Adding Sign In with Apple to Your App in under 5 Mins with ZERO Code

- Janak Amarasena
- Technical Lead, WSO2
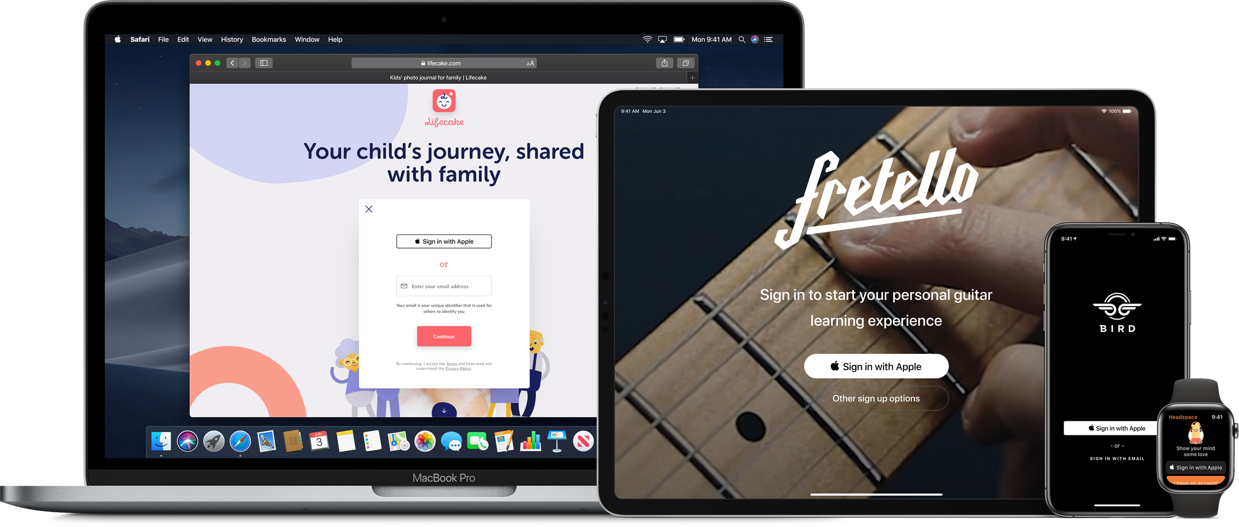
Apple recently rolled out a new feature called “Sign In with Apple” which allows users to log into apps using the user's Apple ID.
The question in most developers minds right now would be how hard will it be to integrate this into my existing app? Well if you're using WSO2 Identity Server, the answer will be…it's pretty simple! You can do this with ZERO code change and in under 5 minutes. The hard part is actually configuring everything from the Apple side (:P). The very first thing you’ll need to do is to configure Sign In with Apple using your Apple developer account. You can refer to my blog post on How to configure Sign In with Apple to quickly get started.
Then the two most important things you’re going to need to add this capability to your app is the client ID and the client secret which will be used to call Apples’ authentication service.
- client_id: The application identifier for your app.
- client_secret: A secret generated as a JSON Web Token that uses the secret key generated by the WWDR portal.
Now we are all set to add Sign In with Apple to your application.
Firstly we are going to add "Sign In with Apple” as an Identity Provider.
- Log into the carbon management console.
- On the Main tab, click on Identity > Identity Providers > Add.
- Fill in the required details in the Basic Information section.
- Expand the Federated Authenticators section and then the OAuth2/OpenID Connect Configuration form. This is where we will be adding the configurations to connect with Apples' new sign-in service.
Tick the checkbox saying Enable OAuth2/OpenIDConnect.
So here are the basic details you need to enter (if you haven’t already done the necessary configuration from within the Apple developer account, the points below might confuse you).
- Client ID: This is the Service ID of the service you created when setting up
- Client Secret: This is the JWT you created using the private key you obtained
- Authorization Endpoint URL: https://appleid.apple.com/auth/authorize
- Token Endpoint URL: https://appleid.apple.com/auth/token
- Callback URL: This will be the /commonauth endpoint of WSO2 Identity Server. You also have to add this as a Return URL when you configure Sign In with Apple when creating the Service ID.
Figure 1
Click on Register after adding the details.
Now, let's add this to your Service Provider.
- On the Main tab, click Service Providers > List > Select the service provider you have already created for your existing app.
- Click on your applications service provider.
- Expand Local & Outbound Authentication Configuration and click on the Advanced Configuration.
- Click Add Authentication Step which is under Authentication Step Configuration. Under Step 1 in Local Authenticators select basic and click Add Authenticator which is next to it (this your normal authentication method which you used previously). In Federated Authenticators select the IDP we just created and click Add Authenticator (this will add Sign In with Apple to your app). Click Update and again Update in the next screen.
Figure 2
Well, that's it! Now when you go to login from your application you will have an option to use “Sign In with Apple”.
How are you able to integrate with new technology this easily using WSO2 Identity Server? It’s because WSO2 Identity Server supports commonly used open standards. And though Apple hasn’t really mentioned it, from the looks of it the implementation of “Sign In with Apple” is done according to OIDC and OAuth2; two very commonly used open standards for authentication and authorization. So, even if another new authentication mechanism roles out tomorrow, if it's based on open standards, WSO2 Identity Server has already got you covered. You just need a simple configuration like the above to add it to your application.
If you are interested in knowing how Sign In with Apple works, read this blog post or watch this webinar on Apple Sign In: A Zero-Code Integration Approach Using WSO2 Identity Server conducted by industry experts :)



