Becoming an Agentic Enterprise with WSO2

- Rania Khalaf
- Chief AI Officer, WSO2

- Asanka Abeysinghe
- Chief Technology Officer, WSO2

- Sanjiva Weerawarana
- CEO, Chief Product Officer, WSO2
Enterprises are moving toward a new North Star: becoming an agentic enterprise. This is a multi-year shift in architecture, operations, and governance as autonomous AI agents become first-class actors in how work gets done. WSO2 provides the foundational technology fabric—agent tooling, APIs, integration, identity, and engineering foundations—to make that shift practical and safe, without lock-in. The practical question for most organizations is whether their digital infrastructure is ready for that shift.
The shift from app-centric systems to agentic systems
Systems of record remain foundational, but the enterprise is adding new “systems of context” around them: context graphs and knowledge bases. Agents act across both, with tools and policies as runtime dependencies. Most importantly, agents rely on generative AI models to reason, plan their actions, and interact. These AI models, unlike traditional software, are intrinsically probabilistic and generally work on unstructured data. Supporting such applications that interleave probabilistic and deterministic behavior requires new capabilities across the computing stack.
This shift from passive software apps to include active, autonomous agents forces a different kind of architecture conversation. In an app-centric world, enterprises could standardize around interfaces (APIs), connectivity (integration), and guardrails (identity and observability). In an agentic world, those still matter, but they are no longer sufficient. Agents and AI models introduce new actors and new pathways to action, which change how we measure and ensure quality, governance, security, and operability. Consider the case of quality: In deterministic software, a key aspect of ensuring quality is done by testing. Generative AI models also require adding “evaluations” that assess qualitative behavior where no single correct answer may exist, often done with another LLM “as a judge”. Finally, AI Agents require testing, evaluations and add the need to consider the dynamic execution logic and its side-effects. Agents that pass all traditional unit, system, and regression tests may very well fail in the wild.
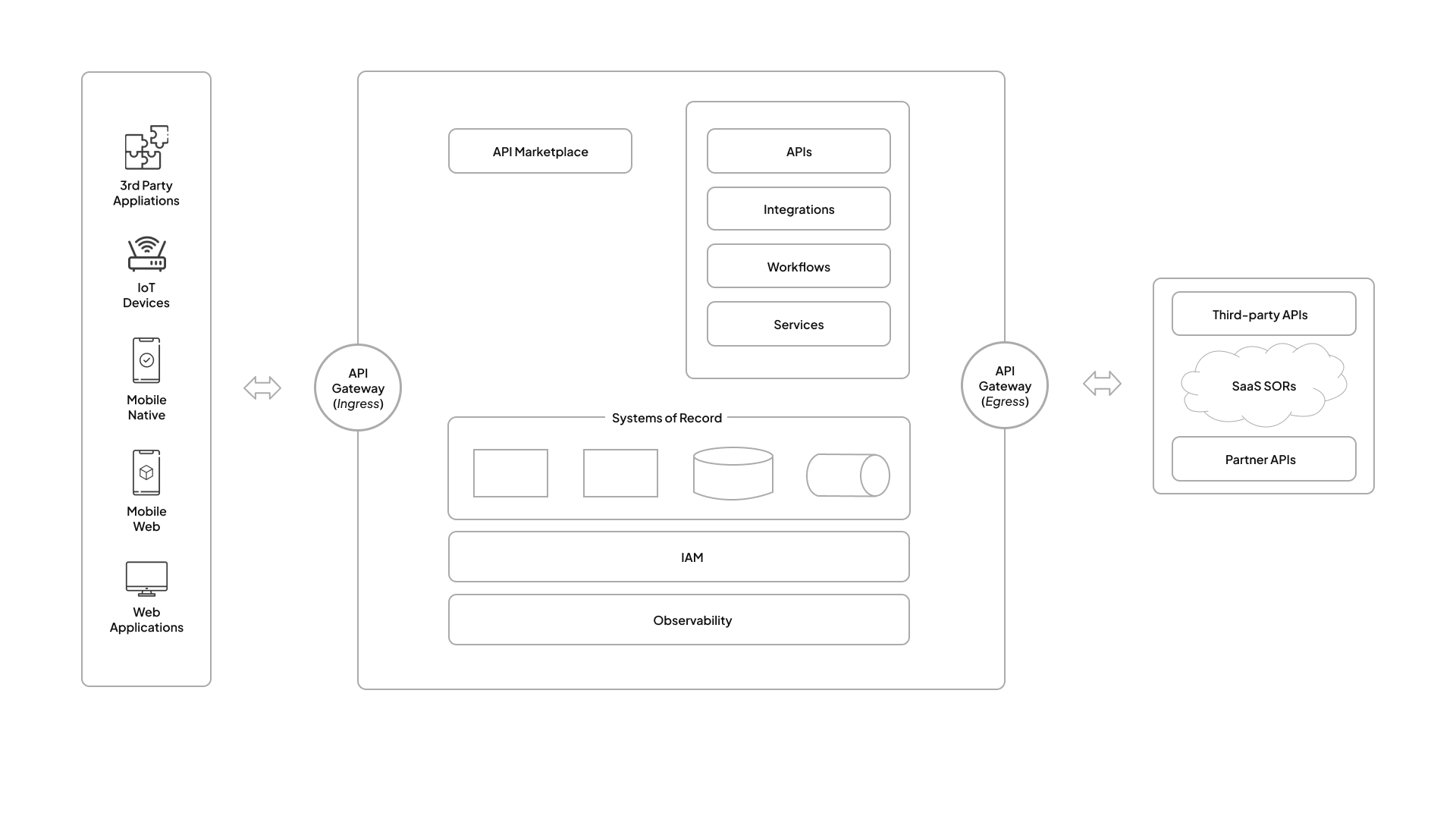
Figure 1: Non-agentic enterprise architecture
Use this diagram to anchor what “non-agentic” enterprise standardization looks like: channels on the left, ingress control, APIs/integrations/workflows/services in the middle, systems of record underneath, shared IAM/observability, and egress to third parties.
That model holds up well for systems built around apps and services. It starts to break down when you introduce AI components, which are probabilistic in nature. With agents that only answer questions or generate content, the blast radius is limited. However, for agents that call tools, chain actions, and operate with their own identity and permissions, the pre-agentic model falls apart.
Today’s enterprise architecture is agentic
Agentic systems introduce requirements that don’t exist in a purely app-centric environment. It’s worth saying plainly: agents augment existing systems with capabilities to operate autonomously but also need to use these existing systems to operate current workflows.
Agents sit within, and add new requirements for governance, security, and operability due to their combination of dynamic logic and ability to act.
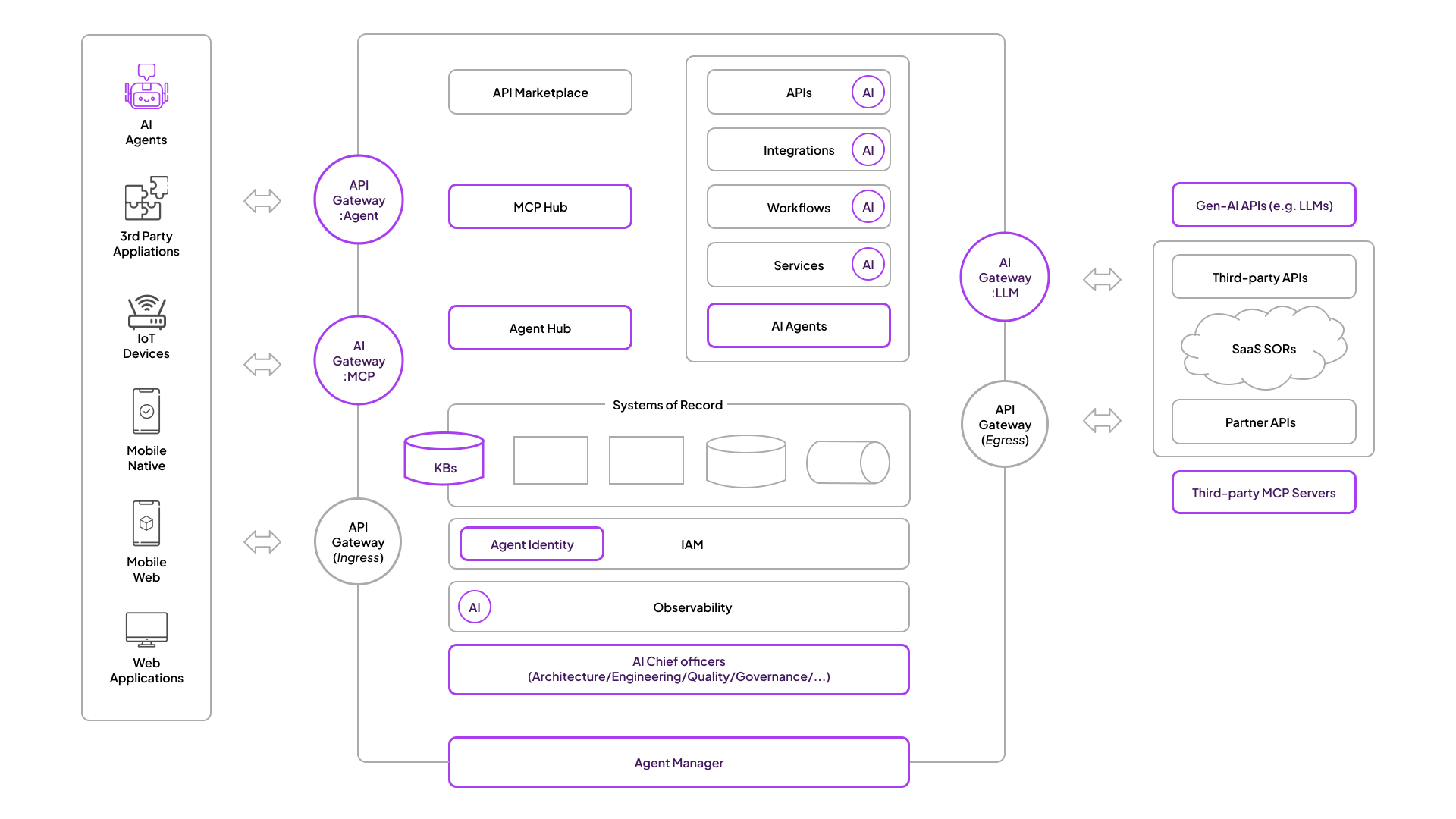
Figure 2: Today’s enterprise architecture is agentic
This diagram makes a key point: “agentic” isn’t one new box. It adds control surfaces across the architecture: ingress, hubs, identity, observability, and outbound access. The problem isn’t “can I build an agent.” The problem is “can I run agents in production across the enterprise without losing control.”
Teams across the enterprise are starting to use agents to speed up day-to-day work and reduce manual handoffs, not just in engineering. When agent-enabled tooling is built into the core technology stack as standard workflows and integrations, the productivity gains become consistent, secure, and scalable across the whole organization, instead of ad hoc and individual.
This is also why the time is now. The challenge is making agents useful, reliable, and manageable across real systems. Across enterprises, the pattern is similar: promising pilots that stall before production, inconsistent controls across teams and environments, brittle tool and data connections, limited visibility when behavior goes wrong, and lock-in decisions made too early.
The goal isn’t more AI
“Enterprises are prioritizing AI adoption and cost efficiency across the enterprise.”
The goal is not “more AI.” The goal is an architecture where agents can safely act across and within enterprise capabilities, under policy, with auditability, and with operational control.
If you take that goal seriously, it requires treating the agents, their models, tools, and knowledge graphs as first-class constructs throughout. The required capabilities are concrete:
- Controlled ingress and egress for agent and API traffic.
- A tooling layer for internal and third-party tools (hubs, MCP-style connectivity).
- Identity and policy enforcement for humans, devices, and agents - differentiating the agent from any humans it is working on behalf of.
- Observability that spans APIs, integrations, workflows, services, agents, and models.
- Testing alongside Agent/LLM evaluations.
- Guardrails that cover apps as well as Generative AI models, MCP servers, and agents.
- Deployability across cloud, on-prem, and hybrid, because this is enterprise reality.
That list is not a “feature set.” It’s the minimum viable architecture for agents that do real work inside real enterprises.
WSO2 agentic fabric for your agentic enterprise
Becoming an agentic enterprise requires more than building agents. It requires an enterprise-grade fabric that controls how agents access tools, act on systems, and operate under policy. That fabric is what WSO2 provides.
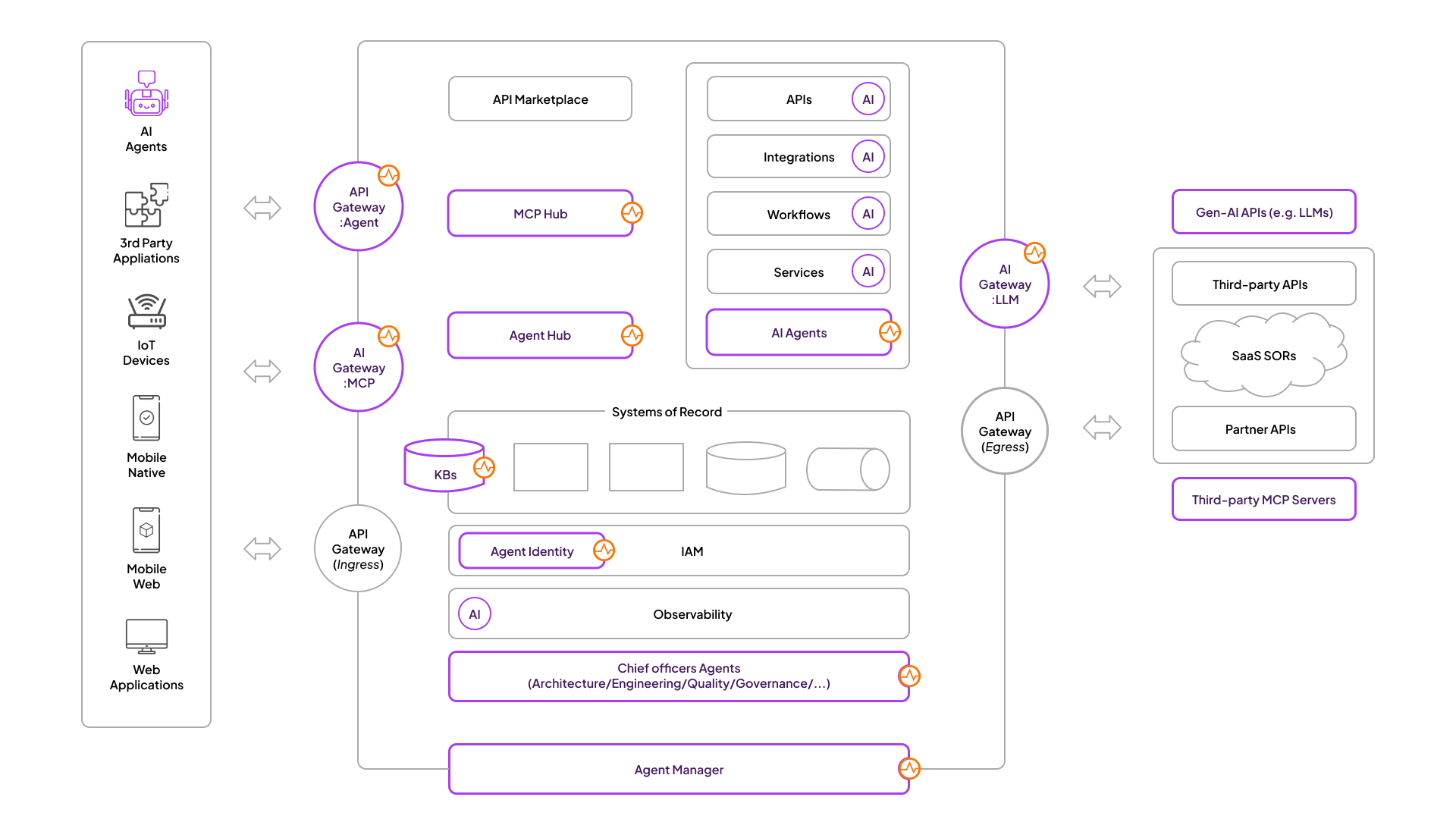
Figure 3: WSO2 agentic fabric
In practical terms, the WSO2 agentic fabric is the set of foundational capabilities that make agents safe and operable at enterprise scale, all the while taking into account the unique needs of the resulting blend of agentic (and probabilistic) and non-agentic (and likely deterministic) workloads:
- Controlled access paths: API gateway and AI gateway patterns for inbound and outbound traffic, with enforcement points you can audit.
- Tool connectivity: Hubs that expose internal capabilities and third-party tools through consistent interfaces (including MCP-style patterns).
- Identity and policy: Identity, authorization, and policy enforcement for humans, services, and agents, so actions are permitted, attributable, and reviewable.
- Integration over systems: Reliable connectivity and orchestration across systems of record, SaaS systems, and partner APIs.
- Operations and governance: Observability, guardrails, and control surfaces to run this in production, not as experiments.
This is why we describe the destination as an agentic enterprise, not “AI adoption.” The agentic enterprise is defined by controlled execution, agents that can do real work across enterprise systems, under policy, with traceability, and with operational discipline.
How we deliver
WSO2 helps you become an agentic enterprise by connecting four layers, each one building on the next. The point is simple: this maps to how enterprises actually execute change.
Strategic engagement to define your agentic strategy
At the top is strategic engagement. This is where we work with CXOs and platform leaders to define your agentic strategy, your North Star, the operating model you’re aiming for, and the constraints that matter (risk, regulation, cost, talent, time). The goal isn’t alignment for alignment’s sake. It’s to turn “agentic” from a set of pilots into a coherent, multi-year program with clear priorities and decision points.
Enterprises don’t “buy architecture.” They commit to a direction, fund programs, standardize platforms, and ship products. This engagement keeps that chain intact and provides a practical path from today’s reality to an agentic enterprise.
Platforms architects standardize on
Platforms sit above products. They’re reusable foundations that reduce fragmentation across teams and domains. At the platform layer, this becomes operational through five foundational platforms: agent, API, integration, identity, and engineering.
WSO2 Agent Platform
Operate agents in production: identity, guardrails, observability, evaluation, and lifecycle management. This is what turns pilots into repeatable systems you can scale across teams and runtimes.
WSO2 API Platform
Manage and govern the APIs, AI services, and MCP tool interfaces agents depend on. A single control plane gives consistent policy, lifecycle control, and visibility across clouds and gateways—without forcing lock-in.
WSO2 Integration Platform
Build agents and integrations that connect events, APIs, data, and systems of record with production-grade integration and orchestration. This is how agentic workloads avoid brittle point-to-point wiring.
WSO2 Identity Platform
Orchestrate identity and access for humans and agents. Centralize authentication, authorization, and policy so every human and agent action is attributable, controlled, and auditable.
WSO2 Engineering Platform
Standardize delivery for services and agents. Golden paths, CI/CD automation, and deep observability so teams ship faster with less variance and lower operational risk.
These platforms define the “how” of the enterprise: common policy, lifecycle, security, and operational controls.
This is where agentic becomes operable. Without standardization here, agents turn into a pile of isolated experiments.
WSO2, your partner for the long run
Sovereignty and choice have become ever more important. Enterprises cannot control their future if their core execution layer is locked behind someone else’s constraints. This is ultimately a decision about digital infrastructure and the operating model, not just a decision about selecting a tool. Run where you need to run. Weave into your architecture. Change when you need to change.
WSO2 ensures you control your future and core execution layer by delivering our platforms fully open source, with the same foundations in both self-hosted and SaaS deployments. As this becomes core infrastructure, you need a vendor built for the long run.
In the shift to the agentic enterprise, the stack is changing fast: new models, new tooling standards, new governance expectations, and new runtime patterns have been emerging at a breakneck pace.
As we have done time and again over the platform shifts of the last two decades, we are extracting the signal from the noise and delivering it into the WSO2 foundations—agent, API, integration, identity, and engineering platforms—so you don’t have to rebuild your core architecture every time the industry shifts. As the agentic landscape evolves, we adopt what’s real, keep what’s stable, and pass the benefits to users as durable capabilities, not one-off features.
This stems from our goal to be a forever company. We are not riding a trend or a hype curve.
“Becoming an agentic enterprise requires an adaptable architecture and a technology stack built for what’s next.”
The leaders will be the enterprises that can let agents act while keeping control—policy, identity, audit, and operational discipline—designed from day one.
If your North Star is being an agentic enterprise, build the foundation accordingly, and choose a technology partner that can evolve with you. This is what WSO2 is built for.
About the Authors
Rania has spent 25 years building AI and Cloud platforms that ship, working at the intersection of frontier AI and enterprise reality, from the multi-agent Watson Orchestrate to open source Trusted AI toolkits at IBM Research to production AI systems at a hypergrowth biotech. She currently leads WSO2's AI strategy and agent platform development.
Asanka has over 20 years of experience designing and building highly scalable distributed systems. He is the author of Cell-based Architecture and leads WSO2’s technology direction.
Sanjiva holds a PhD in Computer Science from Purdue University and previously worked at IBM Research, where he helped found IBM’s Web Services platform. He is a member of the Apache Software Foundation and received the 2022 IEEE TCSVC Research Innovation Award for contributions to web services and open source technologies.




