Why AI Agents Need Their Own Identity: Lessons from OWASP's MCP Security Guide

- Ayesha Dissanayaka
- Associate Director/Architect , WSO2
The recently released OWASP, “A Practical Guide for Securely Using Third-Party MCP Servers,” highlights a fundamental challenge in modern AI deployments: how do we govern, secure, and audit systems that are inherently non-deterministic? Unlike traditional, static software, AI agents dynamically adapt their execution paths, tool selection, and decisions based on context and real-time resources, allowing the same agent to achieve identical goals through entirely different approaches. While the guide focuses on third-party Model Context Protocol (MCP) servers, its security principles and guidelines are equally applicable to MCP servers developed within enterprises and made available for internal agent consumption. As organizations rush to integrate AI agents into their business workflows through the MCP, enabling agents to access business resources and perform actions through tools, a critical security question emerges: who exactly is performing these actions?
This article explores why assigning unique identities to AI agents, particularly MCP Hosts, is essential, and how it addresses the non-deterministic nature of these systems while enabling the comprehensive security framework OWASP describes.
Understanding MCP: Where agents fit in the architecture
MCP has emerged as the standardization layer that enables AI models to connect seamlessly to business systems. At its core, MCP operates on a client-server architecture that consists of three main components:
- MCP Host: The AI agent runtime that manages clients and routes requests, essentially the “brain” that makes decisions. In the MCP architecture, the host represents the agent itself, making autonomous decisions about which tools to invoke and how to achieve its goals.
- MCP Client: The connector communicating with individual MCP servers.
- MCP Server: Programs exposing tools and contextual resources to agents.
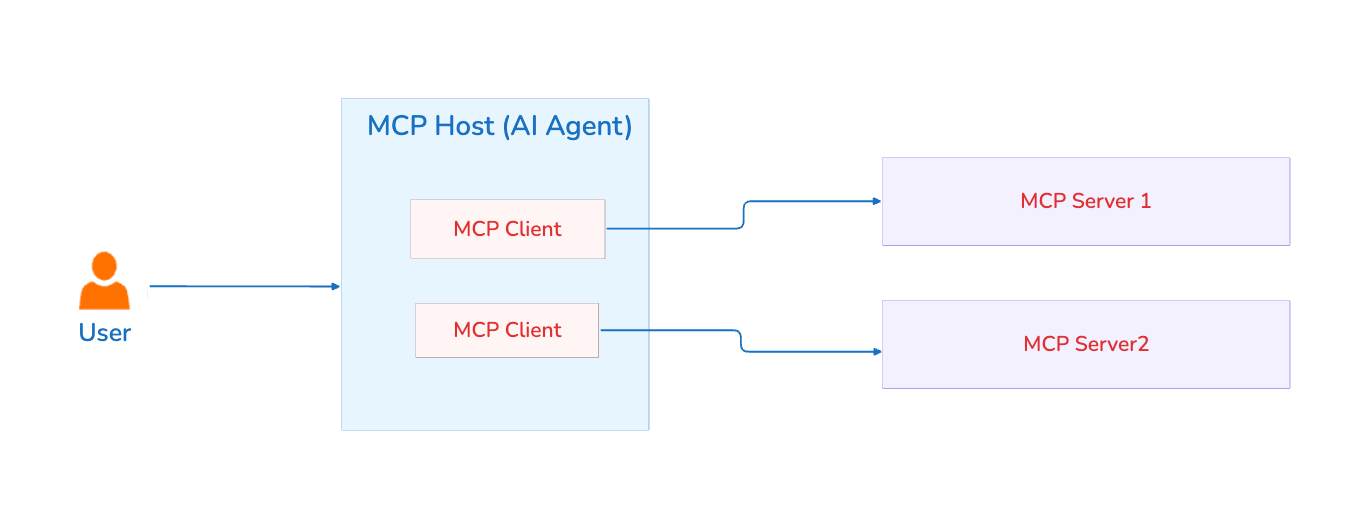
The MCP Host is the agent. It's the intelligent, decision-making entity that orchestrates tool usage, processes contextual information, and executes workflows to accomplish tasks. When we talk about agent identity, we're talking about giving the MCP Host a distinct, verifiable identity that can be tracked, authorized, and audited throughout its interactions with MCP servers.
While the MCP architecture elegantly solves the integration challenge, the OWASP guide makes clear that it introduces profound security concerns that traditional identity and access management systems weren't designed to handle.
The security challenge: Non-deterministic agents in deterministic security models
The OWASP guide addresses multiple attack vectors, including tool poisoning, prompt injection, memory poisoning, and tool interference. But underlying many of these vulnerabilities is a fundamental issue: AI agents operate differently from traditional software.
Unpredictable execution paths: When asked to perform the same task twice, an agent might take completely different routes, invoke different tools, and follow varied execution sequences.
Environmental sensitivity: Two instances of identical agent codebases can behave differently based on input phrasing, the underlying LLM, previous execution contexts, or even subtle variations in system prompts.
Goal-oriented autonomy: Rather than following predetermined workflows, agents adapt their approach based on real-time assessment of available tools and resources.
This non-deterministic behavior amplifies the security challenges OWASP identifies. Without distinct agent identities, organizations face critical questions: Which agent accessed what data? On whose authority? What tools did it invoke? Can we even distinguish between agent actions and human actions in our audit logs?
OWASP's mitigation framework: Where agent identity fits
The OWASP guide structures its security recommendations around several key areas. Agent identity serves as a foundational enabler for many of these controls:
Addressing tool poisoning and rug pull attacks
OWASP recommends monitoring tool integrity and version control, maintaining checksums to verify that tool descriptions haven't been maliciously altered. But who approved this version? Which agent is currently using it?
With distinct agent identities:
- Approval workflows can track which security reviewer and domain owner authorized each agent to use specific tool versions.
- Registry entries can link approved server versions to specific authorized agents.
- Automated alerts can trigger when an unauthorized agent attempts to connect to any MCP server.
By establishing which agent is using which tool version, organizations can implement OWASP's recommendation for monitoring tool integrity and immediately detect when a legitimate tool has been replaced with a malicious version, enabling rapid incident response before widespread compromise occurs.
Implementing runtime policy enforcement
The guide emphasizes enforcing least-privilege policies at the MCP server boundary to restrict tools from accessing sensitive resources. This requires knowing which agent is making the request:
- Agent-specific permissions can be tailored to each agent's role and function.
- Prevent over-privileging by controlling what permissions can be delegated to agents, even when acting on behalf of users.
- Policy-based controls that don't rely solely on user consent, addressing the "consent fatigue" problem.
- Context-aware authorization: Different policies for agents acting autonomously versus on behalf of users.
This directly addresses OWASP's recommendation for "Define least-permission OAuth scopes" and "Use granular permissions" by enabling policy decisions based on which agent is requesting which action on behalf of which user.
Administration: Governance workflow implementation
The OWASP guide describes a formal governance workflow with submission, scanning, review, deployment, and periodic re-validation. Agent identity enables this workflow:
- Identity dashboards show every agent alongside every approved MCP server.
- Lifecycle tracking from submission through staging, production deployment, and eventual retirement.
- Version pinning links specific agent identities to approved tool manifests.
- Probation periods can be enforced by monitoring which agents accessed which servers during staging.
- Retirement procedures systematically shut down agents and revoke access, preventing stale operations.
Without agent identities, you're tracking servers in isolation. With agent identities, you track the complete relationship between agents and the servers they're authorized to use, creating the trusted registry that forms the foundation of OWASP's governance model.
Audit: Enhanced incident detection and response
OWASP recommends monitoring for unusual tool invocation patterns such as mass file reads or excessive API calls. Agent identity transforms this from reactive to proactive:
- Baseline establishment: Each agent's normal behavior patterns can be tracked separately.
- Anomaly detection: Deviations from an agent's typical tool usage become immediately visible.
- Attribution clarity: Audit logs clearly show which agent made which decision.
- Compliance evidence: Trace actions through the complete chain: user to agent to MCP server to tool to resource.
- Forensic capability: Incident investigation can track all actions by a compromised agent.
This enables the "Incident Detection" capability OWASP describes: monitoring and alerting on unusual patterns becomes far more sophisticated when you know which agent is responsible for each pattern.
Agent ID: Implementing OWASP's framework
Agent ID capabilities directly address the security controls OWASP recommends:
- Distinct agent identities: Each agent receives a unique identity, enabling the governance workflow, registry management, and audit capabilities OWASP describes.
- Standards-based authentication and authorization: Built on the OAuth 2.1 authentication framework OWASP recommends, with native support for the MCP authorization specification, enabling seamless integration with MCP servers while enabling enhanced security controls.
- Dual-context authorization: Sophisticated access control distinguishing between agents acting autonomously and agents acting on behalf of users, exactly the two scenarios OWASP's authentication guidance addresses.
- Enterprise IAM integration: Deploys within WSO2's IAM suite, enabling unified governance across human users, traditional applications, and AI agents within the trusted registry OWASP recommends.
- Granular permissions and scopes: Implements OWASP's recommendations for least-permission OAuth scopes and action-level permissions on a per-identity basis.
These capabilities are built into both the open-source, deploy-anywhere WSO2 Identity Server and the IDaaS platform, Asgardeo.
The path forward: Agent identity as security foundation
Agent identity isn't just about authentication. It's about establishing accountability in systems that, by their nature, operate with significant autonomy. Organizations implementing OWASP's recommendations should recognize that agent identity serves as the foundation for many of these controls:
- Governance workflows require knowing which agents are approved.
- Authorization policies require distinguishing which agent is acting.
- Audit and monitoring require attributing actions to specific agents.
- Incident response requires the ability to immediately identify and disable compromised agents.
The non-deterministic nature of AI agents doesn't mean we must accept non-deterministic security. With proper identity management, purpose-built for the unique characteristics of AI agents, organizations can implement the comprehensive security framework OWASP describes while embracing the power of autonomous agents.
Agent identity is what makes this vision practical, transforming abstract security principles into enforceable policies, auditable actions, and manageable risk.
Agent ID has built-in support for the MCP authorization specification. When combined with agent identity capabilities that give a unique identity to each and every AI agent, it provides comprehensive identity and access management specifically designed for agents operating through the Model Context Protocol. Built on OAuth 2.1 and integrated with the WSO2 IAM suite, it implements the complete authentication, authorization, and governance framework outlined in OWASP's practical guide for securely using MCP servers.

