Identity for Every User: AI Agents to Customers
For unmatched developer-centric flexibility without a proprietary black box, WSO2 Access Manager allows you to secure humans, apps, and agents everywhere.
Trusted by Organizations
worldwide
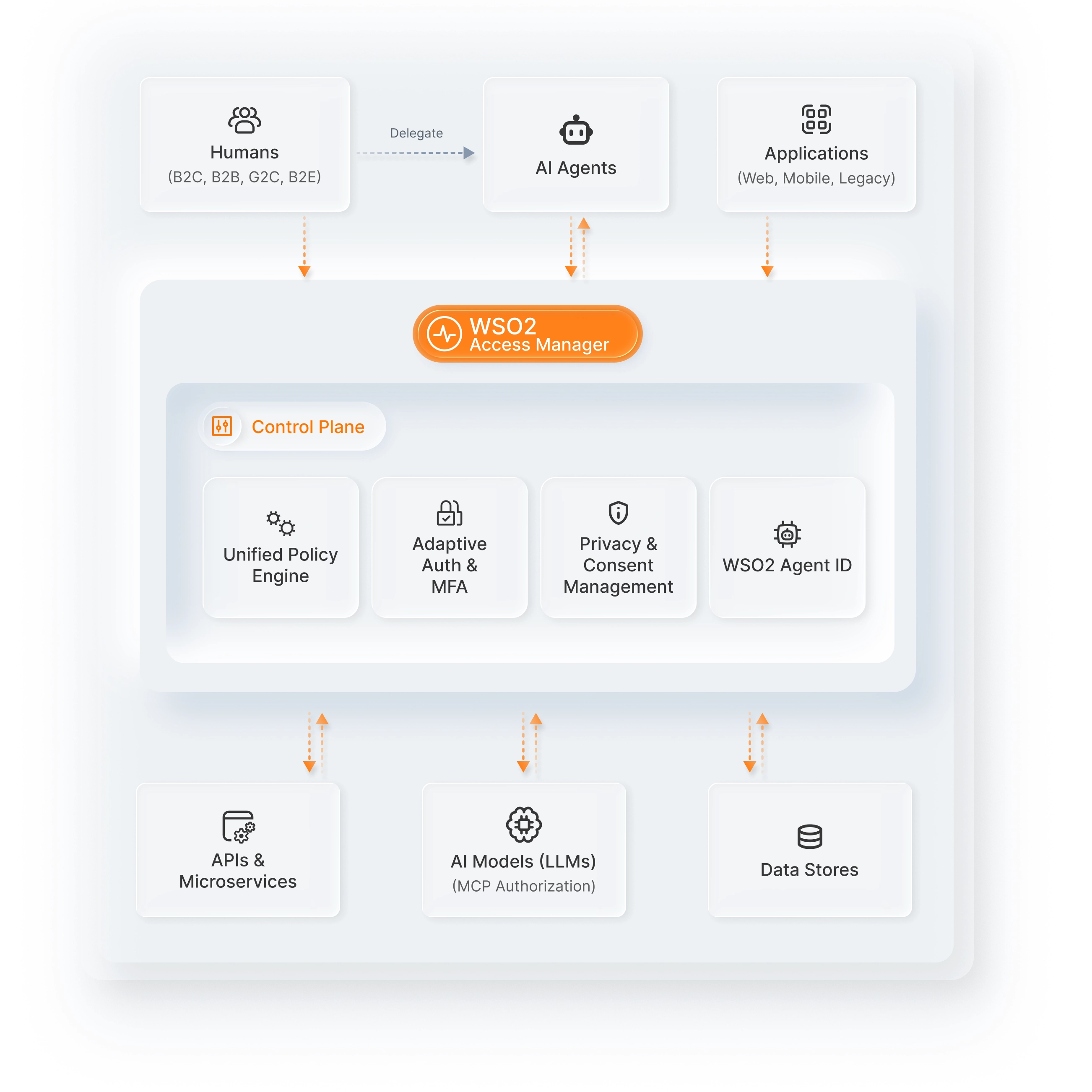
Security, flexibility and control
for humans, services and agents
Manage humans and AI agents from one control plane. WSO2 Access Manager provides the API-first foundation to
secure, authorize, and audit every digital interaction.
The developer-first choice for modern identity
Developer-first design with extreme extensibility
Use an API-first approach to customize every stage of the user journey. Avoid proprietary black boxes with a platform built for deep technical integration.
Open source freedom without hidden vendor lock-in
Retain full control of your identity data and logic. Benefit from a transparent, community-vetted codebase that ensures long-term agility and security.
Deploy anywhere across hybrid and cloud environments
Run WSO2 Access Manager on-premises, in private clouds, or as a containerized solution. Maintain consistency across your infrastructure with ease.
Scale to millions of users with proven reliability
Effortlessly manage complex B2B and B2C requirements. From progressive profiling to delegated administration, handle massive growth without performance loss.
Future-proof security for humans and AI agents
Secure the next generation of digital interactions. Use AI-powered flows and branding to protect both human users and autonomous AI agents seamlessly.
Meet global standards with built-in compliance
Simplify adherence to GDPR, FAPI, and OIDC. WSO2 Access Manager provides the granular consent and security protocols required for highly regulated industries.
Flexible identity for every digital use case
- Passwordless login
- Adaptive multi-factor step-up authentication
- Social login
- Bot and brute force attack protection
- Out-of-the-box self service portal
- Self-service invitation-based registration
- Account linking and recovery
- Branding and internationalization
- Integration with CRM, Sales, and Marketing applications
- Data privacy compliance
- Distinct, separate tenancies per organization
- Handle complex Organizational hierarchies
- Enterprise SSO configurable per organization
- MFA and access policies are definable per organization
- Role-based application resource access control
- Delegated administration
- Branding is definable per organization
- Integration with CRM, Sales, and Marketing applications
- Frictionless access to government services
- Strong user authentication and MFA
- Robust identity proofing
- Robust Compliance and enforce security rules
- Integrate with government digital ID systems
- Fully open-source code base and open standards
- SSO for enterprise applications
- Adaptive multi-factor authentication (MFA)
- Full user lifecycle management
- Strong password management
- Data privacy and Audit compliance
- BYO directory support
- Provisioning/de-provisioning across business systems
- Fully open-source code base and open standards
- Role-based application resource access control
- Secure access to MCP Servers
- Full OAuth 2.1 support
- API authorization policies based on user consent and roles
- Financial grade API security (FAPI)
- Integrate with popular development tools for API development
- Integrate with any API gateway
- Support for JWT and opaque tokens
- In-built token exchange
- Dedicated identity for agents (Agent ID)
- Agent provisioning and lifecycle management
- Full user lifecycle management
- Agent-specific authentication
- Access control when acting autonomously vs on behalf of
- On-demand revocation of credentials
- Issue and manage auditable tokens
- Track actions with auditable trails
Built for developers
The ultimate toolkit
API-first architecture
Full capabilities accessible via secure, modern RESTful APIs for integration with any app or custom workflow.
Unmatched extensibility
Plug-in your own logic into authentication flows, leverage actions and real-time webhook events for workflow automation.
SDKs for your tech stack
Integrate quickly with React, Next.js, and more using framework-specific drop-in components, customizable styles, code samples, and quick-start guides.
Open standards
Built on OIDC, OAuth2, SAML, and SCIM open standards to prevent vendor lock-in and enable interoperability.
AI-assisted drag-and-drop
flow designer
Design user journeys with AI-assisted flows
Design secure onboarding, login (MFA and social), and account recovery journeys simply by describing requirements in plain language with AI prompts.
Pre-built templates for faster deployment
Use one-click, production-ready templates to implement strong authentication with MFA and social login, onboarding and account recovery journeys in no time.
Drag and drop, and visualize your custom user journeys
Design custom authentication with MFA and social login, onboarding, and account recovery journeys with drag-and-drop simplicity and WYSIWYG visualization.
The AI security stack:
Secure every agent action
Centralized AI agent lifecycle administration
Onboard, manage, and decommission AI agents through a central dashboard. Control agent identities just as you would for employees or customer users.
Secure authentication for sovereign AI agents
Issue agent-friendly credentials and verify AI identities using robust protocols. Ensure agents can only access your ecosystem with a verified ID.
Fine-grained authorization and task delegation
Use strict delegation policies to manage what agents can do. Ensure they act with minimum, time-bound access through dynamic user consent flows.
Comprehensive audit and forensic accountability
Maintain detailed logs that clearly distinguish agent actions from human ones. Eliminate attribution gaps for total compliance and oversight.
Policy enforcement for MCP
Secure data exchanges between agents and LLMs using MCP. Enforce granular access controls to prevent data leakage during AI-driven interactions.