Addressing Security Concerns with WSO2 Governance Registry Policy Store

- Eranda Sooriyabandara
- Senior Software Engineer - WSO2
Applies to
| WSO2 Governance Registry | Version 4.5.3 and above |
| WSO2 Identity Server | Version 4.1.0 and above |
| WSO2 Enterpise Service Bus | Version 4.7.0 and above |
| WSO2 Application Server | Version 5.1.0 and above |
Table of contents
- Introduction
- XACML
- Terminologies used in XACML policy enforcement
- System Architecture
- Setting up the servers
- Deploying artifacts to servers
- Sending requests
- Advantages of having Governance Registry as the policy store
Introduction
A typical service-oriented enterprise has mainly three entities in interaction; service consumers, services, and resources. To ensure system integrity and for these entities to perform appropriate actions in the SOA environment the enterprise needs to have a various types of policies that are defined and enforced. In this article, we describe how an enterprise can enforce an XACML (eXtensible access control markup language) policy using WSO2 ESB as the Policy Enforcement Point (PEP), WSO2 IS as Policy Administrative Point (PAP), Policy Information Point (PIP), and Policy Decision Point, and WSO2 Governance Registry as the Policy Retrieval Point (PRP).
We first provide a brief introduction to XACML and then we will show you how to set the servers with special configurations with the content, and finally illustrate a sample request with the expected response for an authorized user.
XACML
XACML (eXtensible Access Control Markup Language) is an XML-schema based policy language, which is used to describe fine grained access control decision request/response language. It can be used to describe the general access control requirements with the standard extension points for defining new functions, data types, combining logic, etc. as well as it allows to form a query to validate the authorization of the action and to interpret the result.
Terminologies used in XACML policy enforcement
- PEP - Stands for Policy Enforcement Point where the incoming request is received and the authorization request will be generated and sent over to the authorization engine
- PIP - Stands for Policy Information Point where information about policy elements such as attribute value and meaning, resource information used in policy, environment in which the particular policy to be evaluated
- PDP - Stands for Policy Decision Point where the authorization request is evaluated (sent by the PEP) and the decision is made whether to authorize or not. This point in general is called the authorization engine since it is the decision maker for authorization requests
- PAP - Stands for Policy Administration Point where the policy is managed
- PRP - Stands for Policy Retrieval Point where the policy is stored and retrieved by the authorization engine to evaluate against the incoming authorization request
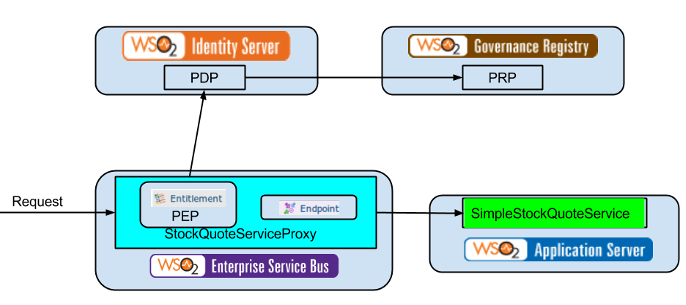
System architecture
Here, we are going to restrict users who are from other destinations apart from Sri Lanka from accessing the StockQuoteService, which is deployed in the WSO2 Application Server in the service URI https://${host}:9446/services/SimpleStockQuoteService/. In order to do this, we are going to create a proxy service in WSO2 WSO2 ESB, which is in the middle of the service and client. To carry out the authorization validation, we add an Entitlement Mediator in sequence to the proxy service, which sends the client request to the WSO2 IS. WSO2 IS validates the request against the EntitlementPolicy policy promoted to PDP, which is retrieved from WSO2 Governance Registry and acts as the PRP or policy store. After authorizing the request, it sends the request to the SimpleStockQuoteService, which is the original service, and sends the response to the client via WSO2 ESB. See the figure below.
Policy
<Policy xmlns="urn:oasis:names:tc:xacml:3.0:core:schema:wd-17" PolicyId="EntitlementPolicy" RuleCombiningAlgId="urn:oasis:names:tc:xacml:1.0:rule-combining-algorithm:first-applicable" Version="1.0">
<Target></Target>
<Rule Effect="Permit" RuleId="Rule-1">
<Target>
<AnyOf>
<AllOf>
<Match MatchId="urn:oasis:names:tc:xacml:1.0:function:string-equal">
<AttributeValue DataType="https://www.w3.org/2001/XMLSchema#string">read</AttributeValue>
<AttributeDesignator AttributeId="urn:oasis:names:tc:xacml:1.0:action:action-id" Category="urn:oasis:names:tc:xacml:3.0:attribute-category:action" DataType="https://www.w3.org/2001/XMLSchema#string" MustBePresent="true"></AttributeDesignator>
</Match>
</AllOf>
</AnyOf>
</Target>
<Condition>
<Apply FunctionId="urn:oasis:names:tc:xacml:1.0:function:any-of">
<Function FunctionId="urn:oasis:names:tc:xacml:1.0:function:string-equal"></Function>
<AttributeValue DataType="https://www.w3.org/2001/XMLSchema#string">Sri Lanka</AttributeValue>
<AttributeDesignator AttributeId="https://wso2.org/claims/country" Category="urn:oasis:names:tc:xacml:1.0:subject-category:access-subject" DataType="https://www.w3.org/2001/XMLSchema#string" MustBePresent="true"></AttributeDesignator>
</Apply>
</Condition>
</Rule>
<Rule Effect="Deny" RuleId="Deny-Rule"></Rule>
</Policy>
Setting up the servers
As mentioned in the system architecture, we need to set up the servers to ensure the system functions properly. Let's check the servers one by one.
WSO2 Enterprise Service Bus
- Set the port offset to 1 in $APPSERVER_HOME/repository/conf/carbon.xml
WSO2 Governance Registry
- Set the port offset to 2 in $APPSERVER_HOME/repository/conf/carbon.xml
WSO2 Identity Server
- Mount Governance Registry /_system/governance/trunk/policies collection to Identity Server /_system/governance/repository/identity/Entitlement/Policies collection using JDBC mount. Click here for the registry mount documentation. Note that you should not enable clustering since Identity Server and Governance Registry are not the same type of servers.
- Change the embedded LDAP userstore to JDBC userstore where WSO2 ESB and WSO2 IS both share the same userstore. Click here for documentation of setting up JDBC userstore in Identity Server
Registry mount configuration
<remoteInstance url="https://localhost:9444/registry">
<id>sharedRegistryInstance</id>
<dbConfig>sharedRegistry</dbConfig>
<readOnly>false</readOnly>
<enableCache>true</enableCache>
<registryRoot>/</registryRoot>
<cacheId>root@jdbc:mysql://localhost:3306/gregdb</cacheId>
</remoteInstance>
<mount path="/_system/governance/repository/identity/Entitlement/Policies" overwrite="true">
<instanceId>sharedRegistryInstance</instanceId>
<targetPath>/_system/governance/trunk/policies</targetPath>
</mount>
<handler class="org.wso2.carbon.identity.entitlement.policy.finder.registry.RegistryPolicyHandler">
<filter class="org.wso2.carbon.identity.entitlement.policy.finder.registry.RegistryPolicyMediaTypeMatcher">
<property name="mediaType">application/xacml-policy+xml</property>
</filter>
</handler>
WSO2 Application Server
- Set the port offset to 3 in $APPSERVER_HOME/repository/conf/carbon.xml
Deploying artifacts to servers
After setting up the servers start them with "-Dsetup" option to create new database tables. Then we need to add the artifacts which we are using as follows.
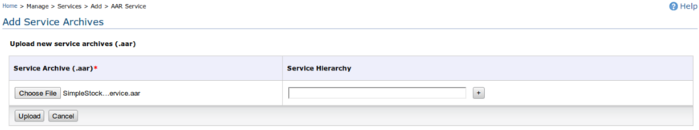
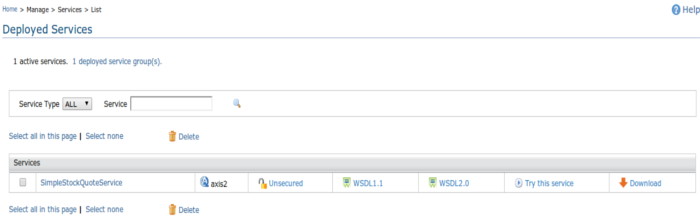
WSO2 Application Server
- Deploy SimpleStockQuoteService service
Deploying service
Deployed service list
WSO2 Governance Registry
- Add EntityPolicy using Metadata -> Add -> Policy
Adding policy

Policy list

When the policy is added from the Governance Registry it will also appear in the entitlement policy list in the Identity Server

WSO2 Identity Server
- Promote the policy to the PDP
WSO2 Enterprise Service Bus
- Create in-sequence (InSeq) as below
<sequence xmlns="http://ws.apache.org/ns/synapse"> <entitlementService remoteServiceUrl="https://localhost:9443/services" remoteServiceUserName="admin" remoteServicePassword="admin"> <onReject> <makefault version="soap11"> <code xmlns:soap11Env="https://schemas.xmlsoap.org/soap/envelope/" value="soap11Env:Server"/> <reason value="Access Denied"/> <role></role> </makefault> <log level="full"/> </onReject> <onAccept> <send> <endpoint> <address uri="https://localhost:9446/services/SimpleStockQuoteService/"/> </endpoint> </send> </onAccept> <advice/> <obligations/> </entitlementService> <header xmlns:wsse="https://docs.oasis-open.org/wss/2004/01/oasis-200401-wss-wssecurity-secext-1.0.xsd" name="wsse:Security" action="remove"/> <drop/> </sequence> - Create the out-sequence (OutSeq) as below
<sequence xmlns="http://ws.apache.org/ns/synapse"> <log/> <send/> </sequence>
- Then create a proxy service using above in-sequence and out-sequence and then apply the security with the UserNameToken. In addition we used the original StockQuoteService wsdl as the publish WSDL. Configuration will be as follows
<proxy xmlns="http://ws.apache.org/ns/synapse" name="HelloServiceProxy" transports="https" startOnLoad="true" trace="disable"> <description/> <target inSequence="gov:/trunk/sequences/InSeq" outSequence="gov:/trunk/sequences/OutSeq"/> <publishWSDL uri="https://localhost:9446/services/SimpleStockQuoteService?wsdl"/> <policy key="conf:/repository/axis2/service-groups/HelloServiceProxy/services/HelloServiceProxy/policies/UTOverTransport"/> <enableSec/> </proxy>
Now the configuration for our set up is done and we can try it out with the help of the try-it feature that is available in the ESB.
Sending requests
To send requests to the service you can use the try-it feature available in the ESB or SoapUI. Given below is a request body and the response body for a request.
Request
<proxy xmlns="http://ws.apache.org/ns/synapse"
name="HelloServiceProxy"
transports="https"
startOnLoad="true"
trace="disable">
<description/>
<target inSequence="gov:/trunk/sequences/InSeq"
outSequence="gov:/trunk/sequences/OutSeq"/>
<publishWSDL uri="https://localhost:9446/services/SimpleStockQuoteService?wsdl"/>
<policy key="conf:/repository/axis2/service-groups/HelloServiceProxy/services/HelloServiceProxy/policies/UTOverTransport"/>
<enableSec/>
</proxy>
Response
<ns:getQuoteResponse xmlns:ns="https://services.samples">
<ns:return xmlns:ax2417="https://services.samples/xsd" xmlns:xsi="https://www.w3.org/2001/XMLSchema-instance" xsi:type="ax2417:GetQuoteResponse">
<ax2417:change>3.8243969717321358</ax2417:change>
<ax2417:earnings>-9.65758378333045</ax2417:earnings>
<ax2417:high>187.22340249201966</ax2417:high>
<ax2417:last>180.0141611725195</ax2417:last>
<ax2417:lastTradeTimestamp>Wed Oct 02 01:13:00 IST 2013</ax2417:lastTradeTimestamp>
<ax2417:low>186.53537154407957</ax2417:low>
<ax2417:marketCap>5.3794621932056956E7</ax2417:marketCap>
<ax2417:name>IBM Company</ax2417:name>
<ax2417:open>-175.87263731376527</ax2417:open>
<ax2417:peRatio>23.52992659588287</ax2417:peRatio>
<ax2417:percentageChange>1.86497960046246</ax2417:percentageChange>
<ax2417:prevClose>205.06374283042015</ax2417:prevClose>
<ax2417:symbol>IBM</ax2417:symbol>
<ax2417:volume>9320</ax2417:volume>
</ns:return>
</ns:getQuoteResponse>
Advantages of having Governance Registry as the policy store
- Policy validation available
- Policies can be re-used
- Non-carbon application can access/use policies using its standard APIs (WS, Atom)
Summary
We could conclude that in order to have a complete policy governance story you need to have a policy store, the place where all your policies reside. To this end, you can leverage WSO2 Governance Registry as your policy store as it helps you to efficiently govern your policies while enabling several interfaces to access it. Going beyond policy governance, you can also use WSO2 Governance Registry to create your entire governance story to ensure a conducive environment.
References
- https://wso2.com/library/articles/2011/10/understanding-xacml-policy-language-xacml-extended-assertion-markup-langue-part-1
- https://blog.facilelogin.com/2009/06/guide-to-write-xacml-policies-in-wso2.html
- https://hasini-gunasinghe.blogspot.com/2011/12/entitlement-service-xacml-pdp-as-web.html
- https://blog.facilelogin.com/2009/05/identity-server-20-as-xacml-engine.html
- https://docs.wso2.org/display/Governance460/Remote+Instance+and+Mount+Configuration+Details
- https://docs.wso2.org/display/IS410/Internal+JDBC+User+Store+Configuration
- https://wso2.com/library/articles/2010/10/using-xacml-fine-grained-authorization-wso2-platform/
