Quantum-Safe IAM: Why Do You Need to Act Today?

- Sagara Gunathunga
- Head of IAM DevRel, WSO2

Quantum computing hasn't gone mainstream yet, but signs increasingly suggest that it may do so in the near future. Some researchers and industry experts estimate that we could see significant breakthroughs as early as the next decade. This anticipated shift is often referred to as Y2Q similar to Y2K that we had at the beginning of this millennium. While the timeline remains uncertain, the growing pace of research and investment in the field makes it important to start considering the practical implications now, especially in areas like cybersecurity and data protection.
That said, our hands are already full with plenty of immediate challenges. So the core question this post explores is: as developers and architects, should we already be worrying about potential implications of quantum computing, or can we afford to wait until quantum computing becomes mainstream—just as we did with AI?
Here's the short answer: quantum computing poses an immediate risk that demands our attention now. In fact, some of the things we've already done in the past may be at risk too. We should at least get started. This threat is often described with the phrase "Harvest now, decrypt later!" as Prof. Frank Leymann highlighted this in his talk at WSO2Con Barcelona 2025. Let's now take a step-by-step look at what that means—and what we can do about it.
Standing on the shoulders of giants
Our lives today are deeply entangled with digital technologies—whether or not we actively use them as individuals. From communication, banking, finance, education, and entertainment to healthcare, transportation, supply chains, work, and even our social lives, every aspect is so closely integrated with the digital world that imagining life without the Internet feels impossible. The 2024 Windows security software outage, which disrupted airlines, banks, broadcasters, healthcare providers, and retail payments, clearly demonstrated just how interconnected our lives have become with digital infrastructure.
We continue to live comfortably in this digital world because we've been assured that our data and activities are relatively safe. That sense of safety is made possible by a range of underlying systems, with foundational digital infrastructure playing a major role in delivering the security and privacy we depend on. Among these, public key infrastructure (PKI) stands out as a key enabler. It powers many of the security and privacy features we rely on in our digital applications—things like TLS, encryption, digital signatures, digital certificates, secure messaging, and cryptocurrencies. Let's take a closer look at a few algorithms used in PKI and other core security technologies to assess how safe they really are today.
- The RSA algorithm—a widely used encryption method in PKI—is based on generating two keys: a public key to encrypt data and a private key to decrypt it. Its strength comes from the computational difficulty of factoring large numbers (like a 2048-bit number) into their prime components—known to be computational infeasible. Classical computers struggle with this because of the exponential time complexity involved. For instance, factoring a 2048-bit module would take longer than the life-time of the universe—even with highly optimized algorithms and powerful supercomputers. This massive time barrier gives us peace of mind, knowing that even if encrypted data were stolen, it couldn't realistically be broken within a useful timeframe.
- The elliptic curve algorithm—another encryption method used in PKI—also follows the private-public key concept. It starts by generating a private key as a random number, and then derives the corresponding public key by combining that number with a predefined starting point on the curve. This is done through a process of repeatedly adding the point to itself. The result is a one-way function: it's easy to calculate the public key from the private key, but practically impossible to reverse the process and find the private key using classical computers, due to the complexity of the underlying math. For example, breaking a 256-bit key would take billions of years with current technology.
- The SHA-256 algorithm—a gold-standard hashing algorithm—is widely used to verify data integrity in digitally signed documents and to securely store passwords by saving the hash instead of plain text. It generates a unique 256-bit fingerprint for any input. It starts by padding the input to fit 512-bit blocks and appending the original length. Each block is split into chunks, scrambled through 64 rounds of bitwise operations, and mixed with constants derived from prime numbers. The results from all blocks are combined into the final hash. Even a tiny change in the input produces a completely different hash, making it reliable for verifying data integrity and securing passwords. Brute-forcing SHA-256 would mean trying about 2²⁵⁶ possible combinations, which would take billions of years even for supercomputers. While a collision attack—finding two inputs with the same hash—is theoretically possible, it would still require around 2¹²⁸ attempts, and no practical collisions have been found to date.
Harvest now, decrypt later!
One major challenge we're facing is that the long trusted algorithms used as fundamental building blocks of modern cryptography—like RSA, Elliptic Curve Cryptography (ECC), and SHA-256—won't hold up against the power of quantum computing. These algorithms, once considered practically unbreakable due to the limitations of classical computers, could be broken relatively easily with the capabilities quantum machines are expected to bring. And it's not just some distant sci-fi threat—we're realistically looking at quantum computing becoming mainstream within the next 10 years. Here are some estimations about the above-discussed algorithms.
- The RSA algorithm: Shor's algorithm used in quantum computing can factor integers in polynomial time, breaking RSA-2048 in days when a sufficiently powerful large-scale, error-corrected quantum computer exists.
- The Elliptic Curve algorithm: Again Shor's algorithm could break the Elliptic Curve in polynomial time potentially in hours using a sufficiently powerful large-scale, error-corrected quantum computer.
- The SHA-256 algorithm: Grover's quantum computing algorithm could reduce brute-force time to ~2¹²⁸ operations making it potential possibility.
Now, here's the real concern: even if encrypted data is secure today, it may not remain that way for long. If an attacker manages to steal encrypted data now, they might not be able to decrypt it with current classical supercomputers—or even the quantum machines we have today. But that could change rapidly as quantum computing matures. This tactic, often referred to as "harvest now, decrypt later", is exactly what it sounds like: collect sensitive data today with the intent of breaking its encryption once the technology catches up.
In other words, data that appears secure under today's cryptographic standards might eventually become vulnerable, leaving organizations exposed in the future. This looming possibility is already becoming a strong motivation for malicious actors to ramp up efforts to harvest encrypted data, anticipating the moment when quantum capabilities make it accessible.
Before we dive into how we can mitigate this risk and prepare for what's ahead, let's first take a closer look at the power of quantum computing—and how it could make previously unthinkable attacks possible.
The core concept in quantum computing is the qubit—the quantum version of a classical bit. While a classical bit is either 0 or 1, a qubit can be both at once, thanks to superposition. This means a qubit holds a weighted combination of 0 and 1, representing multiple possibilities simultaneously. As more qubits are added, computational power grows exponentially—N qubits can represent 2ᴺ states in parallel. For instance, 10 qubits can represent 1,024 states at once, allowing quantum computers to evaluate many outcomes in parallel—something classical computers can only do sequentially.
Another key principle is entanglement, where qubits become deeply linked, so the state of one instantly affects the other—no matter the distance. This connection, combined with superposition, enables massive parallelism and powers quantum computing's most promising capabilities, like drastically cutting the time to break today's cryptographic algorithms.
If you're curious to learn more, here's a great video to explore.
Quantum-safe future
This threat gave rise to an entirely new area of research focused on mathematical problems believed to be hard to solve—even with quantum computers—such as lattice-based and code-based problems. This emerging area of research is called Post-Quantum Cryptography (PQC). The goal of PQC is to develop cryptographic techniques that are secure even in the presence of powerful quantum computers. The good news is that this work is already underway. Organizations like NIST have taken the lead in standardizing quantum-safe algorithms, and open-source initiatives such as the Open Quantum Safe (OQS) project are actively working on implementing these new algorithms in usable software libraries. While quantum computers are still evolving, quantum-safe algorithms are evolving in parallel. Here are a few notable quantum-safe algorithms that have already been standardized and are considered future-ready. Among them the first two standards are based on cryptographic primitives from the CRYSTALS (Cryptographic Suite for Algebraic Lattice) project.
- FIPS 203 - Module-Lattice-Based Key-Encapsulation Mechanism Standard: This standard introduces ML-KEM, a key-exchange algorithm based on CRYSTALS-Kyber, which is designed to resist quantum attacks. It relies on the hardness of the Module Learning With Errors (MLWE) problem—basically, solving noisy equations over modular lattice structures. This mathematical problem is believed to be too difficult to solve even for quantum computers, making ML-KEM a solid candidate for secure key exchanges in a quantum future.
- FIPS 204 - Module-Lattice-Based Digital Signature Standard: This one is all about digital signatures. Based on CRYSTALS-Dilithium, the algorithm behind ML-DSA provides robust security against quantum threats. It also builds on hard lattice problems like MLWE and MSIS (Module Short Integer Solution). The standard defines three levels of security—ML-DSA-44, ML-DSA-65, and ML-DSA-87—each optimized for performance and interoperability. This makes it ideal for applications that need strong authentication, data integrity, and non-repudiation.
- FIPS 205 - Stateless Hash-Based Digital Signature Standard: This standard takes a different approach using hash-based cryptography, specifically derived from the SPHINCS+ algorithm, and is now known as SLH-DSA (Stateless Hash-Based Digital Signature Algorithm). Unlike stateful schemes, it doesn't rely on persistent state between signature operations, which simplifies implementation and reduces potential vulnerabilities. It uses strong hash functions like SHA-256 or SHA3-256 to create signatures and verify them, offering strong resistance to quantum attacks. SLH-DSA is especially valuable as a backup to lattice-based schemes like FIPS 204, providing a conservative, hash-based alternative for organizations making the shift to quantum-safe security.
However, one important point to remember is that as quantum computing advances rapidly, post-quantum cryptography is evolving too. This means you can't rely on a single set of cryptographic algorithms forever—you need the flexibility to adopt new ones as needed with minimal effort. This adaptability is known as crypto-agility. The following diagram, from a paper by Johanna Barzen and Frank Leymann at the University of Stuttgart, illustrates this concept clearly.
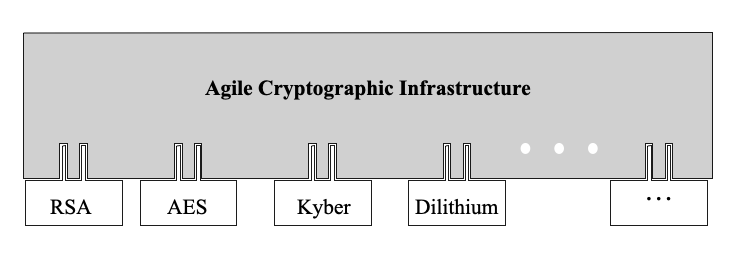
Figure 1: Plugin-based cryptographic infrastructure
It is absolutely critical to plan and achieve crypto-agility within your organizations. The Post-Quantum Security Recommendations guide published by our PQC team provides a great set of recommendations that you can follow.
Quantum-safe IAM
Quantum-safety is important for virtually every digital application you can think of, but its significance becomes absolutely critical when it comes to your Identity and Access Management (IAM) solution. IAM systems are deeply rooted in cryptography at every level. From hashing passwords and encrypting sensitive user data, to signing and encrypting security tokens, and ensuring secure communication over encrypted channels, they heavily depend on the integrity of cryptographic algorithms. Every request to and from an IAM system typically passes through a secure, encrypted channel to prevent tampering or interception.
But there's more. IAM solutions act as the gatekeeper to your entire business ecosystem. It authenticates users and manages access to your most critical business systems. That means if an attacker compromises your IAM layer, they potentially gain access to everything behind it: personal data, business logic, confidential operations. This makes IAM a high-value target in a quantum-threat world. If today's encryption becomes obsolete due to advances in quantum computing, the IAM layer could become the weakest link, putting both user privacy and the entire digital infrastructure of your business at serious risk. That's why ensuring quantum-safety as well as crypto-agility are foremost important in IAM.
We've adopted crypto-agility across our IAM product suite, which includes WSO2 Identity Server—the leader in open source identity—and Asgardeo, our public cloud identity offering. As part of this commitment, we're actively tracking advancements in Post-Quantum Cryptography (PQC) and continuously evolving our products to improve quantum safety.
The latest Identity Server 7 series, which serves as the foundation of our entire identity platform, has been architected with fundamental cryptographic improvements to support crypto-agility. This enables us to plug in new, quantum-safe algorithms as they emerge, with minimal changes with confirmation changes.
Quantum-safe TLS
WSO2 Identity Server now supports inbound quantum-safe TLS connections using the X25519MLKEM768 algorithm—a hybrid post-quantum key exchange mechanism. This combines the classical X25519 elliptic-curve Diffie-Hellman (ECDH) with the NIST-standardized ML-KEM-768 (Module-Lattice Key Encapsulation Mechanism from FIPS 203) to secure TLS 1.3 connections against quantum threats. Since ML-KEM-768 is one of the three parameter sets defined in the NIST FIPS 203 standard, this enhancement also helps you work toward FIPS 203 compliance. It enables a gradual adoption of post-quantum cryptography without requiring major architectural changes.
Most major browsers—Chrome, Firefox, and Edge—already support X25519MLKEM768, which means you can establish quantum-safe connections with WSO2 Identity Server right out of the box. If you're using Cloudflare, you're likely already benefiting from this same algorithm during TLS handshakes.
To configure WSO2 Identity Server to use X25519MLKEM768, refer to this configuration guide. The technical implantation to support quantum-safe outgoing TLS connections has already been started and will be available in future releases.
Symmetric encryption
WSO2 Identity Server uses symmetric encryption internally for a variety of tasks—like securing passwords for secondary user store connections, credentials for event publishers, and passwords and client secrets for federated authenticators.
To enhance quantum safety, WSO2 Identity Server now supports configuring AES-256, which is widely recognized as strong enough to withstand current quantum threats. We're also continuously evaluating emerging cryptographic algorithms and will be adding support for new standards as they mature.
If you want to configure AES-256 in WSO2 Identity Server, refer to the configuration guide.
We're actively working on adopting the latest quantum-safe standards published by NIST. You can stay up to date with our progress and ongoing updates here.
In addition to that, to simplify the adoption of quantum-safe features, we've built and released pre-configured WSO2 Identity Server (IS) Docker images and you can easily pull the image from DockerHub and get started right away.
Finally, this guide offers in-depth information on quantum computing and explains how WSO2 products are designed to ensure quantum safety.
Conclusion
Quantum computing, an emerging technology advancement, can also pose a serious threat to our current cryptographic standards. The "harvest now, decrypt later" tactic makes it clear that we can no longer rely solely on traditional algorithms like RSA, Elliptic Curve, and SHA-256, as they could become easily breakable in the not-so-distant future.
That's where Post-Quantum Cryptography (PQC) steps in. New standards like ML-KEM, ML-DSA, and SLH-DSA offer strong quantum-resistant alternatives. But simply switching algorithms isn't enough—we also need crypto-agility, the ability to adopt and integrate new cryptographic methods quickly and with minimal friction as the landscape evolves.
For identity and access management (IAM) systems, this combination of quantum-safety and crypto-agility is absolutely critical.
At WSO2, we're tackling this head-on with WSO2 Identity Server. We've enabled quantum-safe TLS connections, added support for AES-256 symmetric encryption, and built the system with crypto-agility at its core. By staying on top of emerging standards and integrating them into real-world solutions, we're helping organizations future-proof their identity infrastructure and safeguard their data in a post-quantum world.

