GSMA Open Gateway: The Standard That Turns Network Capabilities Into Developer-Friendly Products

- Dev Wijewardane
- Senior Director / Field CTO, WSO2
Introduction
The telecommunications industry is undergoing a shift from proprietary, connectivity-focused mobile networks to open, programmable platforms. This transformation is being accelerated globally by GSMA Open Gateway, an initiative that introduces a standardized, API-driven approach to exposing mobile network capabilities, enabling developers and enterprises to interact with telecom networks in a cloud native way. Open Gateway establishes an interoperable, federated platform that overcomes the fragmentation in the telecom sector caused by regulatory, technological, and historical factors.
This initiative offers capabilities such as identity verification, fraud detection, network quality assessment, and consistent, interoperable billing. Abstracting the complexity of telecom networks through simple cloud-like interfaces enables third parties to integrate with network functionality without needing custom operator integrations or specialised telecom expertise. This is achieved through open specifications developed by the CAMARA project, an open source collaboration under the Linux Foundation, that defines RESTful API specifications, data models, and security patterns for accessing network services.
These APIs enable commercially significant use cases across identity and fraud prevention, IoT and connected device management, enterprise security, and performance-sensitive 5G services. By exposing trusted, network-level capabilities through standardized interfaces, GSMA Open Gateway supports secure, real-time, and context-aware digital applications.
The GSMA Open Gateway acts as a foundational layer for the global digital economy, with potential adoption across operators and regions. For consumers, it facilitates secure, real-time, and context-aware digital services. For telcos, it transforms the network from a commoditized utility into a programmable platform, generating new revenue streams beyond traditional connectivity.
The challenges solved by Open Gateway
The Open Gateway initiative was established to address several persistent challenges within the telecommunications sector.
Fragmentation to federation
The issue of network API fragmentation has long plagued the telecommunications sector. Historically, network operators exposed their network services (e.g., user data, location data), if at all, through proprietary interfaces, inconsistent security protocols, and custom data models. This practice led to higher integration expenses, longer onboarding times, and constraints on scalability.
GSMA Open Gateway addresses this by establishing common, standardized API definitions that function uniformly across all participating operators. By collaborating on API specifications through the CAMARA project, Open Gateway introduced a "build once, deploy anywhere" model. This fundamentally lowered the technical and commercial hurdles associated with integrating services across multiple operators, making network capabilities significantly more accessible to a wider developer community.
Connectivity revenue to API monetization
Operators have invested heavily in 4G and 5G infrastructure, yet their ability to monetize network capabilities has been largely limited to basic connectivity and messaging. Advanced network functionalities, such as identity verification, real-time location awareness, and network quality control, have remained internal assets.
Open Gateway enables these capabilities as productized, API-based interfaces with defined SLAs, security models, and billing mechanisms. This allows operators to participate in digital value chains far beyond their conventional service offerings. This fundamentally shifts the operator's role from a pure infrastructure provider to a crucial platform enabler.
Telecom complexity to developer alignment
Modern application development is built around cloud-native principles such as RESTful APIs, automated scaling, and CI/CD pipelines. Traditional telecom interfaces were not designed for these models, creating integration friction.
Open Gateway addresses this by exposing mobile network capabilities through developer-friendly APIs, abstracting telecom complexity and enabling integration into modern cloud and microservices environments.
National to international
Many telecom operators find it difficult to scale internationally due to inconsistent network capabilities, regulatory constraints, and operator specific implementations. In other words, what works in one market will require a significant amount of re-work to be used in another.
The creation of a federated global framework where operators have the ability to expose equivalent capabilities through standardized APIs while retaining local control, addresses this gap, allowing enterprises and developers to scale services across regions with minimal rework.
Technical foundation
With a common set of API definitions and a federated architecture, Open Gateway positions the network as a digital platform, granting developers and businesses access to reliable network functions without requiring them to navigate the underlying complexity of telecom infrastructure. In practice, these standardised APIs are exposed and governed through operator-deployed API gateways or API management platforms, which provide the runtime capabilities required for secure exposure, traffic control, observability, and monetization.
An API-first, open, and federated architecture
Open Gateway specifies a common set of northbound APIs, which each operator then implements within their own environment. These APIs act as an abstraction layer between applications and the underlying telecom network. Integration with core network functions, operational support systems (OSS), and business support systems (BSS) is handled within the operator environment, ensuring that external consumers interact only with standardized, policy-governed interfaces. This design ensures global interoperability while preserving local autonomy: operators retain full control over their networks and data, while applications gain the ability to interact with consistent, standardized interfaces across various markets.
CAMARA as the open specification backbone
The CAMARA project serves as the foundation for Open Gateway by defining the technical specifications for network APIs. This vendor-neutral environment encourages collaboration among operators, cloud providers, and technology partners to collectively design API contracts, security patterns, and data models.
By basing Open Gateway on these open specifications rather than proprietary standards, CAMARA guarantees transparency, sustainability, and extensibility. The API definitions themselves are technology-agnostic, REST-based, and properly versioned. This approach supports rapid innovation and maintains stability while ensuring backwards compatibility.
Security, policy and trust built into the API layer
The APIs are inherently secure, incorporating robust security measures such as strong authentication, authorization, rate limiting, and auditability. These mechanisms are typically implemented using industry-standard identity and access management frameworks such as OAuth 2.0 and OpenID Connect, ensuring alignment with enterprise security architectures. Importantly, end-user consent and policy enforcement are prioritised as "first-class" concerns in the specification. As these APIs expose network-level signals originating from the operator's secure infrastructure, they offer a higher degree of assurance when compared to device or application-level alternatives. As a result, Open Gateway is ideally suited for demanding use cases, including identity verification, fraud detection and prevention, and regulated digital services.
Future-proof integration model
Open Gateway establishes a technical layer that simplifies complex telecom network functions, transforming them into accessible, consumable, application-level services. Key capabilities such as authentication, device location tracking, network quality management, and billing are exposed through APIs. These APIs operate independently of the underlying network technology, whether it is 4G, 5G, or a hybrid setup.
As this layer decouples the application logic from the evolution of the network, it allows operators to modernize their cores and introduce new services while existing API contracts remain unchanged. This provides developers and enterprises with a future-proof integration model that aligns with cloud native design principles and reduces the dependency on specific network technologies. API lifecycle management, versioning control, and identity federation further ensure that integrations remain stable as both network technologies and application ecosystems evolve.
Architecture patterns and deployment models
Implementing GSMA Open Gateway involves more than exposing a set of standardized APIs. It requires architectural choices across API management, routing, performance, security and integration with core network functions. A number of different deployment models exist and each of them are best suited for different use cases, which range from latency-sensitive, edge-enabled services to enterprise-facing APIs. This section introduces two patterns focusing on: federated API gateway and an edge-enabled gateway pattern.
Federated API gateway pattern
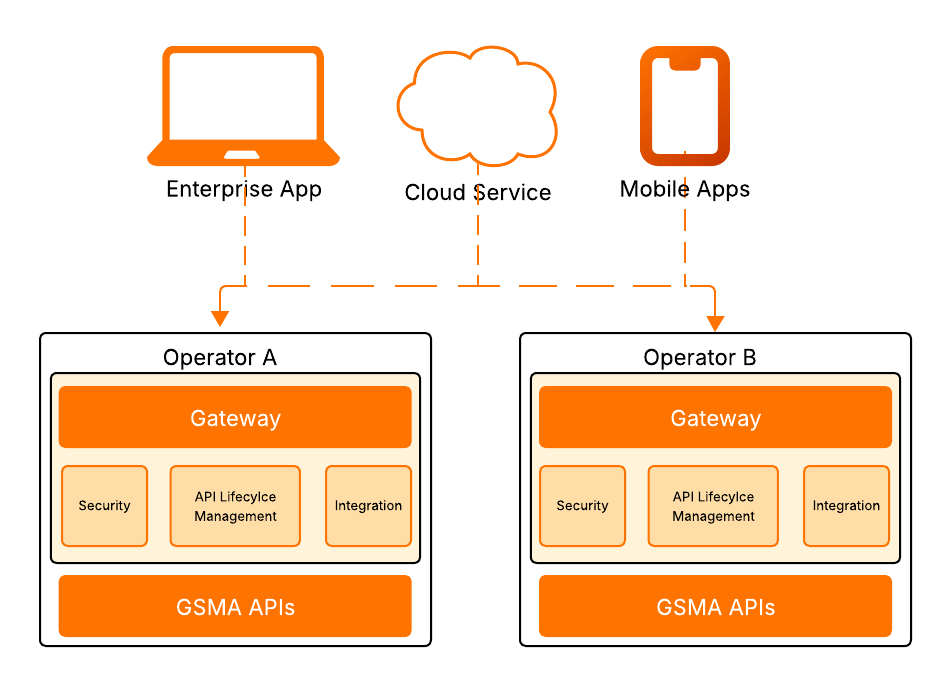
Figure 1: Federated gateway architecture
In this context, federation does not imply a centralized technical gateway, but rather a coordinated model in which independently operated operator gateways implement common API specifications and trust frameworks.
Each mobile network operator exposes standardized Open Gateway APIs through an operator-hosted API gateway, implementing common API contracts, security models, and behaviours defined by the Open Gateway framework and CAMARA specifications.
There is no single centralized gateway for all operators. Instead, federation allows independently operated operator gateways to present a uniform external interface. Each gateway becomes the control point for authentication, rate limiting, observability, and policy enforcement. For applications, the experience is consistent and predictable; for operators, data control, network access, and regulatory responsibilities remain local, preserving sovereignty, resilience, and operational independence.
Federated API gateway pattern: Use cases and examples
The federated gateway model is best suited for use cases where compliance, consistency, and multi-operator scalability matter more than ultra-low latency.
- Identity and fraud prevention APIs (SIM Swap, Number Verification, Device Status)
Example: A bank checks for recent SIM swaps before approving high-value transfers across multiple countries using the same standard API. - APIs involving regulated subscriber data
Example: A government portal verifies mobile numbers during onboarding, with each operator processing requests locally to maintain national data sovereignty. - Multi-country enterprise deployments
Example: A fintech app verifies whether a phone number is active before registration, integrating once and scaling across participating operators. - Foundational Open Gateway rollouts
Example: Operators first expose standard identity APIs under a federated model before introducing advanced 5G or edge-based services.
Trade-offs
- Implementation variability: Conformance may be consistent, but maturity can vary across operators, affecting performance, reliability, and onboarding, especially early on.
- Multi-operator complexity (in some models): Global applications may need routing/operator selection and failover logic unless an aggregator layer abstracts this.
- Feature rollout skew: API versions and enhancements may not ship simultaneously across operators, leading to capability differences across markets.
- Coordination overhead: Sustained interoperability requires governance mechanisms such as conformance testing and certification programs.
Edge-enabled API gateway pattern
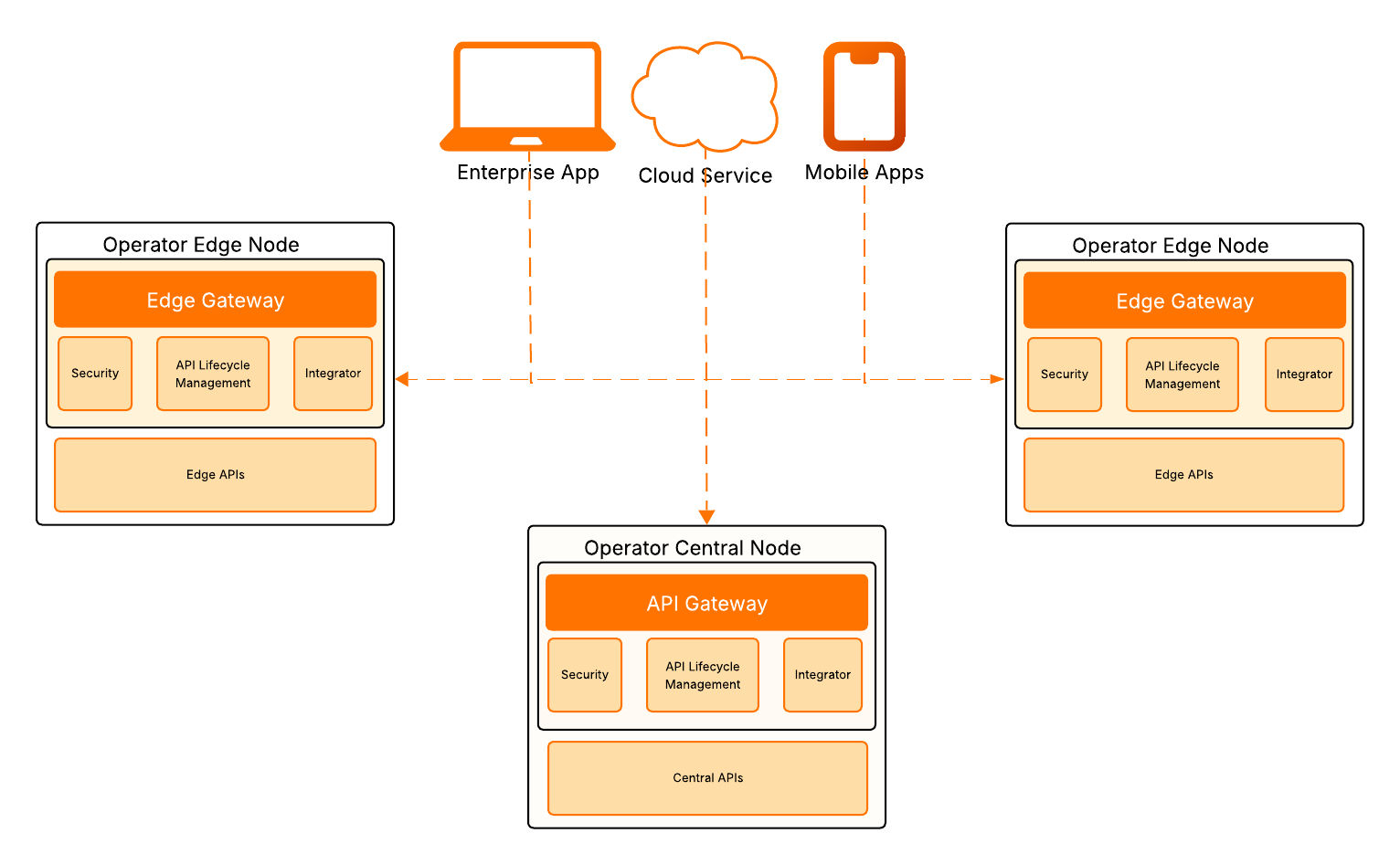
Figure 2: Edge-enabled gateway architecture
The edge-enabled architecture places selected APIs closer to the consuming applications, usually within the operator’s edge nodes, while other APIs are exposed centrally. This hybrid configuration consists of a central gateway and complemented by one or more edge-resident API gateways. In this architecture, the edge gateway exposes the same standardized contracts that are exposed by the central gateway but executes latency sensitive APIs, locally. These latency sensitive APIs include requests that require real time interaction with the network, location verification, quality control and session aware services. Less time-critical operations continue to be handled centrally.
Placing gateways at the edge achieves a number of objectives including:
- Reducing network round-trip time between the application, the API and the underlying network functions.
- Localising access to network state including subscriber context and session parameters.
- Aligning with 5G principles where distributed user plane functions and edge compute are already present.
Edge-enabled API gateway pattern: Use cases and examples
The edge-enabled gateway model is best suited for scenarios where low latency and immediate network interaction are critical.
- Latency-sensitive applications (quality on demand, real-time session control)
Example: A cloud gaming platform requests guaranteed network quality at session start to minimise lag. - Real-time location and context-aware services
Example: A ride-hailing app verifies precise user location instantly before matching drivers. - Mission-critical industrial systems
Example: An industrial IoT platform reacts immediately to network state changes for safety monitoring and automation control. - Immersive and high-bandwidth experiences (AR/VR, live events)
Example: An AR application in a stadium uses edge-hosted APIs to deliver low-latency interactive features. - 5G and MEC-based service differentiation
Example: An operator offers premium low-latency network APIs to enterprise customers as a differentiated 5G service tier.
This model prioritises performance, responsiveness, and premium service differentiation over centralised simplicity.
Trade-offs
- Architectural complexity: Deploying gateways across both central and edge environments increases orchestration, lifecycle management, and observability complexity.
- Higher infrastructure costs: Edge environments are more expensive to operate at scale, requiring justification through premium, latency-sensitive use cases.
- Operational duplication risk: Running APIs at both core and edge can introduce configuration drift, version management challenges, and operational overhead.
- Limited API applicability: Only a subset of APIs benefit from edge placement; most enterprise-facing APIs do not require ultra-low latency.
The future of GSMA Open Gateway
The future of Open Gateway will not be shaped by individual APIs, but by how successfully it becomes embedded within global applications, cloud platforms, and digital identity ecosystems. To achieve this, it must become native to developer workflows rather than remain a telecom add-on.
Its success depends on widespread adoption by developers and enterprises, driven by strong developer experience, clear pricing models, and compelling use cases that demonstrate measurable ROI.
Operators can now tap into new revenue streams by participating in digital ecosystems they were previously largely excluded from. By integrating more deeply with cloud hyperscalers, edge platforms, and IoT ecosystems, operators can participate more fully in digital value chains and monetise network intelligence beyond traditional connectivity.
A core aim of Open Gateway is interoperability at scale. By standardizing APIs across operators, it enables developers to "write once and deploy" across various carrier networks globally. This is an essential step toward broad enterprise adoption.
However, regulatory requirements, multi-operator alignment, and competition from hyperscalers present real challenges. How these are addressed will determine whether Open Gateway becomes a transformative industry standard and shape the role of telecom operators in the digital economy in the years ahead.
Bringing GSMA Open Gateway into production requires secure and scalable API management to properly expose, govern, and monetise network capabilities. Platforms such as WSO2 API Platform can help operators turn standards into real, production-ready services.
To explore how production-grade API management can support your Open Gateway strategy, visit: https://wso2.com/api-platform/.

