Revenue-First Open Banking: A Five-Step Blueprint for Non-Mandated Markets

- Lalaji Sureshika
- Associate Director / Architect, WSO2
Introduction
For financial institutions (FIs) operating in regions without a regulatory open banking mandate, open banking is a strategic path to generating new revenue streams through innovative, market-driven services. Progressive banks in these markets already recognize the significant value of this shift, particularly the opportunity to monetize core infrastructure through embedded finance.
This article provides a five-step universal blueprint to navigate the 'technical reference vacuum' and implement open banking to compete rather than comply. We detail the journey from defining a business strategy focused on embedded finance to establishing the security and operational frameworks required for a profitable, market-driven platform.
The strategic shift: Comply vs. compete
Banks in regulated markets often view open banking as a mandatory cost center. In contrast, banks in non-mandated markets have the freedom to treat it as a product strategy. The following table outlines the fundamental differences between an implementation driven by compliance versus one driven by competition and revenue.
| Feature | Compliance-first (regulated mandate) | Revenue-first (market-driven/compete) |
| Primary goal | Meet government/central bank deadlines and avoid penalties. | Generate new revenue streams, monetize infrastructure, and gain time-to-market advantage |
| Types of APIs | Limited to foundational Payment Initiation (PIS) and Account Information (AISP). | Advanced APIs focused on Embedded Finance (Lending, Insurance, BNPL) and "Premium" services. |
| Partner strategy | Must accept any Third-Party Provider (TPP) authorized by the regulator. | Selective partnerships with high-value platforms (e-commerce, ERPs) to grow the deposit base and customer reach. |
| Monetization | Often restricted; APIs are frequently free by mandate. | Monetized APIs, interest income from embedded loans and revenue through growth in customer base. |
| User journey | Heavy security flows dictated by rigid technical standards. | Seamless integration into non-financial customer journeys (e.g., e-commerce checkout) to reduce friction and increase customer acquisition |
The implementation journey: A five-step blueprint
To execute this revenue-first strategy, banks must navigate a specific implementation path. This snapshot outlines the five critical stages of the journey, which are detailed in the sections below.
Business strategy: Defining the monetization model and embedded finance goals.
Technical standards: Selecting global specifications to fill the local "regulatory vacuum."
Security framework: Establishing trust with financial-grade security (FAPI).
Operational framework: Managing partner onboarding and API governance.
Ecosystem maintenance: Scaling through analytics and lifecycle management.
1. Business strategy: Monetization and embedded finance
In a non-regulated market, the business strategy could focus on high-potential areas such as embedded finance, monetizing APIs, and unlocking markets through ecosystem data. This approach shifts the focus from compliance to leveraging open banking to monetize core infrastructure.
Embedded finance: The primary opportunity
Embedded finance is the seamless integration of financial services (such as payments and lending) directly into non-financial platforms like e-commerce sites, online travel booking systems, or ERP software. An open banking API infrastructure serves as the crucial enabler for this shift.
- Increasing customer lifetime value (CLV): By embedding services directly into the customer journey (e.g., offering instant credit at checkout), banks and their partners reduce friction.
- New revenue streams: This strategy unlocks new revenue streams through embedded finance use cases, such as offering instant credit via buy now, pay later (BNPL) at the point of need.
- Measuring success: When embedded APIs help merchants turn more visitors into buyers, the bank directly profits through a considerable increase in transaction fees, and scaled customer acquisition without traditional marketing costs.
Monetizing APIs: From bank to platform
Banks must shift from only serving their direct customers to becoming platform and service providers, a model often referred to as banking-as-a-service (BaaS).
Monetizing infrastructure
FIs can leverage open banking to monetize their existing core infrastructure, transforming a cost center into a profit center. Instead of keeping their regulatory licenses and payment rails closed, banks expose them via APIs so non-bank brands or neo-banks can build financial products on top of them. The bank then generates net-new revenue by charging these partners subscription fees, per-transaction API fees, or taking a revenue share of the transactions processed through the partner's app.
Consuming ecosystem data to unlock new markets
The true value of an ecosystem approach lies not just in exposing bank data outward, but in actively consuming data from third-party partners (TPPs) to expand beyond traditional banking boundaries.
- Expand the deposit base: Partner with tech platforms to seamlessly onboard customers and capture deposits far beyond the bank's traditional physical footprint.
- Unlock SME lending via TPP data: Most SMEs are unbankable due to a lack of formal, traditional credit bureau data.
- The solution: Consume real-time sales and accounting data directly from ecosystem partners (ERPs, e-commerce platforms).
- The result: Build dynamic risk-scoring models based on actual business performance, unlocking profitable lending to a previously untapped market.
2. Technical standards: Solving the reference vacuum
In the absence of a regulator to define the comprehensive technical and security frameworks, engineering teams face a "technical reference vacuum”. To build a production-ready system, these teams should ideally select a robust, globally recognized open banking standard rather than building from scratch.
A common observation across both regulated (mandated by government/central bank) and industry-led (market-driven) open banking markets is the adoption of a few core specifications by multiple countries. This adaptation of specifications can generally be sorted into several categories:
| Base specification | Functional API support | Examples of adoption or influenced jurisdictions |
| UK OBIE | Account Retrieval, Payment Initiation, Confirmation of Funds | Saudi Arabia, Hong Kong, Bahrain, Singapore, Philippines |
| Berlin XS2A | Account Retrieval, Payment Initiation, Confirmation of Funds | Europe, Russia, Maldives, Israel, Vietnam (partially) |
| Australian CDS | Account Retrieval, Payment Initiation (in the roadmap), Customer APIs | Australia, Vietnam (partially), New Zealand, UAE (partially) |
| US FDX | Account Retrieval, Payment Initiation, Tax and Payroll Data, Investment & Insurance | US, Canada |
When establishing open banking without a mandate, the strategy for functional specifications should focus on interoperability and adaptability. Since your regulator has not defined the specific data fields or payload structures, the goal is to choose a template that is widely recognized.
- Select a functional base standard: Choose a globally mature specification (e.g., UK Open Banking or Berlin Group) to provide a proven set of API structures. These provide well-documented, rich API models (e.g., how to request an account balance or a payment).
- Use case alignment: Initially, the implementation should concentrate on the core APIs necessary for the earliest market opportunities. These APIs should be chosen from the standard functional APIs detailed in the table above. For instance, the account balance retrieval API resource can be utilized for the instant credit check API in a BNPL use case. Subsequently, the bank can expand the supported APIs to accommodate additional use cases for embedded finance and monetization APIs.
- Ensure adaptability: Build the architecture with a dedicated integration layer to handle the translation between the adopted functional standard (e.g., ISO20022) and your core banking system's internal data fields and protocols.
3. Security framework: FAPI first
Security is the most resource-intensive part of an open banking implementation. When no mandate exists, the safest and most efficient starting point is to immediately adopt the global security foundation that all major mandates share: the Financial-grade API (FAPI) security profile.
- FAPI is the highly secured technical profile built on OAuth 2.0 and OpenID Connect that all leading open banking initiatives mandate for protecting high-risk financial data and payment transactions.
- By adopting the FAPI-compliant stack out-of-the-box, your bank instantly aligns with the security stance required in the most mature global markets. This makes your implementation future-proof and immediately trustworthy, allowing you to easily tune for specific regional data standards later.
- Implement comprehensive consent management and multi-factor authentication (MFA) to ensure explicit and auditable customer consent, in addition to the measures mentioned above.
4. Operational framework: Governance and partner onboarding
In an unregulated market, the bank functions as its own regulator, unilaterally determining the rules of engagement and controlling information flow. Consequently, banks typically implement processes to manage and guarantee that they are partnering with trusted external parties.
Partner vetting and onboarding
In a non-regulated market, the bank must act as its own "trust framework." Since there is no central regulatory directory, the bank is entirely responsible for deciding who gets access.
- Dual onboarding paths: The platform can support two distinct flows: Manual Client Registration (requiring human-in-the-loop approval for high-value, bespoke partnerships) and Dynamic Client Registration (automated, API-driven onboarding to scale partners).
- Identity verification: The bank must implement its own mechanisms to verify TPP identities, assess their security posture, and issue the necessary certificates before granting access.
API governance and control
- Protecting the core: An API gateway is non-negotiable for enforcing rate limits, quotas, and strict schema validation. This ensures that poorly coded TPPs (or malicious actors) cannot overload the bank's legacy backend systems.
- Commercial tiering: Move away from a one-size-fits-all approach. Implement tiered access models (e.g., Basic, Pro, Enterprise) that assign different rate limits, payload sizes, and data access levels. This is the technical foundation for monetizing "premium" API access.
5. Ecosystem operations and maintenance
Going live is just the baseline; running the platform requires active, ongoing management.
- Traffic and threat monitoring: Establish real-time visibility into API traffic to diagnose performance bottlenecks and flag abnormal request patterns that indicate fraud or aggressive data scraping.
- Commercial analytics: Track API usage not just for system uptime, but for business development. You need to know exactly which TPPs are driving volume, which APIs are most heavily consumed, and how to bill for them.
- Continuous developer experience (DX): A platform's success relies entirely on third-party adoption. The bank must treat its APIs like a product, continuously refining the developer portal, documentation, and sandbox environments to ensure integration remains frictionless and attractive to partners.
- Iterative API expansion: The initial go-live is just the MVP. The bank must actively use market feedback and commercial analytics to design and deploy new API endpoints that unlock adjacent business use cases and keep the ecosystem competitive.
- Lifecycle pruning: Actively audit and revoke access for dormant TPPs or unused client applications. Orphaned connections are a significant security vulnerability.
The reference implementation: WSO2 open banking tech stack
WSO2 Open Banking Accelerators provide a pre-configured, modular reference implementation. This significantly reduces the time and cost required to build an open banking stack from the ground up.
It includes all necessary out-of-the-box features (such as security, consent, and TPP management) on an open platform that is fully tunable. This allows technical teams to customize any feature available through accelerators, such as authentication or data mapping, ensuring flexibility for unique local needs and evolving use cases.
WSO2 Open Banking Accelerator capabilities
- Financial grade API security - The platform natively supports the OpenID FAPI security profile. This removes the heavy lifting for your engineering teams by automatically enforcing advanced security measures like Mutual TLS (mTLS) and digital signature validation.
- Customer trust and consent - Security cannot come at the expense of user experience. The WSO2 platform provides adaptive, multi-factor login flows that adjust based on risk, alongside comprehensive consent management interfaces that let customers easily control who has access to their data.
- Flexible partner onboarding - Supports both automated scaling (via API-driven dynamic client registration) and bespoke, human-approved onboarding via a developer portal, giving banks total control over who enters the ecosystem.
- API governance and tiering - Beyond just protecting backend systems with strict schema validations and rate limits, the gateway enables commercial flexibility. It allows the bank to enforce tiered access models, charging different rates based on partner use cases and enforces custom policies.
- Core banking integration - The platform serves as a critical translation layer. It mediates between modern open banking API standards and existing legacy core banking infrastructure, ensuring low-latency data flow without requiring expensive backend modernization.
- Visibility and analytics - The system integrates seamlessly with analytics platforms (e.g., Moesif ) to provide real-time intelligence on both operational health and commercial API usage.
- AI advantage - As financial ecosystems evolve, APIs will increasingly be consumed not just by traditional applications, but by autonomous AI agents. Most open banking platforms are built exclusively for human developers and traditional apps. WSO2’s distinct competitive advantage is a platform purpose-built for the developer experience and natively engineered to power the next generation of agentic banking.
- Secure AI access: The MCP Gateway securely exposes open banking endpoints as "tools" for AI agents using the Model Context Protocol (MCP), while enforcing strict rate limits.
- Data guardrails: Built-in AI guardrails provide egress control to prevent data leaks by automatically masking PII and financial secrets sent to external LLMs.
- AI-accelerated integration: AI-assisted integration (Copilot) automates complex data mapping for legacy core banking systems, reducing time-to-market.
- Identity for AI agents: The Identity Server assigns distinct, governable identities to AI agents, enforcing multi-party consent for compliant auditing of all AI-driven actions (e.g., payments).
Reference implementations for regional specifications
In addition to the accelerator layer, WSO2 provides pre-built Reference Implementations of Regional Toolkits that instantly implement the functional and security specifications of major standards, acting as the ideal "functional base standard":
- OpenBanking UK Compliance Toolkit
- Berlin Group NextGenPSD2 Compliance Toolkit
- AU CDS Compliance Toolkit
Banks adopting any of these three specifications can immediately utilize WSO2’s reference implementations. To incorporate regional requirements, organizations can leverage accelerator extension points—the same framework used to customize base open banking implementations. Technical details for these extensions are available in the official documentation.
Example application for WSO2 reference implementation
This use case demonstrates the full capability of the universal blueprint's architecture in enabling embedded finance for rapid monetization. The following diagram illustrates an instant credit check API request, essential for offerings like BNPL, and showcases the usage of WSO2's pre-configured features on complete flow at the bank side.
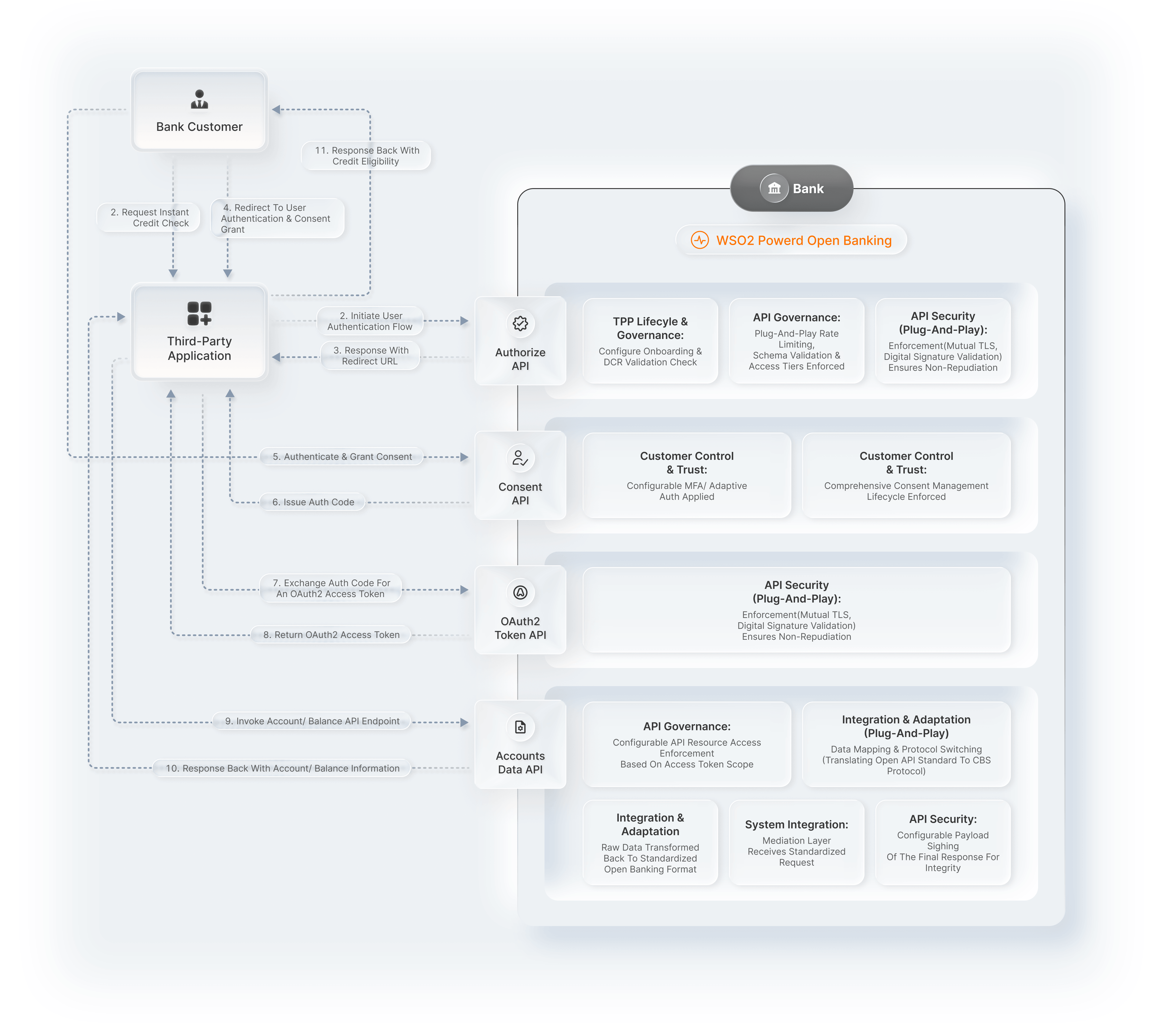
Figure 1: Leveraging WSO2 Open Banking for an Instant Credit Check API
Build your market advantage now
WSO2 Open Banking provides the essential technical blueprint and pre-built components, transforming open banking implementation from a lengthy, high-risk project into a rapid assembly and configuration exercise. It delivers the technical certainty and acceleration needed to lead the market, even without a regulatory mandate.
Ready to leverage a globally validated, market-focused open banking stack?
- Request a demo: To see how the pre-configured building blocks reduce development effort, get in touch with us here.
- Explore the reference: Review WSO2 Open Banking Accelerator documentation to understand components, overall architecture, and available functional templates.
About The Author
Lalaji Sureshika is an energetic technology enthusiast, currently working as a Software Architect and Engineering Manager at the BFSI team in WSO2. She's a key member of the WSO2 Open Banking solution team with prior key experience in the WSO2 API Manager team since both team's inception. During her stay at WSO2, she has contributed to several WSO2 products including WSO2 API Manager, WSO2 Identity Server, and WSO2 Enterprise Integrator.
She spearheaded the architectural, research, and development aspects of the WSO2 Open Banking solution which is a solution formed from combining WSO2 API Manager, WSO2 Enterprise Integrator, WSO2 Identity Server, and WSO2 Stream Processor.
She has demonstrated strong engineering professional skills in Java, WSO2 products, Apache projects, JavaServer Pages (JSP), javascript, Maven, SOAP, XML, REST, JSON , Application Programming Interfaces [API] and Identity and Access Management mechanisms including SAML2 SSO, OAuth 2.0, OpenID Connect.
She is a well versed consultant who has actively involved in designing and building solutions for WSO2 customers, including many Fortune 500 companies.

