The Silent Security Problem of AI Agents: Bridging the IAM Gap

- Ayesha Dissanayaka
- Associate Director/Architect , WSO2

The increasing use of AI agents in enterprise workflows introduces new identity and security vulnerabilities that conventional identity and access management (IAM) systems are under-equipped to address. Here’s how to close the gap.
AI agents are no longer a futuristic concept. They’re booking meetings, writing emails, generating code, automating internal workflows, and making autonomous decisions on behalf of humans or systems, or on their own. But behind the excitement lies a silent security question: Are these agents acting with proper IAM?
Without effective IAM, AI agents operate as an opaque system, performing sensitive actions without necessary accountability, visibility, or protective measures.
“Who are you, and what can you do?” should be the first question we ask every AI agent.
Answering this very question is what we’ve been doing for humans for decades with traditional IAM; now it’s time to modernize our approach to include these powerful but potentially risky agents.
The risk: What happens when agents act without IAM?
AI agents operating without modern IAM can lead to:
- Unauthorized data access
- Privilege escalation
- Impersonation attacks
- Untracked actions
- Regulatory non-compliance
If this sounds like the early days of API security, it is - except the stakes are higher. Agents don’t just access or expose data. They act on it.
Imagine your customer service agent, designed to help with basic inquiries, suddenly gains access to your entire customer database, financial records, and HR systems. Without proper IAM, there's no way to track what it accessed, when, or why. We've seen real-world cases where AI systems have been compromised, This isn't theoretical - it's happening right now.
Why traditional IAM falls short
Existing user methods for authenticating and authorizing AI agents to access resources, such as embedding user credentials or utilizing API keys, introduce substantial security vulnerabilities that businesses aim to prevent. Some developers tend to represent agents as applications or service accounts. This approach works only to a point, and often does not adequately address the distinct attributes of AI agents.
Let’s say your AI assistant needs access to your email and calendar to schedule meetings. Using OAuth, you can delegate those permissions. But what happens in the logs? The agent’s actions look identical to the user’s. There’s no way to know whether the user or the agent scheduled that meeting. That’s an audit nightmare.
Even worse, if the agent misbehaves by deleting emails, sending misinformation, or accessing sensitive calendars, there's no clear audit trail, no ownership, no rollback, and no accountability. Unfortunately, AI misbehavior is not just a concept; it’s already happening. IAMfor agents is not just about authentication. It's about identity, autonomy, and auditability.
IAM for AI Agents: What must it do?
This is the paradigm shift we need: treating AI agents as first-class citizens in our identity systems. Just like we manage employee identities, we need comprehensive agent identity management. This means,
- Establish agents with unique identities: Crucial for authentication, authorization, and accountability.
- Issue revokable, agent-friendly credentials and tokens securely: Enable secure access, agent friendly communication mechanisms, and allow immediate revocation if compromised.
- Enforce agent-specific access controls: Apply the principle of least privilege at both development (defining permissions) and runtime (verifying actions).
- Log and audit every action: Maintain a meticulous, unalterable record for detecting anomalies, forensic analysis, and continuous security improvement.
How Asgardeo enables IAM for AI Agents
At WSO2, we built these capabilities into Asgardeo, our SaaS IAM platform—not as a bolt-on, but as a core feature.
With Asgardeo, teams deploying AI agents can:
- Register and manage agents as first-class identities: Asgardeo treats AI agents as distinct identities within the system, similar to human users, enabling dedicated registration, identification, and centralized control. This "first-class" treatment allows organizations to track agent activities, manage permissions, and detect anomalies, ensuring agents are independently secured entities rather than mere extensions of user identities.
- Assign roles and access levels to determine their privileges:
Granular access control, vital for minimizing attack surfaces, is managed with Asgardeo by defining roles and assigning them to AI agents. This enforces the principle of least privilege, ensuring agents only have necessary permissions, thus reducing compromise impact. For instance, a data analysis agent might have read-only access, while a financial transaction agent would have highly restricted and monitored permissions. - Issue agent-friendly credentials and authentication: Asgardeo provides mechanisms for AI agents to securely authenticate themselves and obtain credentials suitable for their operational context. This includes supporting authentication methods tailored for machine-to-machine communication over APIs, ensuring that agents can prove their identity and access resources without continuously human intervention for token bootstrapping, while maintaining strong security postures.
- Issue and manage tokens for secure communication: Asgardeo ensures secure communication for AI agents by issuing and managing secure JWT tokens. These tokens cryptographically prove an agent's identity and authorization, allowing secure access to services. And most importantly, these tokens carry delegation information of the party that delegated the permission to the agent and which agent is acting on behalf of the delegated party.
- Audit agent activity independently of user activity: Understanding who (or what) did what, when, and where is fundamental for security and compliance. Asgardeo provides independent auditing capabilities for AI agent activities. This means that every action performed by an AI agent can be loggable and can be reviewed, separate from the audit trails of human users. This independent audit trail is vital for forensic analysis, identifying suspicious patterns, and ensuring accountability.
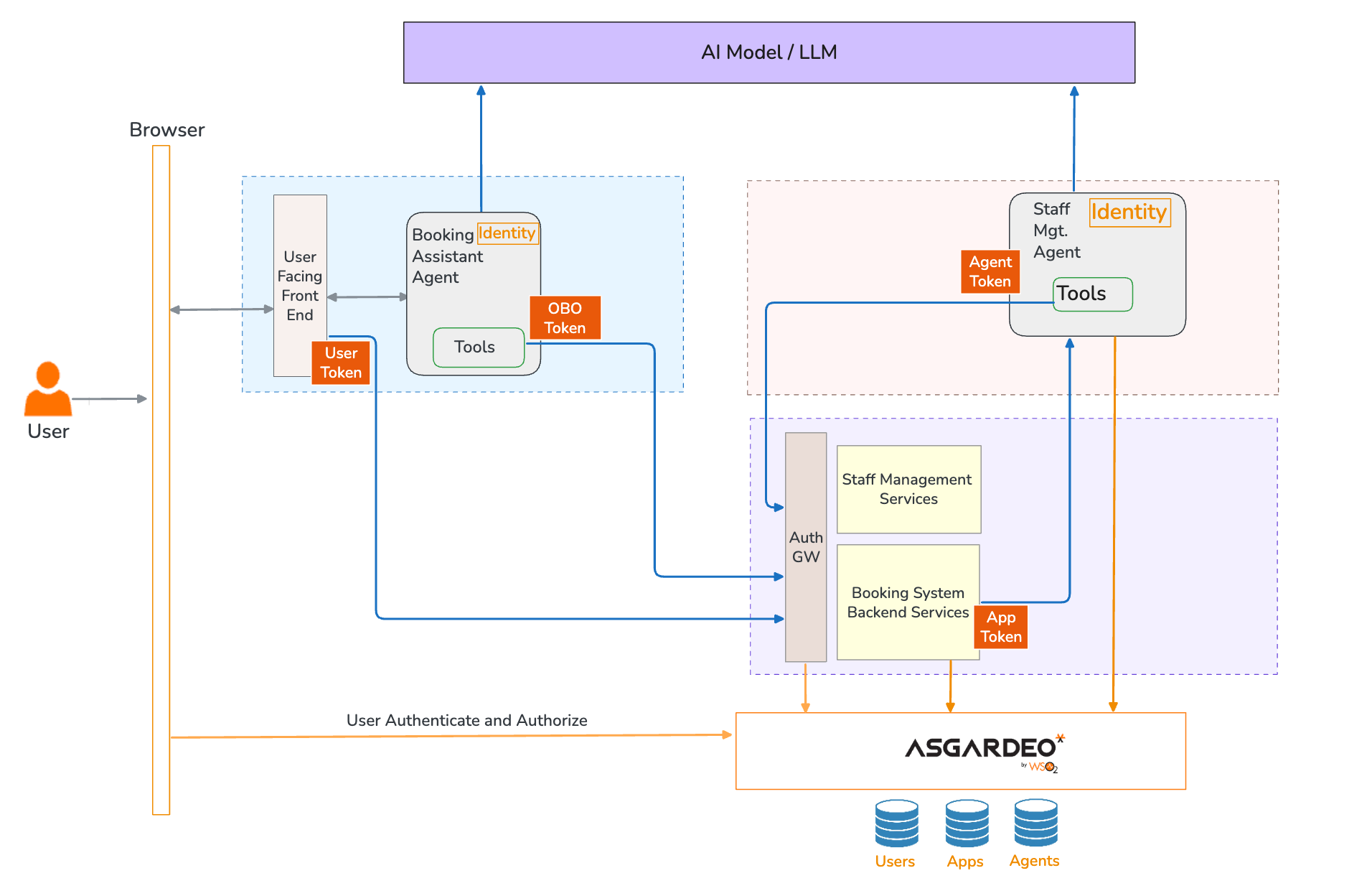
Diagram 1: Reference agent representation in a digital system of a hotel infrastructure
|
In this example, an AI hotel booking assistant can interact with various systems like availability checkers, booking engines, and payment gateways. Similarly, a staff assistant agent might access systems for concierge assignments to look up staff information and update existing bookings. Asgardeo gives each of these agents a unique identity and tailored access, so we can secure, monitor, and manage them with clear visibility, so that the agents will act within their boundaries to fulfil their purpose.
Extending proven standards with agent-aware capabilities:
Asgardeo doesn't reinvent the wheel; instead, it enhances established security standards like JWT and OAuth with "agent-aware" capabilities, customizing them for AI agents' unique needs. By building these on proven standards (SCIM 2.0, OAuth 2.0, and OIDC), we ensure interoperability, security, and maintainability while extending functionality specifically for agent-based systems. This approach allows us to leverage existing identity infrastructure while addressing the unique challenges of autonomous agent management.
Looking ahead: Identity is foundational to trustworthy AI
IAM has long been the backbone of security for humans and services. Now, it must evolve to support AI-native actors - intelligent, autonomous, unpredictable, and constantly active..
Identity needs to be priority #1, as AI becomes a first-class participant in digital systems. At WSO2, we have already launched support for AI Agents, and we are continuously improving our capabilities to support this rapidly evolving landscape. With products like Asgardeo, developers and architects can build AI-driven experiences without compromising on trust, compliance, or control.
Ready to secure your AI agents?
Learn how Asgardeo supports AI agent identity management →
Want to talk with us?
Request a demo or reach out to our team →

