The Future of Internet Security: Preparing for the Post-Quantum Era
The global IT security infrastructure relies on private-public key mechanisms such as RSA (Rivest-Shamir-Adleman) and ECC (Elliptic Curve Cryptography). These mechanisms face a significant threat from the development of quantum computers.
Over the next few years, quantum computers will possess sufficient computational power to break encryption based on these algorithms. For instance, while classical algorithms would require the age of the universe to factor an RSA 2048 key, a sufficiently powerful quantum computer could potentially achieve this in a matter of hours.

What is Post-Quantum Cryptography?
The global cryptography community is aware of the threats posed by quantum computers and has been engaged in addressing this challenge for years. This ongoing work has resulted in the development of novel algorithms considered "quantum-safe," as they are resistant to attacks from both known classical and quantum algorithms.
The US National Institute of Standards (NIST) has already standardized such algorithms. Open source implementations of many of such algorithms have been made available by the Post-Quantum Cryptography Alliance (a Linux Foundation project).
Organizations Need to Act now!
While large-scale quantum computers capable of breaking today’s encryption are not yet available, the implications of their arrival are too significant to ignore. Organizations that fail to act now risk being caught unprepared, facing severe data security threats and regulatory challenges.
The "Harvest Now, Decrypt Later" Threat
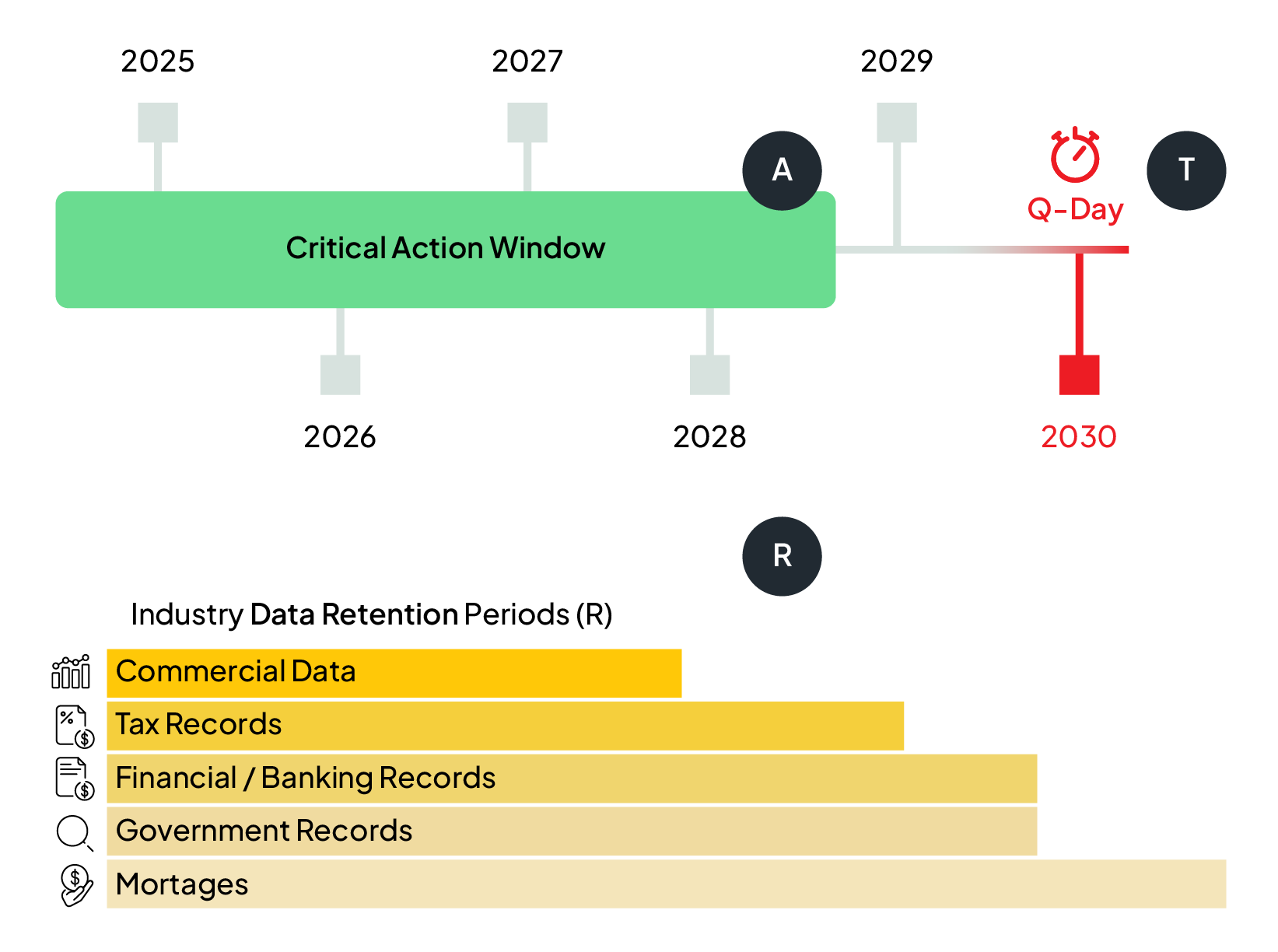
Adversaries are already collecting encrypted data today, with the intent of decrypting it once quantum computers become powerful enough. Sensitive information such as financial transactions, customer records, and intellectual property could be compromised retroactively. Organizations need to transition to post-quantum cryptography (PQC) before quantum computers render current encryption obsolete.

Long-Term Security Takes Time
Cryptographic transitions are complex and require years of planning, testing, and implementation. Enterprises cannot afford to wait until quantum computers are an imminent threat. By starting the migration process early, businesses can ensure a smooth transition, minimizing disruption while maintaining compliance with future security standards.
All industries are potentially impacted but banking, finance, healthcare and government are the most critical.
As shown below, data retention plays a crucial role. If your industry mandates long-term data storage, you must act within a limited window to encrypt that data using quantum-safe methods. Any information encrypted with RSA or ECC today will be at risk once quantum computers become capable of breaking these algorithms.
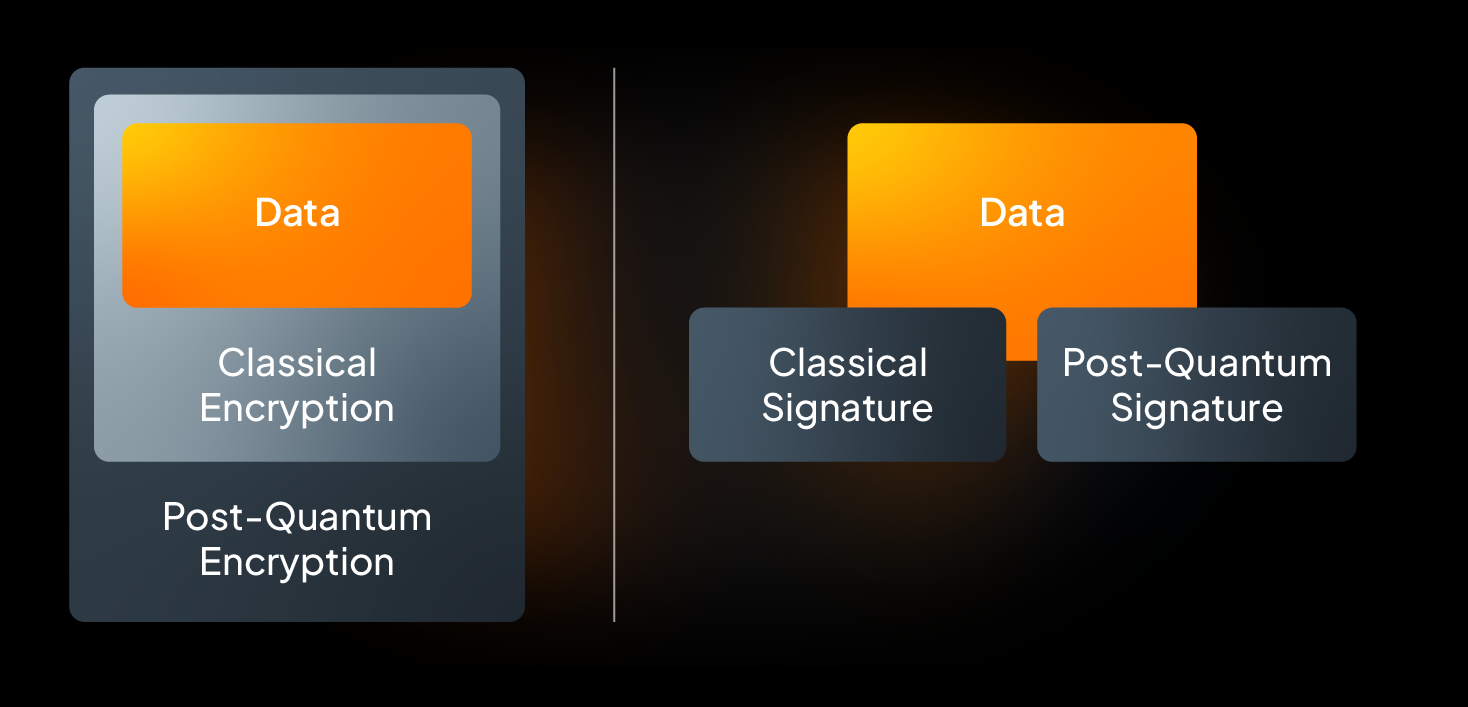
Start Now by Combining Classical and Post-Quantum Algorithms
Post-quantum algorithms (Q) are gradually gaining prominence but require time to establish trust within the industry. Therefore, combining classical (C) and post-quantum (Q) algorithms ensures resilience against classical or quantum attacks, and allows one to gain trust in the new quantum algorithms.
For example, data may be encrypted by means of a classical algorithm first and after that via a post-quantum algorithm (left part of the figure). Or data may be signed by a classical algorithm and in parallel by a post-quantum algorithm. Any other ordering of applying C and Q is fine.
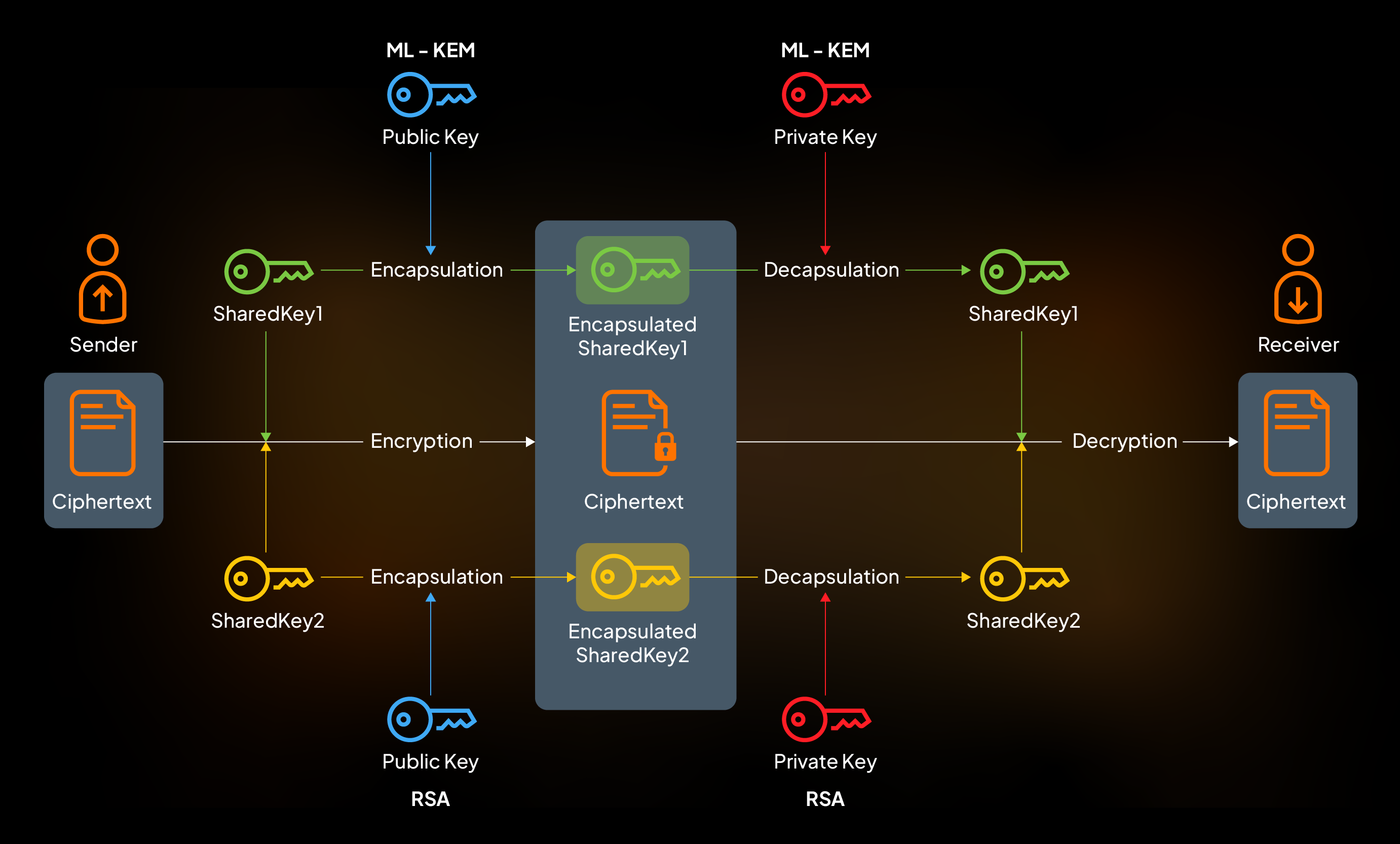
RSA-KEM-ML-KEM768-HPKE is a hybrid public key encryption algorithm (HPKE) that combines the conventional RSA-KEM with the post-quantum ML-KEM-768. It serves as a robust alternative to traditional public key encryption methods, providing protection against both traditional and post-quantum threats.
WSO2 is proactively working to ensure its products are quantum-safe:

The Ballerina language introduced support for post-quantum secure end-to-end encryption mid 2024 in Swan Lake Update 9.

The Ballerina language introduced support for post-quantum hybrid digital signatures in Swan Lake Update 9.

Ballerina also supports the post-quantum hybrid key agreement algorithm X25519MLKEM768 for TLS 1.3 since Swan Lake Update 12.
WSO2 Identity Server 7.0+ supports the post-quantum hybrid key agreement algorithm X25519MLKEM768 for TLS 1.3.
More quantum-safe features will be added across the WSO2 portfolio in the coming months.

