Securely Connecting Internal Services to WSO2 Bijira with Tailscale

- Nisan Abeywickrama
- Senior Software Engineer, WSO2

Enterprises often host their backend services within private internal networks, whether in on-premises data centers or restricted cloud environments. This setup is essential for protecting sensitive data, meeting compliance requirements, and reducing exposure to external threats. But it also introduces a major hurdle: how do you let external consumers and partners access the right APIs without opening unnecessary doors into your private infrastructure?
This challenge becomes especially pressing when using SaaS-based API platforms like Bijira, where the API gateway is hosted in the cloud rather than inside the enterprise network.
How SaaS API gateways connect to internal services and the challenges
When an API gateway is deployed inside an enterprise network, it can reach backends directly. But with SaaS-based API gateways, the gateway is hosted in the provider’s cloud and, by default, has no direct path to internal systems. To bridge this gap, enterprises typically choose one of three options:
- Public exposure – Open backend services to the internet through firewalls, NAT, or reverse proxies, restricting access with TLS, IP allowlists, or authentication. While straightforward, this increases the attack surface and complicates compliance.
- VPN tunnels – Build a site-to-site VPN between the SaaS provider and the enterprise network. This secures the channel but adds significant overhead: tunnel provisioning, certificate rotation, troubleshooting, and scaling.
- Private interconnects – Use dedicated links such as AWS Direct Connect or Azure ExpressRoute. These provide reliability and strong security but are costly, slow to provision, and inflexible for fast-moving API projects.
All three approaches work, but they carry clear drawbacks in modern environments:
- Operational burden – VPNs require constant maintenance, and interconnects mean lengthy provisioning and vendor management.
- Performance issues – VPN hubs add latency and single points of failure, while private links lack elasticity to scale with demand.
- Limited visibility – Network-level connectivity isn’t application-aware, making it difficult to enforce API-specific controls like fine-grained access, rate limiting, or auditing.
As enterprises expand across hybrid and multi-cloud environments, these trade-offs compound. What’s needed is a simpler, more secure, application-aware connectivity model designed for today’s distributed systems.
The solution in Bijira with Tailscale
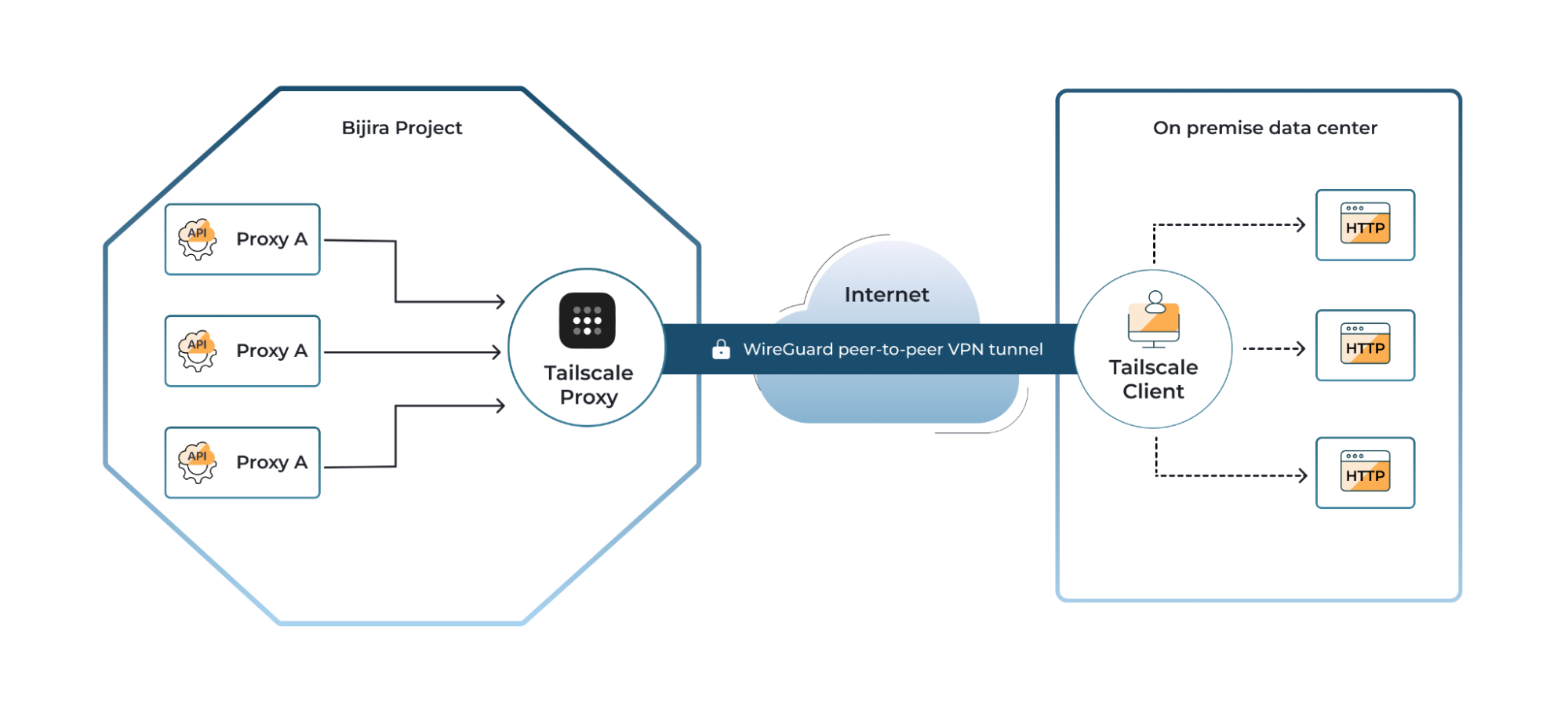
To solve the challenge of securely connecting enterprise backends to the cloud, Bijira integrates with Tailscale, a modern networking solution built for simplicity, security, and scalability through peer to peer connections. This integration allows enterprises to connect their internal systems directly to the Bijira Cloud Data Plane without the complexity and maintenance overhead of traditional VPNs.
Through these peer-to-peer connections, enterprises can grant the Bijira Cloud Data Plane secure access to their internal services, allowing API proxies in Bijira to route requests directly to internal backends. This enables Bijira to manage and monitor all traffic while keeping backend services protected, ensuring they remain secure, efficient, and fully under enterprise control.
What is Tailscale?
The Tailscale platform leverages WireGuard, an open-source, high-performance encryption protocol, to secure connections. It provides direct, end-to-end encrypted communication between devices, whether in the cloud, on premises, or behind firewalls, without relying on fixed IPs or complex routing. Connections are established automatically, traverse firewalls and NATs without special configuration, and remain resilient in dynamic cloud environments. Access is controlled based on user or device identity, ensuring that only authorized users and applications can reach sensitive enterprise systems.
This seamless integration allows enterprises to securely expose selected internal resources to the Bijira Cloud Data Plane while enabling teams to focus on delivering business value rather than managing network connectivity.
How Tailscale works with Bijira
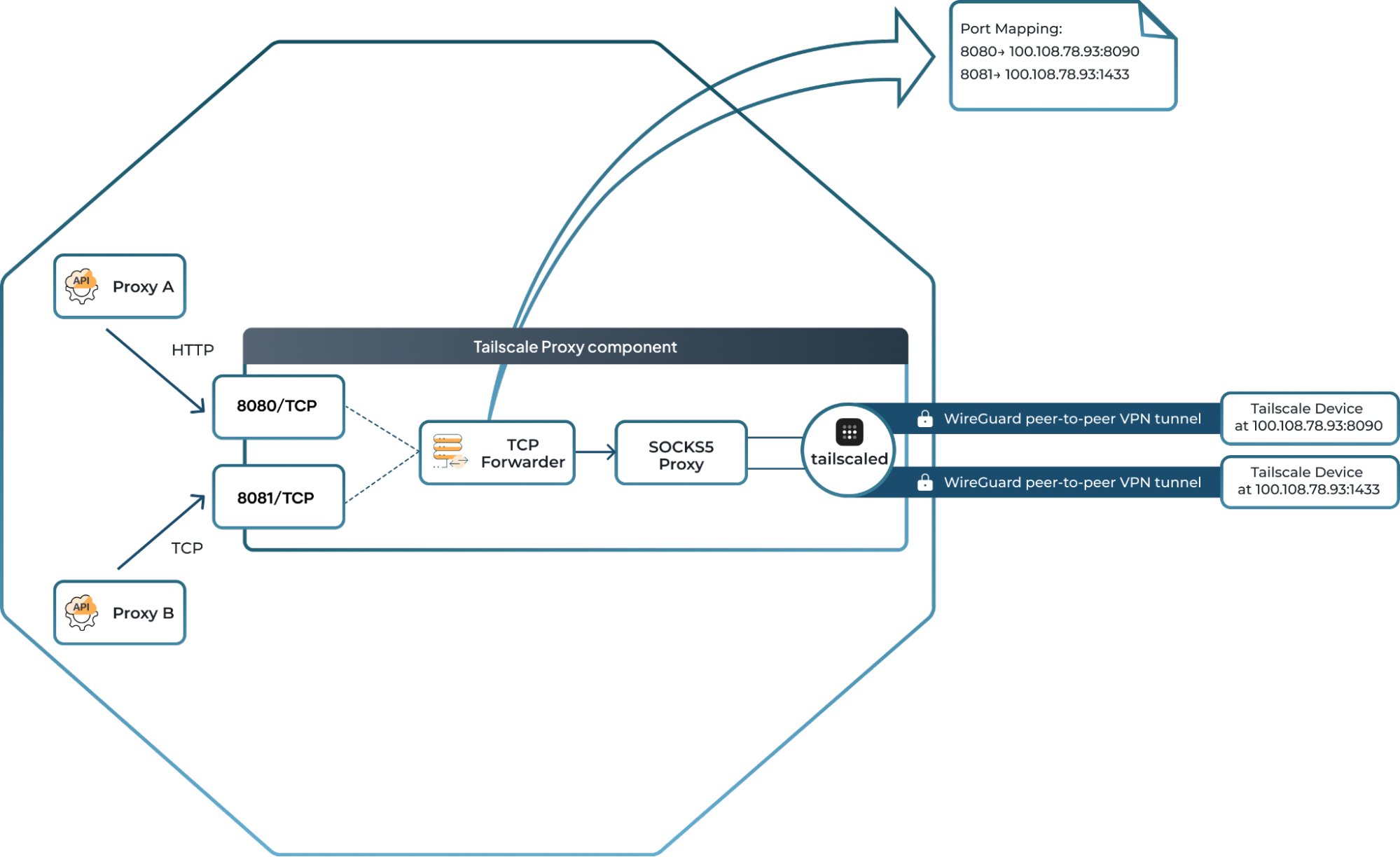
Bijira provides the capability to deploy Tailscale proxies across projects, enabling secure connections between your cloud API proxies and internal devices. This allows enterprises to expose internal services to the cloud without opening up their network or compromising security. Traffic from an API proxy deployed in Bijira is routed through a Tailscale proxy using straightforward port mappings. For example:
- An API proxy in Bijira sends requests to port 8080 on a Tailscale proxy.
- The Tailscale proxy forwards those requests to an internal device at 100.19.1.1:9000.
Once the mapping is configured, Bijira automatically directs requests from the API proxies to the appropriate internal services. All connections are encrypted end-to-end, ensuring that data remains private and secure. This approach eliminates the need for complex VPN setups or firewall reconfigurations and works reliably even as infrastructure scales or evolves. Teams can focus on building and managing APIs, while Bijira manages secure connectivity to internal systems seamlessly.
Overall benefits
- Easy connectivity – Developers can connect internal services to Bijira without worrying about manual VPN setup.
- Simple deployment – Use Bijira’s interface to quickly deploy Tailscale proxy components.
- Strong security – Identity-based access ensures only approved devices and services connect.
Get started
Bijira and Tailscale together make connecting enterprise backends to cloud APIs secure, seamless, and future-proof. To learn more and try it out, visit our documentation.

