself.
Common Cyber Threats
Image credits: Markus Spiske on Unsplash
Phishing
In this method, the user information is captured illegally by luring them to click on certain insecure links or download unsafe attachments. When the user clicks on the link or downloads the attachment, malware is instantly installed in the user’s device. These evil websites usually copy the logos or web templates of well known brands with very minor differences. For example, an online shopping website can be replicated with minor changes. When the user enters the credentials to login or pay, a keylogger is used to steal this information.
Brute force attacks
This is a very common attack based on trial and error. It checks all the key combinations that can be the pin or password. There are software used to generate numerous possibilities of the key combinations within seconds. If any one of them matches, the hacker gets access to the system. This can take between a few minutes to years. A dictionary attack is a form of brute force attack where the software scans through all the words in the dictionary to unlock a pin or password.
Bots
A Trojan horse is used to attack a device and infect it completely so that it is controlled at its core. Botnet is a network of such bots and the botmaster is the one who controls these botnets.
Man in the middle attacks
As the name suggests, the bad guy takes control of two computers that are involved in a data transfer. This is successful only if he gains control of both the devices. Mostly prevalent in open wireless connections. This is also possible by hijacking an email communication or hijacking a particular session going on between a device and a website.
DoS and DDoS mishaps
Denial of Service (DOS) is a strategy where massive traffic is sent to a website via thousands of requests per second from a single source. Distributed Denial of Service (DDoS) is when similar requests are sent from multiple sources. This is more complicated and it is tedious to differentiate the legitimate requests and the ones that are sent to cause trouble, resulting in having to block all the requests to the site. This attack is mostly done using botnets.
Cross-site scripting (XSS) attacks
A code chunk that is inserted in a functional website or web application. When users visit this website, they become the targets.
Ransomware
This is a severe threat since when infected, the system user is completely locked out of the system. This is not targeted at anyone specific, meaning that everybody is equally viable to become a victim. Common locked screens show messages like “You have accessed prohibited websites and fined $2000. On delayed or ignored payment, this can lead to a sentence of up to seven years”. These messages have a threatening tone and very specific details that make users fall prey to it. Unfortunately, in more than half of the cases, the information is not accessible even after payment.
These aren’t the only threats. There are many other challenges cybersecurity professionals deal with. Some of the other threats include SQL injections, pings, and malware entities like viruses, worms, and trojans of different intensities.
How Can You Stay Safe?
Image credits: Liam Tucker on Unsplash
As an individual:
- Use lengthier passwords - The longer the password or pin, the more combinations the software needs to traverse before it finds the right combination during a brute force attack. Since sign in should happen within a certain time frame, if the combination is not met before it expires, it is unlikely to be hacked.
- Use complicated passwords - Passphrases are said to be more secure than passwords because of its length. However, this is not always true. As mentioned above, certain software that can traverse through an entire dictionary to find your passphrase. So the solution is to create a password or passphrase that makes sense to you but not outsiders. Usage of special characters is a plus too.
- Do not click on random links online - When you get links or attachments from your friends via mail, you can either check with them if they actually sent it or hover over the “from” link to see the origin address. You can hover over the links as well before clicking on them. Always scan email attachments.
- Be vigilant when you visit websites - Look for spelling mistakes and differences in the logos. Domain extensions like “.biz” and “.info” can be suspicious. Also, make sure there aren’t excessive advertisements on the page since this might mean it is infected with adware.
Additional Tips for Organizations
- Request an ICANN host to hide your profile information from the website.
- Have password management mechanisms for organizational applications like enforcing stronger passwords, restricting the number of login attempts, and encouraging time outs on a number of failed attempts.
- Ensure all employees have updated antivirus and anti-malware at all times.
- Having an increased bandwidth, though not a solution can prevent the site from going down when there is excessive traffic due to a DDoS attack.
- Use biometric authentication instead of passwords.
- Use 2-factor or multi factor authentication (MFA) rather than relying on a single factor.
- Place honey pots in production. These will contain resources that will distract the hackers from the actual resources while you can work on your production releases peacefully.
- If BYOD (Bring Your Own Device) is permitted in your organization, design BYOD policies to secure company information accessible in the employees’ personal devices.
WSO2 Identity Server is an open source IAM solution that can solve your organization’s identity and access management requirements.
Stay safe everyone!



