Asgardeo Changelog
- 17 Feb, 2026
Configurable JSON Array Format for JWT Access Token Scopes
Configurable JSON Array Format for JWT Access Token Scopes
Integrating Asgardeo with existing systems just got easier. While standard OAuth 2.0 JWT access tokens format scopes as a single, space-separated string (e.g., "scope": "read write"), some applications and downstream services (especially legacy apps or those integrated with other IdPs) strictly require scopes to be passed as a JSON array (e.g., "scope": ["read", "write"]).
To eliminate integration hurdles and custom workarounds, Asgardeo now supports configurable scope claim formats. This configuration can be applied at two levels:
- Application Level: Configure the array format for a specific application to ensure seamless compatibility with downstream services.
- Organization Level: Apply the array format globally to standardize the token structure for all applications across the organization.
(Note: Application-level configurations take precedence over organization-level settings when determining the JWT scope format for a specific application)
Documentation:
OIDC Configuration
Application Management API
- https://wso2.com/asgardeo/docs/apis/application-management/#tag/Applications/operation/createApplication
- https://wso2.com/asgardeo/docs/apis/application-management/#tag/Inbound-Protocols-OAuth-OIDC/operation/updateInboundOAuthConfiguration
Sub org Application Management API
- 12 Feb, 2026
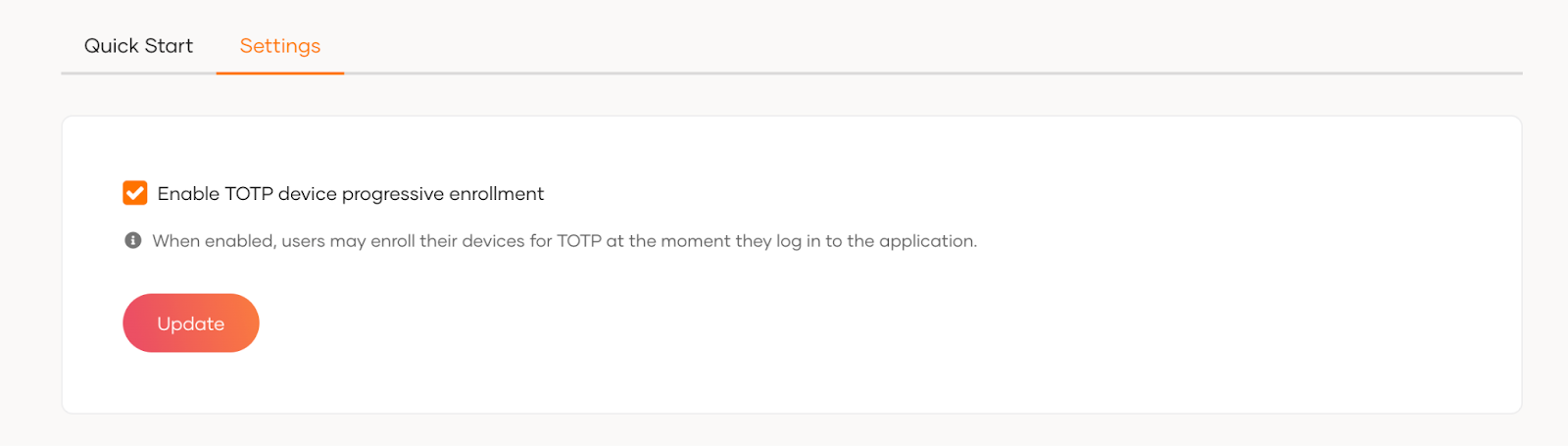
Organization level configuration to govern TOTP enrolment in the user login
We are introducing an organization level config to control TOTP (Time-based One-Time Password) enrollment during user login. This setting defines the default behavior for all applications in the organization. If needed, administrators can still override this behavior for specific applications using conditional authentication scripts. This makes it easier to manage TOTP enrollment while keeping the flexibility to customize it when required.
Documentation:
- 12 Feb, 2026
Support for Dynamic User Attributes in ID Token
WSO2 Identity Server now introduces the Pre-Issue ID Token Action, a new pre-flow extension that enables administrators and developers to execute custom logic just before an OIDC ID token is issued. Instead of relying on Java SPI extensions or server-level customizations, you can register an external HTTPS service endpoint that WSO2 Identity Server calls synchronously during the ID token issuance flow making ID token customization significantly more maintainable and decoupled from the core server.
Documentation:
- 30 Jan, 2026
Selectable Storage Locations for User Attributes
Asgardeo now gives you greater flexibility in managing where user attributes are stored. You can choose to manage specific user attributes internally within Asgardeo or store them in your connected user stores.
This enhancement provides better control over data management and residency, allowing you to configure storage at a global attribute level or tailor it for each connected user store based on your organizational needs.
Documentation:
- 20 Jan, 2026
Introducing Inheritance and Override Controls for Login & Registration Settings
We have introduced login and registration configurations inheritance for child organizations.
- Login and registration settings are now automatically inherited from parent organizations to their child organizations.
- Child organizations can override these inherited settings with custom configurations at any time.
- You can also revert overridden settings to restore the inherited defaults whenever needed.
This update simplifies configuration management across organizations, ensures consistency for child organizations, and provides flexibility to customize settings where necessary.
Documentation:
- 15 Jan, 2026
Inheritance of Custom Attributes and OIDC Scopes
We have simplified organization management by enabling child organizations to automatically inherit custom attributes and OIDC scopes from the root organization.
Previously, these resources had to be explicitly shared via B2B SaaS applications. With this update, inheritance is automatic, reducing configuration time and eliminating the need for manual sharing steps when setting up new child organizations.
Documentation:
- 20 Dec, 2025
Support custom console roles in Asgardeo
Asgardeo now allows organization administrators to define custom console roles with granular permissions for their intended management operations within the console application.
Documentation:
- 15 Dec, 2025
Enable UI-based OAuth2 application creation and authorization code grant support for sub-organizations
OAuth2 applications can now be created in sub-organizations using the Asgardeo Console UI. In addition to the existing password, refresh token, and client credentials grants, sub-organization applications now support the authorization_code grant.
Documentation:
- 16 Oct, 2025
Version Support for Action (Service Extension)
We are introducing version support for actions, allowing clear version boundaries and controlled upgrades. This ensures that existing service extensions can continue to operate safely within their current major version without any breaking changes. Administrators now have the ability to upgrade to the latest major version to take advantage of new features and enhanced capabilities, providing greater flexibility and control over service evolution.
Documentation:
- 15 Oct, 2025
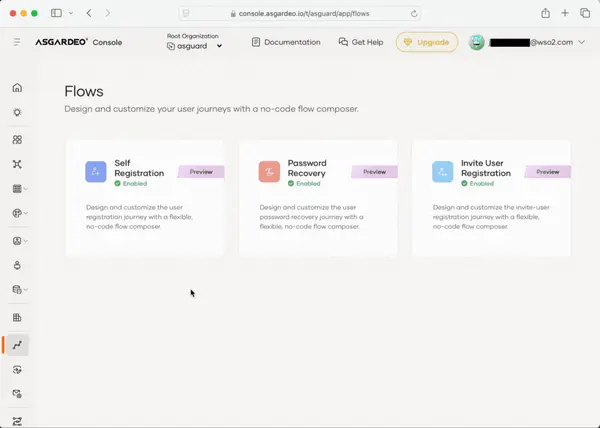
Expanding Flow Orchestration Capabilities: Password Recovery and Invited User Registration
We are extending the AI-powered Registration Flow Builder with support for Password Recovery and Invited User Registration flows in Asgardeo. These new capabilities allow you to design consistent, secure, and customizable user journeys. Administrators can now use the Flow Builder to visually create and manage recovery and invitation flows, integrate steps such as OTP, email verification, and CAPTCHA, and enforce organization specific logic without complex development effort. This enhancement provides a unified way to build onboarding and account recovery with improved flexibility, usability, and security.
Documentation:
- 10 Oct, 2025
Unicode character support for user attributes
We have added full Unicode support to user attributes in Asgardeo. Administrators and end-users can now use non-ASCII characters (e.g., Chinese, Arabic, emojis) in user profile attributes such as names and addresses.
- 11 Sep, 2025
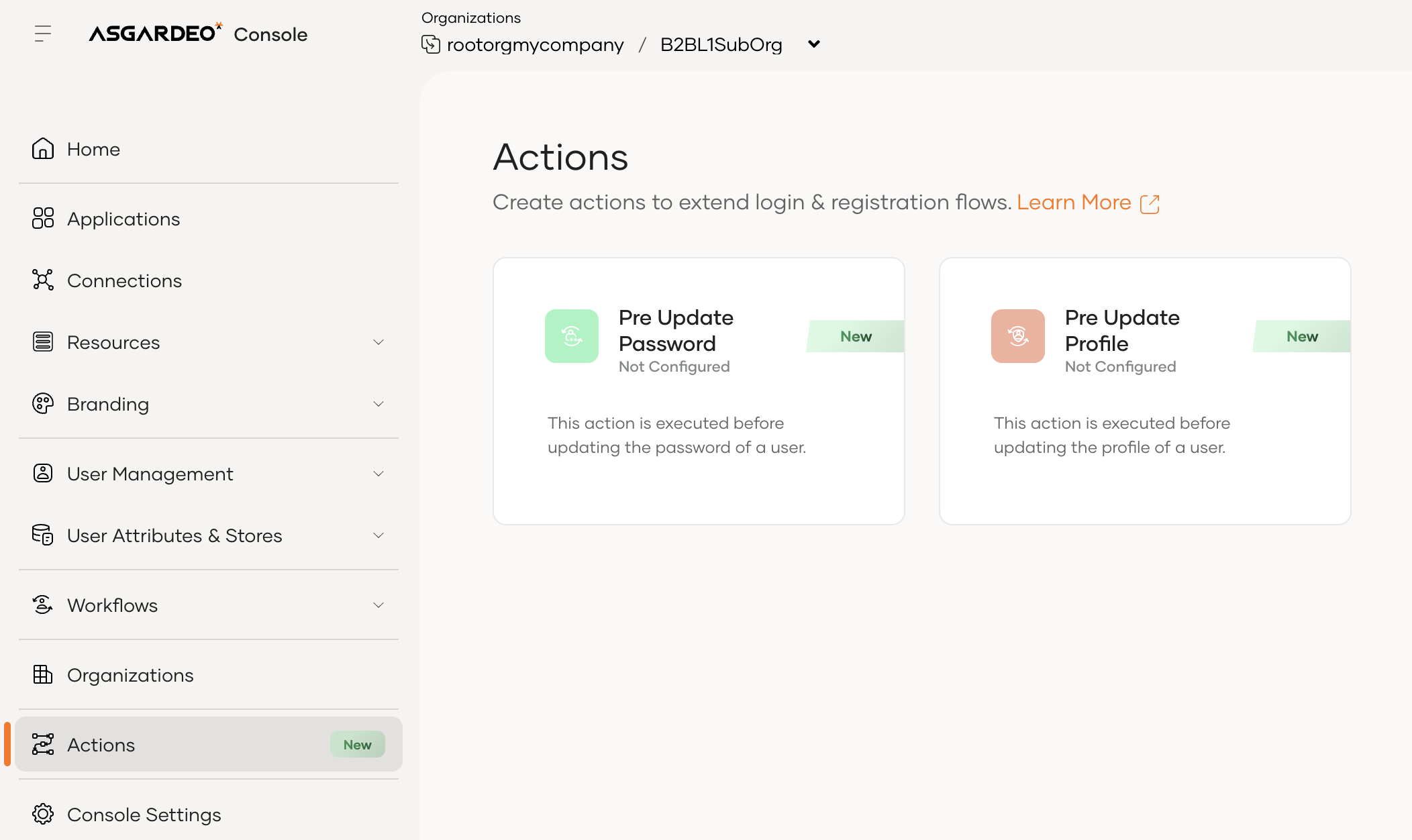
Configuring actions (service extensions) at sub organizations
Asgardeo now supports configuring Pre-Update Password and Pre-Update Profile Actions at the sub-organization level.
Previously, these configurations were only supported at the root organization level. This enhancement enables better flexibility and customization across organizational hierarchies.
Documentation:
- 11 Sep, 2025
Actions enriched with organizational context
We have enhanced the Pre-Update Password, Pre-Update Profile actions to provide richer organization context in the request payload when communicating with external services.
These now includes,
- User’s organization – the organization the authenticated user belongs to.
- Execution organization – the organization under which the action is executed.
With this enhancement, external services can make more contextual, organization-aware decisions during actions, enabling advanced B2B SaaS scenarios.
Documentation:
- 11 Sep, 2025
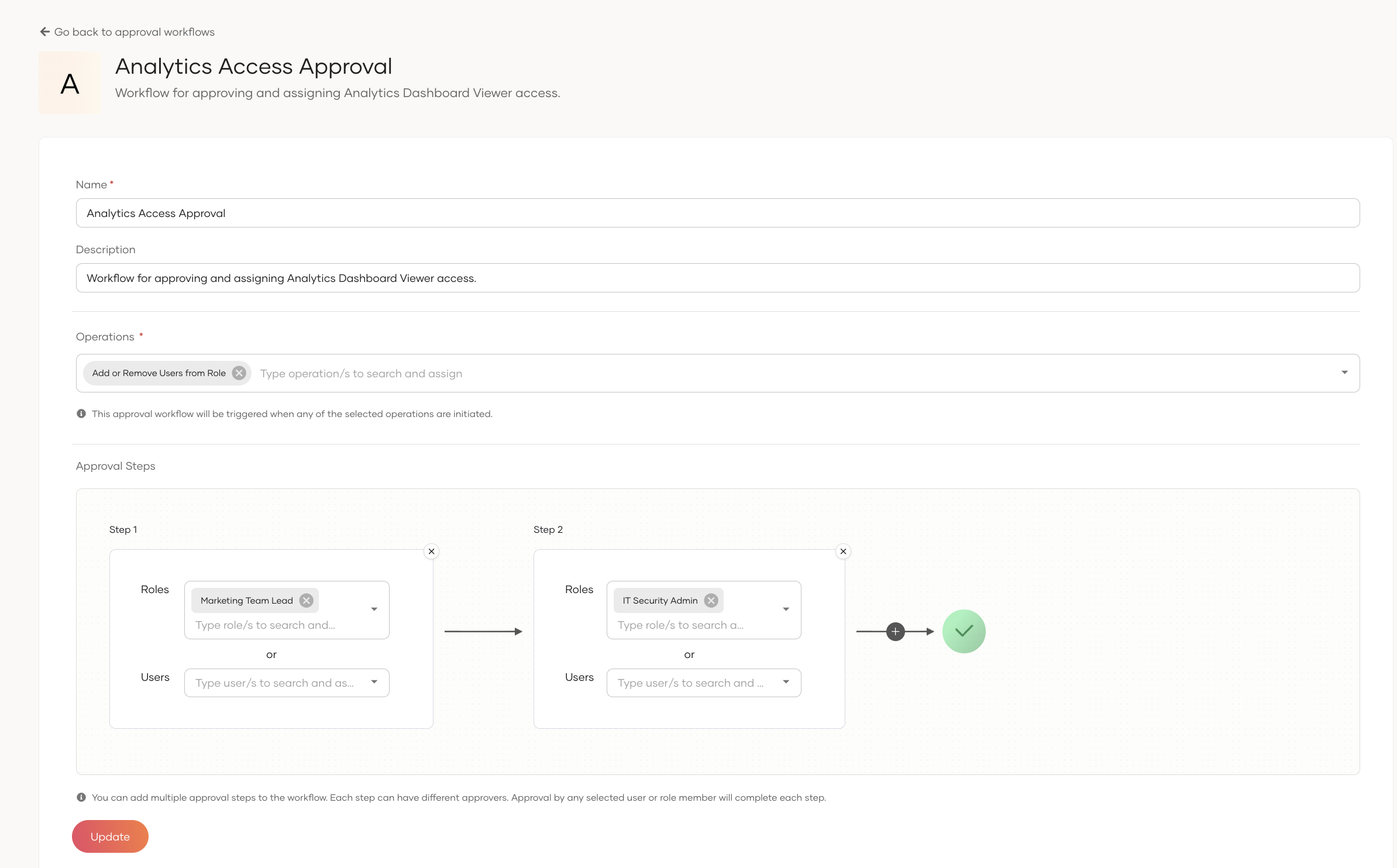
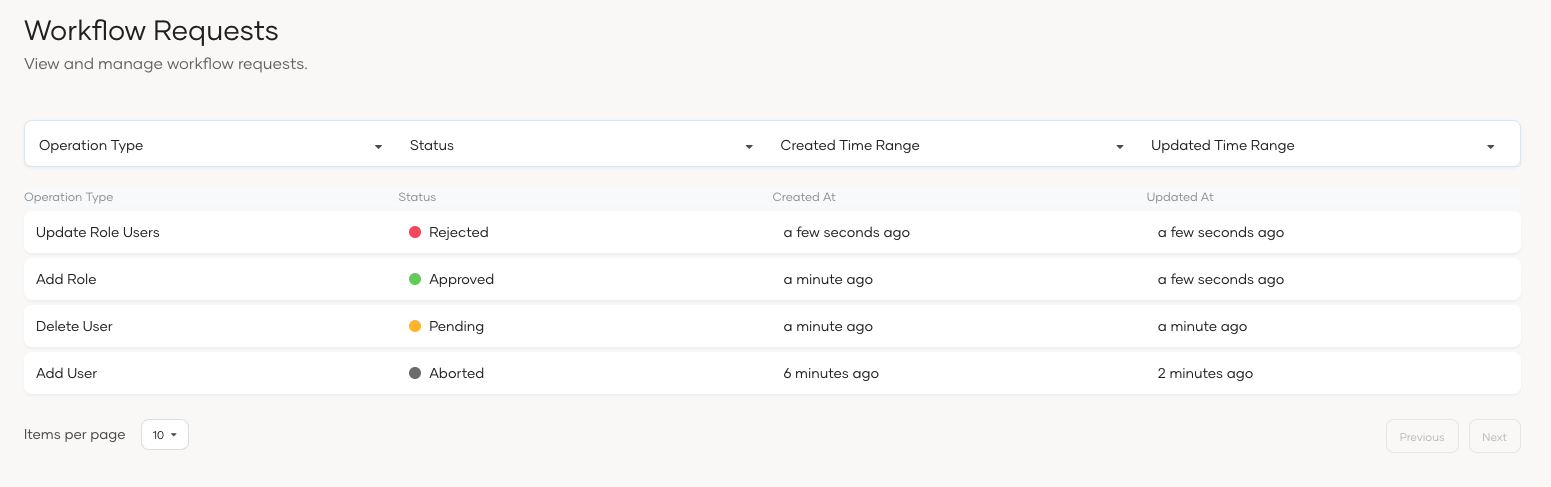
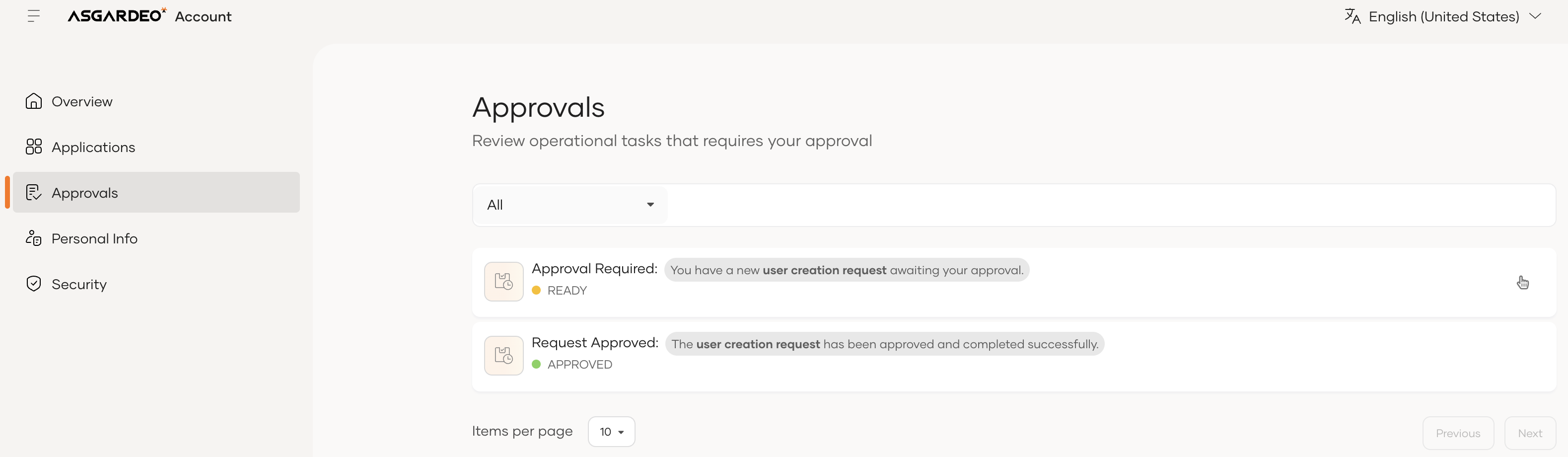
Introducing Workflow Approval Support for User and Role Management
The new workflow approval support empowers organizations to enforce approval processes for critical user and role management operations. With this enhancement, approvals can now be required for key actions such as adding users, deleting users, creating roles, and updating role assignments—ensuring greater control and compliance in identity management.
Workflows can include multiple approval steps, and approvers can be assigned either as individual users or based on roles, providing flexibility to align with organizational governance policies.
Administrators can easily configure and manage these workflows through the Admin Console, while users can seamlessly participate in the approval process via My Account. This feature strengthens governance, enhances accountability, and improves the overall security posture of identity operations.
Documentation:
- 20 Aug, 2025
Attribute-Driven Account Linking with Custom Provisioning Controls
We’ve enhanced account linking functionality to provide greater flexibility and control. Administrators can now define any attribute beyond just username or email as the lookup attribute for linking accounts. In addition, provisioning behavior during account linking failures is fully configurable.
Documentation:
- 20 Aug, 2025
Enhanced Organization Search in Console with Nested Hierarchy Support
We’ve introduced a nested-level organization search option in the Console.
Previously, searches were limited to immediate child organizations. With this enhancement, you can now search across the entire organization hierarchy, making it easier to locate and manage organizations at any depth.
Documentation:
- 20 Aug, 2025
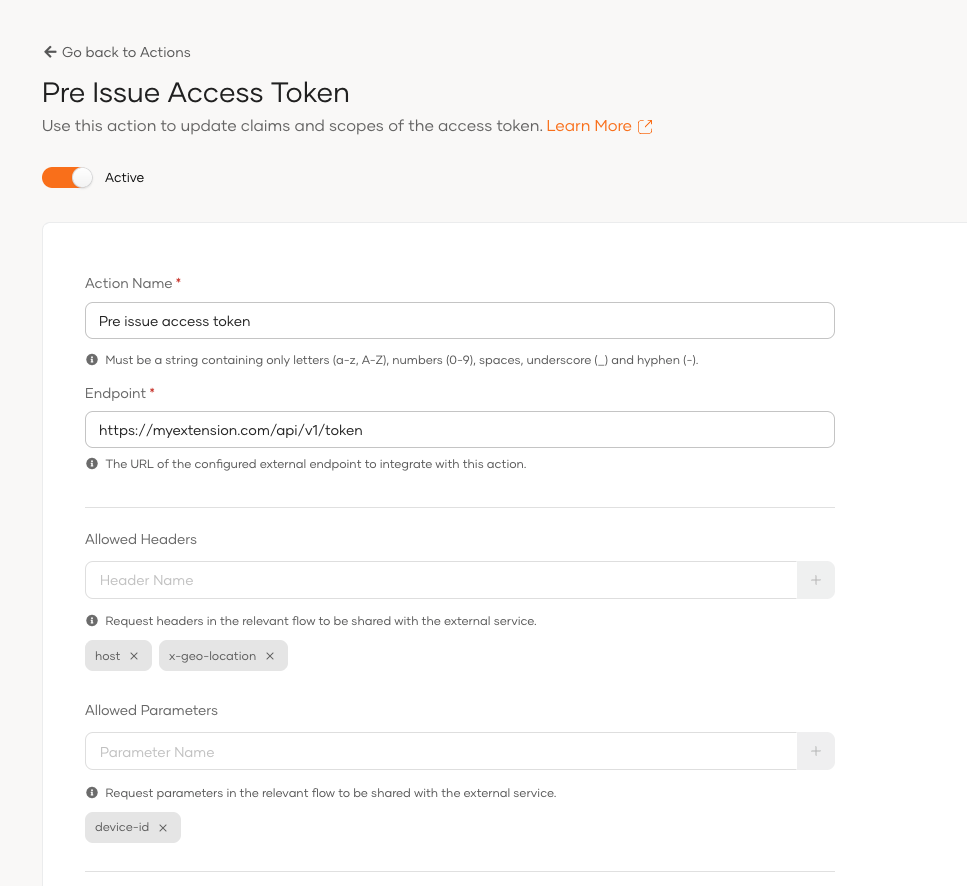
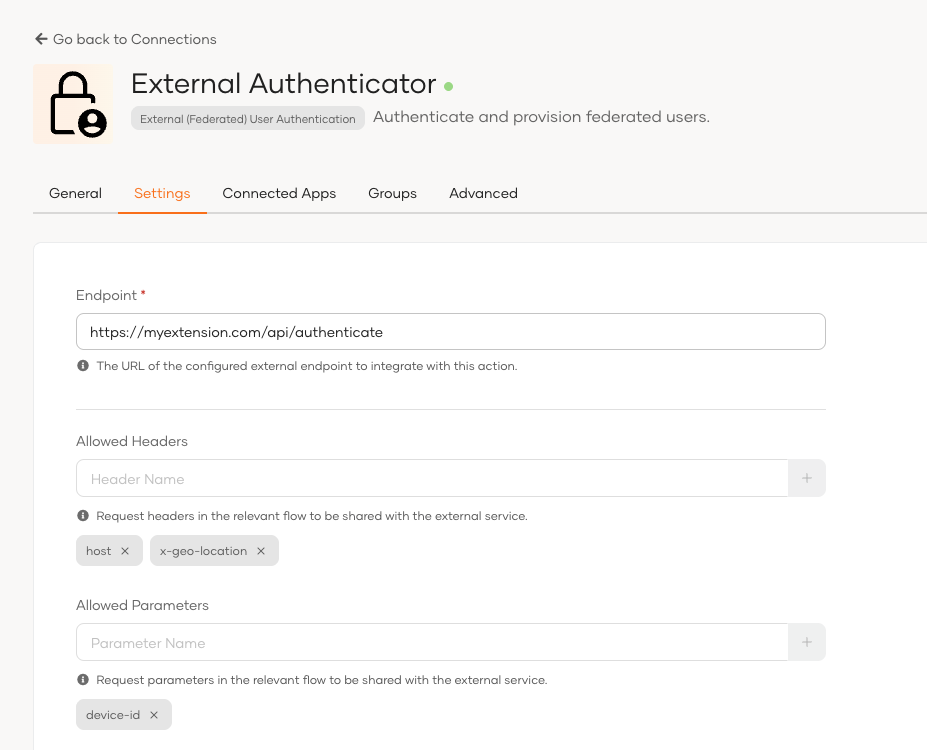
Configure Allowed headers and parameters to be shared with Pre-Issue Access Token extension and Custom Authenticator (Service-based)
In extension points such as Pre-Issue Access Token and Custom Authenticator actions, it is common to rely on additional headers and parameters from the request flow. However, allowing unrestricted access to all headers and parameters poses security risks, as they may contain sensitive information, personally identifiable data (PII), or internal infrastructure details.
Now the extension developers can explicitly select which headers and parameters should be shared with the extension, in addition to the safeguards already applied at the server level. This ensures extensions get the required data while maintaining strong security controls.
Documentation:
- 20 Aug, 2025
Selective role sharing for sub organizations
Asgardeo now provides full control over which roles are shared when delegating applications to sub organizations.Previously, application sharing automatically granted all associated application roles to sub organizations, which could lead to over-permissive access.
With this update, admins can fine-tune role visibility using one of three sharing modes:
- Share all roles with all organizations – Previous "everything shared" model.
- Share a common set of roles with all organizations – Pick a single set of roles that will be shared everywhere.
- Share different roles with each organization – Customize role sharing per sub-org for maximum flexibility.
The new experience is available for both console and general applications, with tailored UI in the "Shared Access" settings. Role selection is fully integrated into the sharing workflow, allowing admins to see at a glance which roles are shared where and adjust them instantly, while preserving the organizational hierarchy. This empowers tenant admins, B2B customers, and security teams to enforce least-privilege access, improve governance, and prevent unintended role propagation across complex organizational structures
Documentation:
- 20 Aug, 2025
Efficient Multi-User Account Linking via Bulk API
To simplify user management, we’ve introduced a new account linking bulk API. This feature allows administrators to perform multiple account linking actions in a single call, significantly reducing repetitive effort, improving efficiency during migrations and onboarding.
Documentation:
- 09 Jul, 2025
Improved User Impersonation
Asgardeo now supports initiating user impersonation without requiring changes to business applications. Previously, impersonation could only be started through a client application that was explicitly configured to allow impersonation, and this required modifying the application’s source code to integrate the feature. With this update, impersonation can instead be initiated directly from the Console application, after which users can seamlessly access any business application that has been registered in Asgardeo with impersonation enabled. This enhancement simplifies deployment and increases flexibility for organizations adopting impersonation.
Documentation:
- 24 Jul, 2025
Introducing Asgardeo Webhooks
Asgardeo Webhooks is an existing new feature that enables your applications to receive real-time notifications from Asgardeo, allowing you to respond immediately to important events in the user lifecycle and security flows. With webhooks, your systems can react to key user lifecycle events such as user registration, profile updates, password changes, and account status changes, as well as important security-related events such as login failures, session revocations, and account locking. The common use cases of the Asgardeo webhook include:
- Automatically provision users or send welcome notifications after successful registration.
- Update external systems such as user directories or CRMs when a user profile is updated.
- Notify security teams or external services upon password changes or resets.
- Integrate with SIEM systems to detect and respond to failed login attempts or suspicious activity.
Documentation:
- 08 Jul, 2025
End-to-End MCP Authorization: Streamlined Client-Server Representation
Asgardeo now offers enhanced support for standards-based authorization within the Model Context Protocol (MCP). MCP clients can be easily registered as applications in Asgardeo, utilizing a preconfigured template that aligns with the recommended identity configurations specified in the MCP standard.
Furthermore, MCP servers can be registered as protected resources. This allows for granular control over access to the MCP servers themselves, as well as their associated tools and resources. Organizations can define specific permissions for MCP tools and resources within registered MCP servers, thereby reflecting various access levels. This enables the authorization of MCP client applications to access these resources and the granting of user access through Role-Based Access Control (RBAC).
These capabilities streamline MCP integrations, ensure consistent authorization rules, and guarantee that only the appropriate clients and users have access to the necessary resources.
Documentation:
- 25 Jul, 2025
Identity for AI agents
Asgardeo now delivers first-class identity management designed specifically for AI agents, enabling organizations to manage AI agents securely and at scale. Each AI agent receives a unique, distinguishable identity with specific attributes, credentials, and metadata, allowing auditing, management, and lifecycle control while treating each agent as a trusted entity within the organization.
This feature provides comprehensive credential management with multiple authentication methods, role-based access control (RBAC) to ensure agents operate with minimum necessary permissions, while enabling organizations to log and monitor agent activities. Organizations can now support regulatory compliance, conduct forensic investigations, and detect unusual behavior while reducing security risks and enforcing strict access boundaries for their AI agents.
Documentation:
- 11 Jun, 2025
User Account Management Enhancements
Managing user accounts in Asgardeo is now more efficient with enhancements to verification, password setup, and recovery workflows. These improvements resolve common challenges such as handling pending verifications, expired password setup emails, locked accounts, and unverified user profiles.
Key Highlights
- Filter users by pending verification states: Advanced filters in the Console give administrators precise visibility into the user base. Instantly identify and segment users by states such as pending password reset, pending initial password setup, pending email verification, pending mobile verification, locked accounts, and disabled accounts.
- Resend password setup emails or set passwords directly: The Console now enables administrators to resend initial password setup emails and password reset emails when links have expired, or directly set a user’s password, ensuring a smoother onboarding and recovery experience.
- Notify users of unverified accounts in MyAccount: The MyAccount portal now displays clear prompts when accounts remain unverified, with options for users to resend verification links and complete the process independently.
- Together, these improvements simplify administrative workflows while empowering end users to complete verification, onboarding, and recovery seamlessly.
Documentation:
- https://wso2.com/asgardeo/docs/guides/users/manage-users/#resend-password-setup-linkcode
- https://wso2.com/asgardeo/docs/guides/account-configurations/user-onboarding/self-registration/#resend-account-verification-email
- https://wso2.com/asgardeo/docs/guides/users/manage-users/#filter-users
- https://wso2.com/asgardeo/docs/guides/user-self-service/self-register/
- 06 Jun, 2025
Pre-Issue Access Token Action Enriched with organizational context
We have enhanced the Pre-Issue Access Token (AT) action to provide richer organization context in the request payload when communicating with external services. This now includes
- User’s organization – the organization the authenticated user belongs to.
- Application’s organization – the organization where the client application is registered.
- Execution organization – the organization under which the action is executed.
With this enhancement, external services can make more contextual, organization-aware decisions during actions, enabling advanced B2B SaaS scenarios.
Documentation:
- 24 Jun, 2025
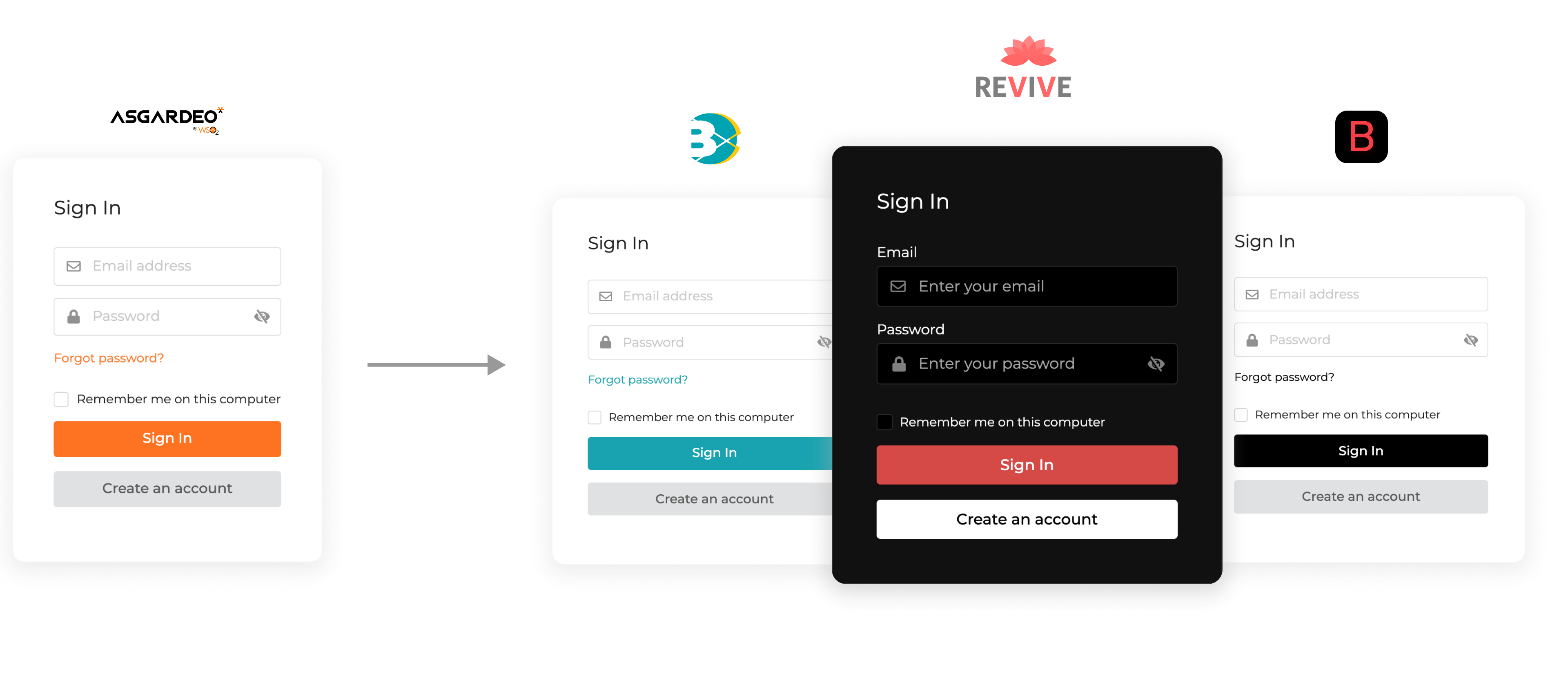
Extensive Branding capabilities
Asgardeo now offers extensive branding capabilities that go beyond basic logo and theme adjustments. Through the in-console editor, you can now fully customize end-user facing interface pages using HTML, CSS, and JavaScript. This allows for greater flexibility in tailoring the appearance, feel, and functionality of your login and self-service interfaces, ensuring a cohesive brand experience.
Documentation:
- 01 May, 2025
Registration Flow Builder
Introducing Registration Flow Builder (PREVIEW)
Create dynamic, customizable identity journeys with our new AI-powered Flow Builder. Easily design intuitive registration flows, and seamlessly integrate security checks like MFA and CAPTCHA - all without complex coding. Build flexible, user-friendly experiences tailored to your desired onboarding experience.
Documentation:
- 16 May, 2025
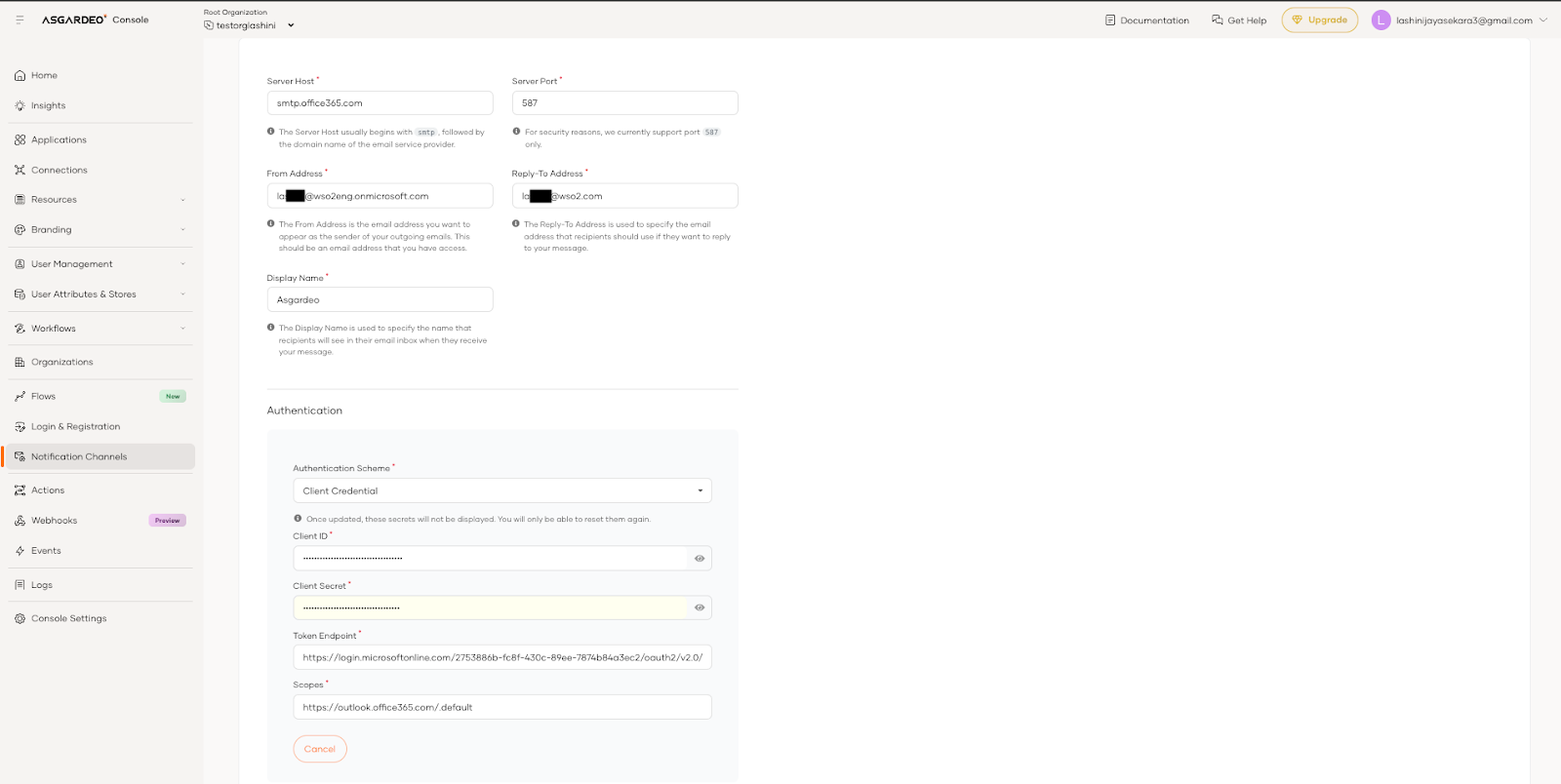
OAuth2 authentication for SMTP servers
OAuth2 authentication for SMTP servers.
The Email Provider template now supports OAuth2-based authentication for SMTP servers. Alongside the existing Basic authentication option, you can now configure SMTP using client credential authentication to meet modern authentication requirements.
This enhancement comes ahead of Microsoft’s planned retirement of Basic authentication with Client Submission (SMTP AUTH) in Exchange Online, scheduled for April 2026. Enabling OAuth2 support now ensures uninterrupted email delivery and keeps your configuration aligned with the latest security standards.
Documentation:
- 21 May, 2025
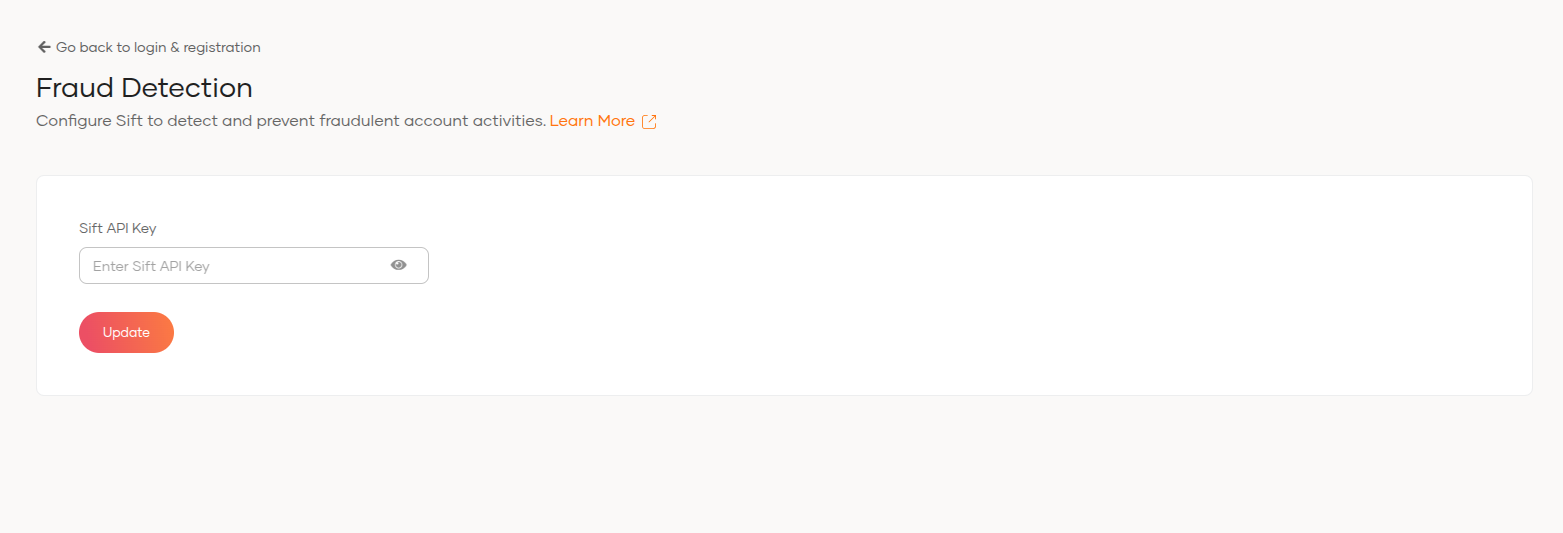
Conditional authentication function to retrieve Sift workflow decisions
Conditional authentication on Asgardeo now supports retrieving the Decision ID from Sift workflow executions.
This allows adaptive authentication flows to respond instantly to Sift’s real-time fraud insights, delivering more precise and fine-grained risk-based access control without adding complexity.
Documentation:
- 30 Apr, 2025
Support for Managing Third-party OAuth 2.0 Clients Per Organization to Enable B2B API Access
We’ve added support for managing third-party OAuth 2.0 clients at the organization level, enabling B2B businesses to securely expose their APIs to enterprise customers.
With this enhancement, customer/partner organizations,
- can manage their own access roles for third-party applications
- consume the Asgardeo organization-level APIs and exposed business APIs by service providing companies
Documentation:
- 30 Apr, 2025
Support for Publishing Logs to External Storage
Asgardeo now supports Remote Log Publishing for Audit and Diagnostics logs.
Remote Log Publishing enables organizations to securely transmit both Audit and Diagnostic logs to an external receiver.
Documentation:
- 30 Apr, 2025
Enhance Pre-Issue Access Token Extension to Update Refresh Token Expiry Time
With the new extension feature, Asgardeo enables external systems to define how long a refresh token should remain valid at the time it is issued. This means that, rather than relying on a fixed, predefined expiry time set within Asgardeo, refresh token lifetimes can now be dynamically adjusted based on user-specific or contextual information, offering greater flexibility and control over session management.
Documentation:
- 30 Apr, 2025
Email OTP Support for Password Recovery
Asgardeo has extended its password recovery options to include Email OTP, providing users with greater flexibility during the recovery process. Previously, password recovery was supported via email link and SMS OTP. With this enhancement, users can now also recover their passwords using a one-time password sent via email, offering an additional secure and convenient method to regain access.
Documentation:
- 30 Apr, 2025
Email/SMS OTP support for Admin-Initiated Password Reset
Asgardeo now supports admin-initiated password resets through multiple channels, enhancing flexibility and user experience. Previously, administrators could trigger password resets, but only with email links. With the latest update, admins can now initiate password resets using email link, email OTP, or SMS OTP. This allows organizations to choose the most suitable recovery method for their users based on security and usability preferences.
Documentation:
- 28 Feb, 2025
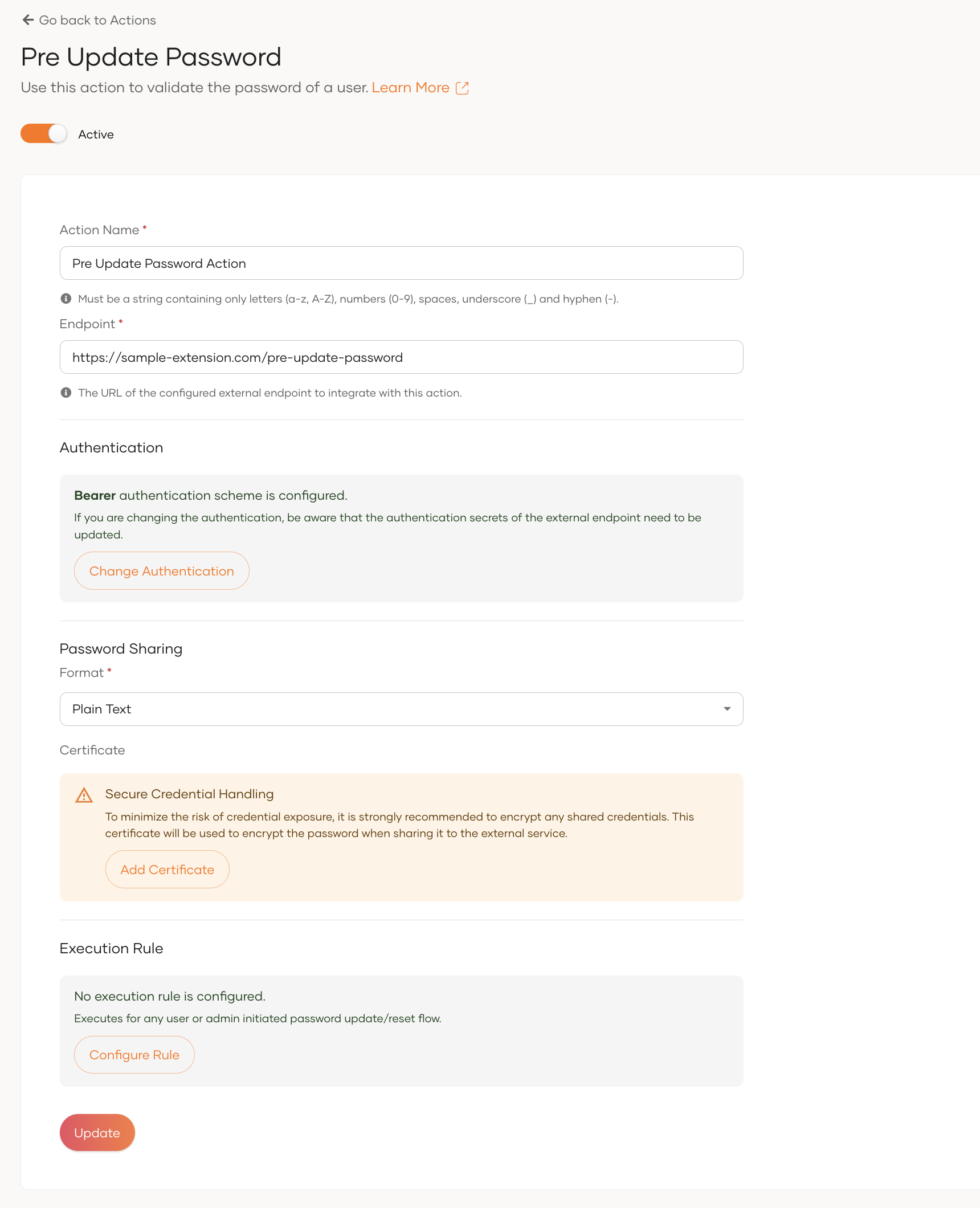
Extend Password Update Flows with the New Pre-Update Password Action
The Pre-Update Profile action is now available to enforce extra validation on the user password during various password update flows.
Also it can be invoked conditionally based on a simple conditional rule which allows you to configure the action to be invoked only for specific password updating flow.
- 31 Mar, 2025
Push Notification based Authentication
We’re excited to announce that push notification-based authentication is now available in Asgardeo! This new feature allows users to securely log in with a simple tap on their mobile device, eliminating the need to enter passwords or OTPs. Designed to enhance both security and user experience, push authentication provides real-time login approvals, making access faster, safer, and more convenient. Start using this modern, user-friendly MFA method today and experience seamless authentication!
Documentation:
- 31 Mar, 2025
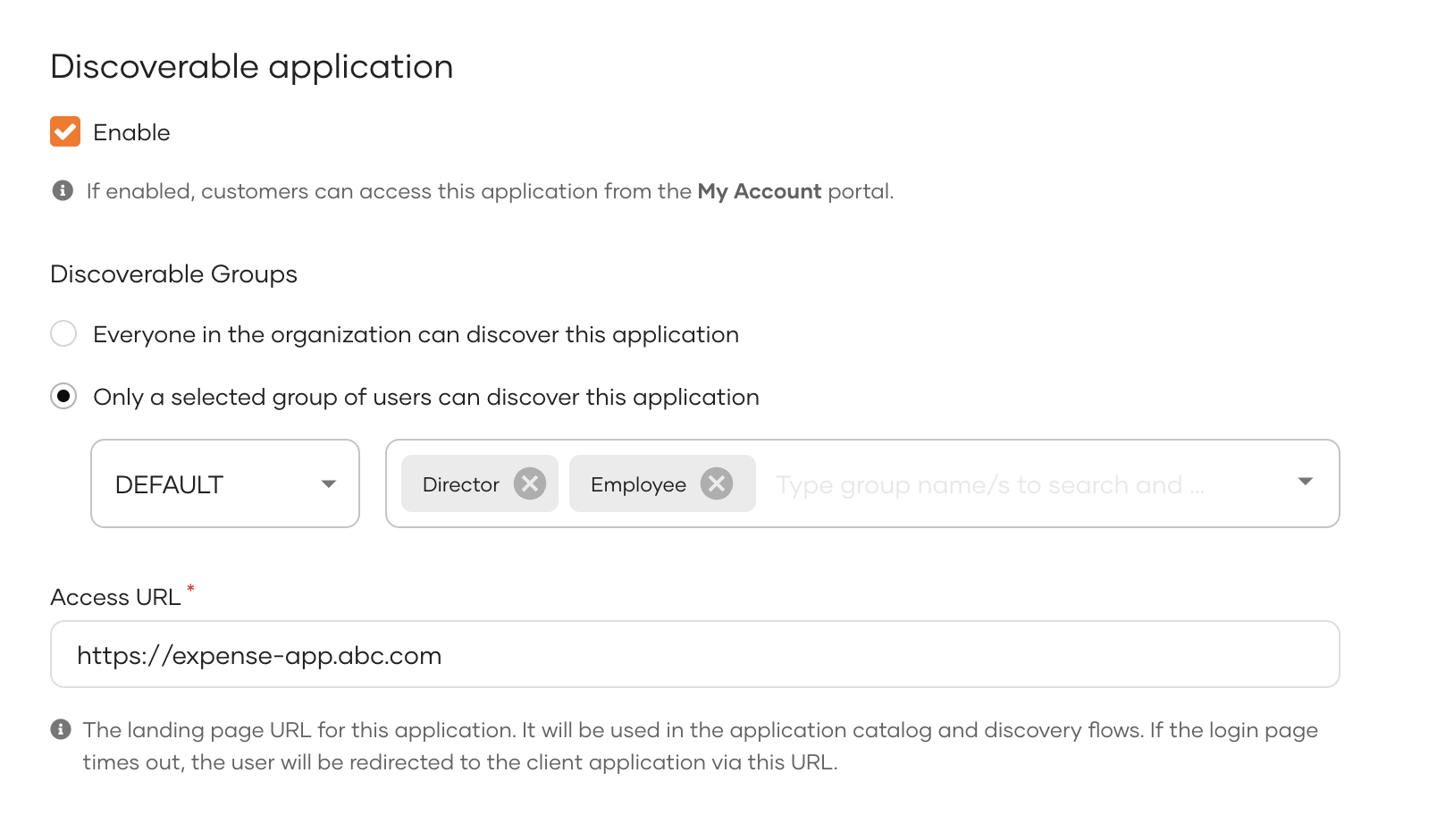
Conditional View Access For Discoverable Applications in MyAccount
Asgardeo now allows you to control the visibility of discoverable applications based on user groups. Previously, when an application's discoverability was enabled, it became visible to everyone in the organization via the My Account application dashboard. With the latest update, you can now specify a set of user groups as discoverable groups. Only users who belong to these selected groups will be able to see the application in the My Account portal.
Documentation:
- 31 Mar, 2025
Extend Profile Update Flows with the New Pre-Update Profile Action
A new Pre-Update Profile action is now available to validate user profile update requests before they are applied. Once enabled at the organization level, this action is triggered for all profile update requests, whether initiated through the self-service portal, admin portal, or SCIM API. It allows you to implement custom validation logic for user claims that are getting updated.
Documentation:
- 31 Mar, 2025
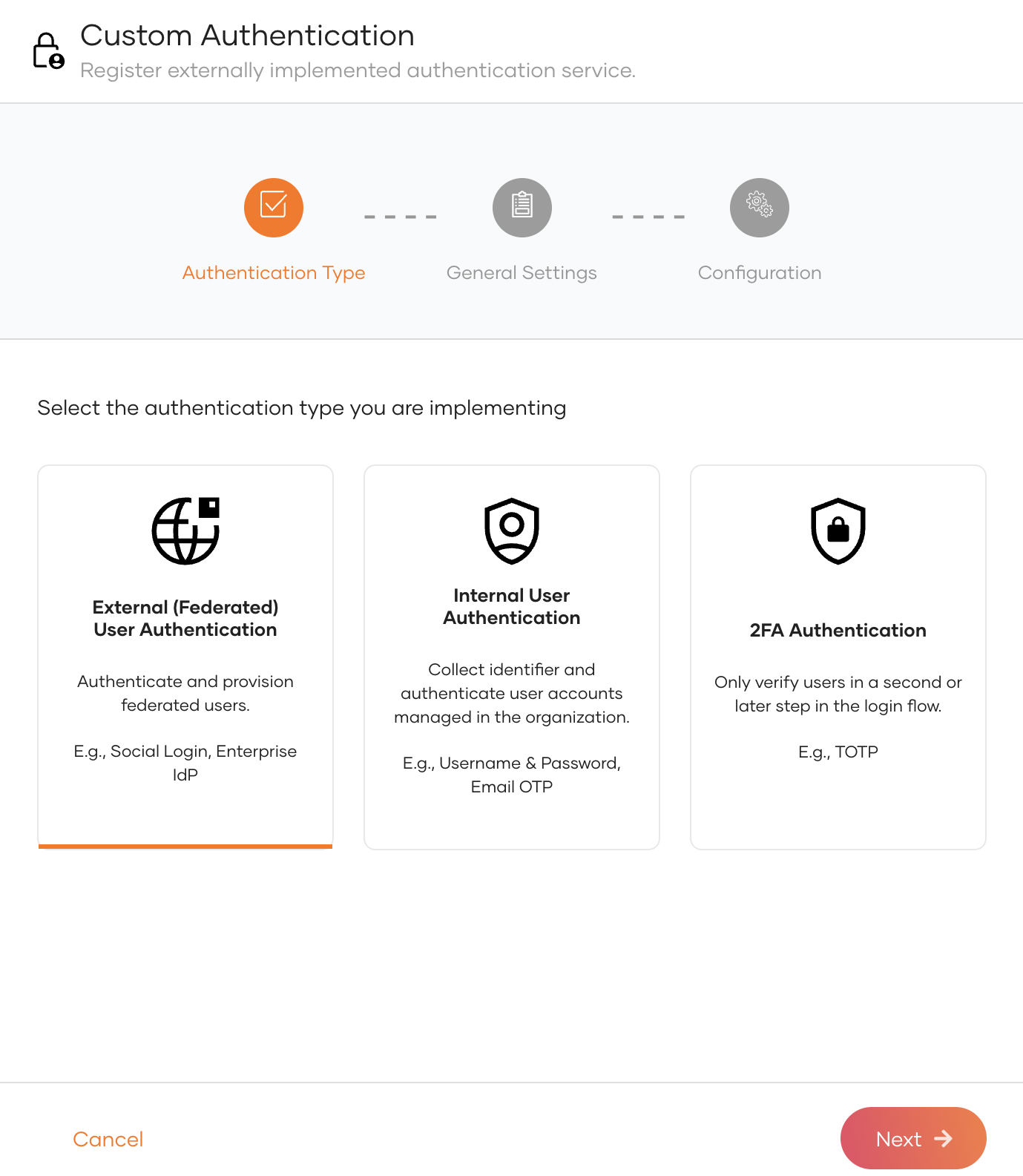
Extend Authentication Flows with Custom Authentication
Custom Authentication is now available in Asgardeo, a powerful feature that enables you to extend the authentication process. With this feature, you can integrate a custom authentication service to tailor the login experience, meeting specific needs beyond the built-in authenticators and implement your own custom authentication logic.
Documentation:
- 28 Feb, 2025
User account disabling
Asgardeo now lets you disable user accounts. This allows you to retain the user's information and activity history while preventing the user from logging into applications or to the self-service My Account portal.
This option is intended for a more permanent solution and should not be used for temporarily locking user accounts.
- 28 Feb, 2025
Distinct attribute profiles for different user flows
Asgardeo now lets you configure attribute settings such as making an attribute visible, mandatory or read-only per different user flow such as self-registration, console and my account.
For example, users can now make a user attribute (such as mobile number) to be mandatory in the My Account while not being mandatory in the console.
- 28 Feb, 2025
Support configuring multiple secondary user stores in sub-organizations
Asgardeo now allows you to configure and manage multiple secondary user stores within your organizations,
enabling seamless integration of user data from diverse identity sources.
With this feature, you can manage users and groups across several secondary user stores within each organization.
- 28 Feb, 2025
Override notification template content in sub-organizations
Asgardeo now lets you customize Email templates and SMS templates at your organization level.
Previously, Email templates and SMS templates of primary organizations were inherited by all child organizations.
With this enhancement, administrators can:
- Override Email and SMS templates at each organizational level
- Inherit Email and SMS templates from nearest parent organizations if organization level customizations are not available
This update delivers more control over the customization needs of Email and SMS templates at organization level.
- 28 Feb, 2025
Share users across organization hierarchy with role assignment
Asgardeo now allows administrators to share user profiles from a parent organization to child organizations, while also assigning specific roles during the process.
Multiple sharing policies are supported, enabling greater flexibility—administrators can choose to share users with all existing and future child organizations or selectively share them with specific organizations.
This feature streamlines user management by:
- Enabling centralized control over roles and access across the organization hierarchy
- Improving both efficiency and security
- 28 Feb, 2025
Ability to Update and Resolve Shared User Profiles via Organization Hierarchy
Asgardeo now lets you customize shared user profiles at each level of your organization hierarchy.
Previously, shared users between parent and sub‑organizations always inherited the same profile data.
With this enhancement, administrators can:
- Override or extend custom user attributes specifically for parent or child organizations
- Resolve attribute values for shared profiles based on the organization context
This update delivers more granular control over user attributes across multi‑organization setups.
- 31 Jan, 2025
Fraud detection in Asgardeo with Sift
Fraud detection capabilities are now available in Asgardeo, integrating with Sift to help organizations proactively detect and prevent fraudulent user logins.
Documentation Link: https://wso2.com/asgardeo/docs/guides/account-configurations/login-security/sift-fraud-detection/
- 31 Jan, 2025
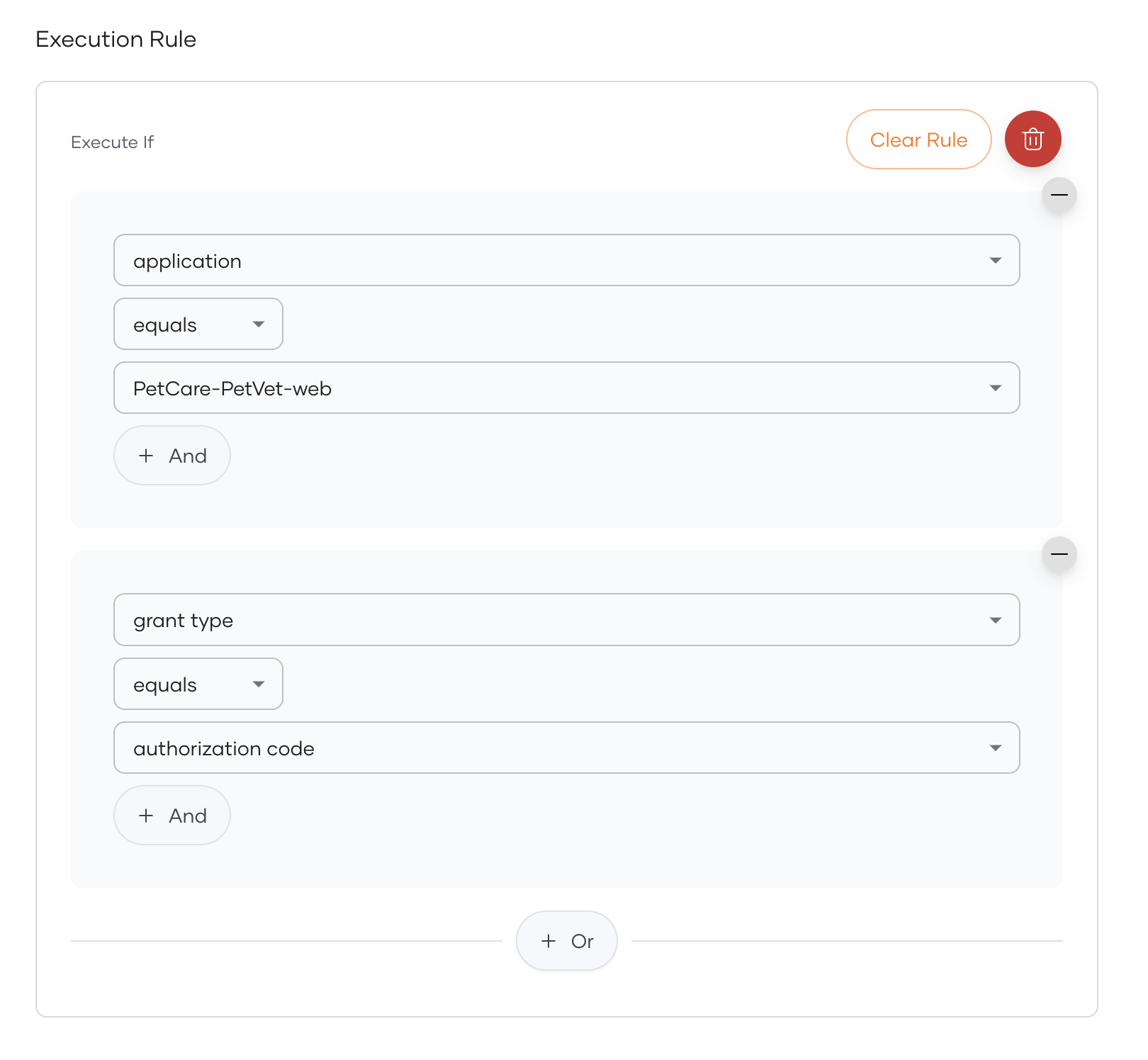
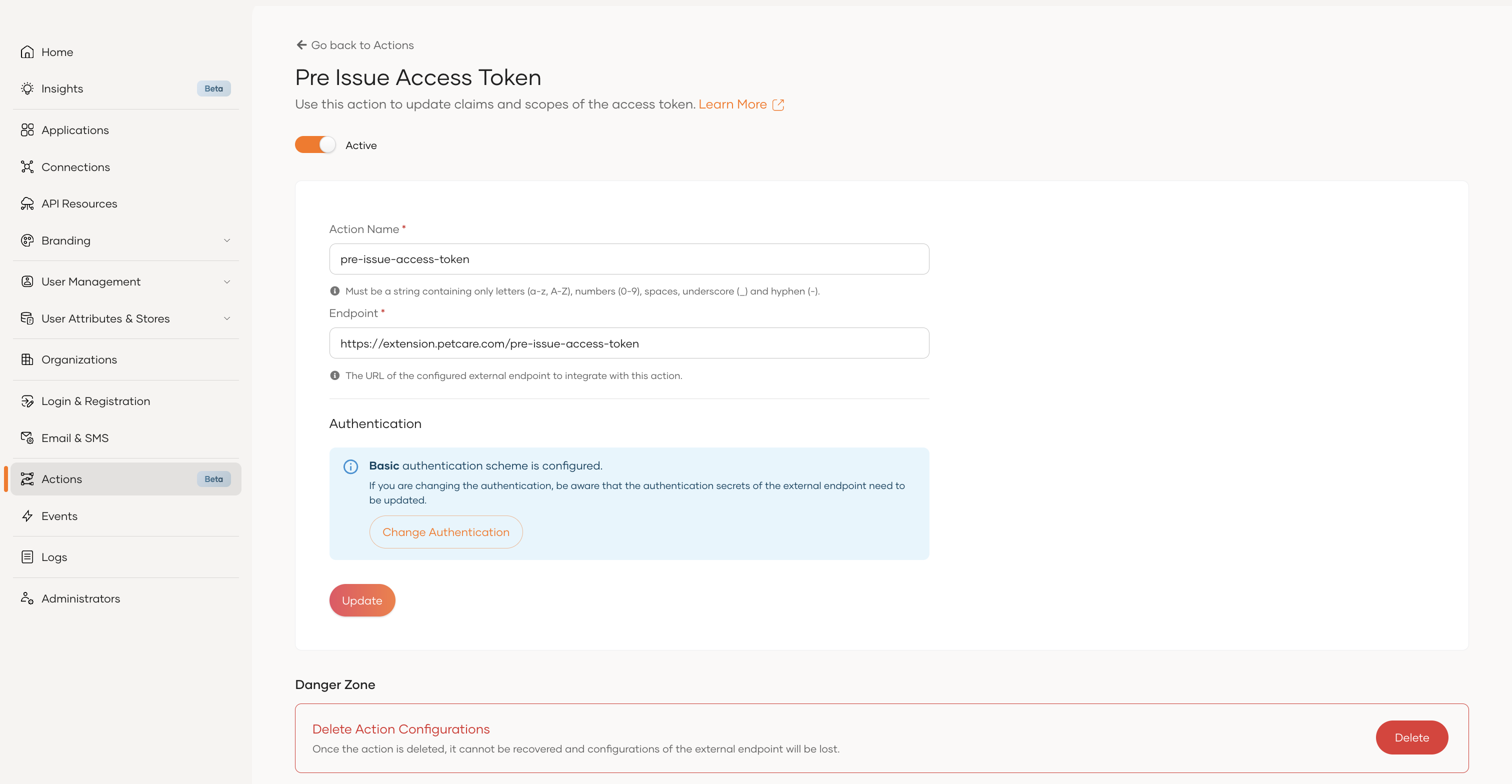
Pre-Issue Access Token action now supports conditional invocation
The Pre-Issue Access Token action can now be invoked conditionally based on a simple conditional rule. This action was previously invoked for all JWT token requests at the root organization level for authorization code, client credentials, password, and refresh token grant types once enabled. The update allows you to configure the action to be invoked only for specific applications or grant types.
Documentation Link: https://wso2.com/asgardeo/docs/guides/customize/actions/pre-issue-access-token-action/
- 18 Dec, 2024
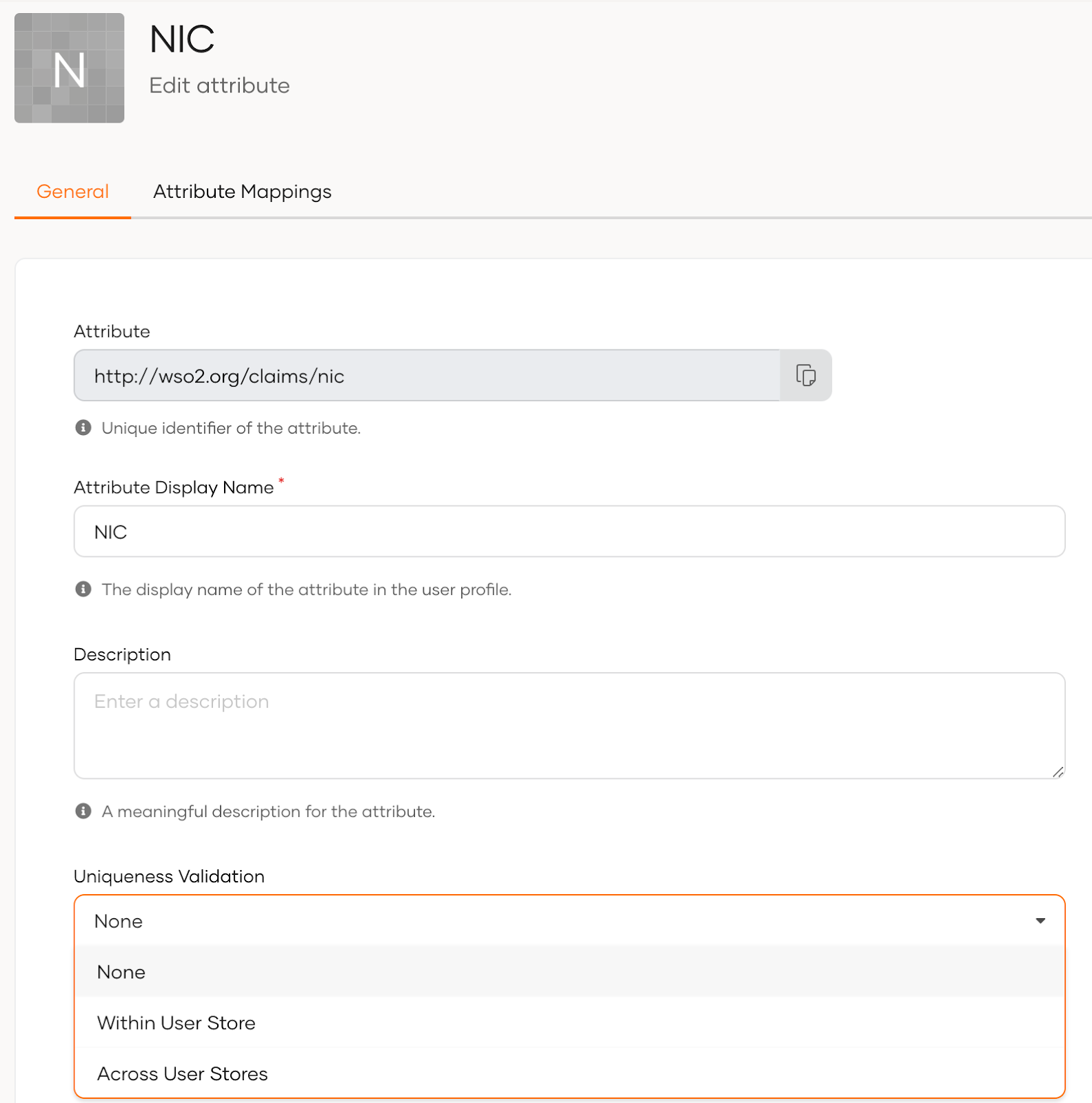
Uniqueness Validation For User Attributes
We have improved the uniqueness validation for user attributes providing flexibility for administrators to define the scope of uniqueness for each attribute separately.
The available options include:
- None: No uniqueness validation
- Within User Store: Validates uniqueness within the selected user store
- Across all User Stores: Validates uniqueness across all user stores
This enhancement offers granular control, enabling a more tailored and flexible approach to uniqueness validation.
Documentation:
- 16 Dec, 2024
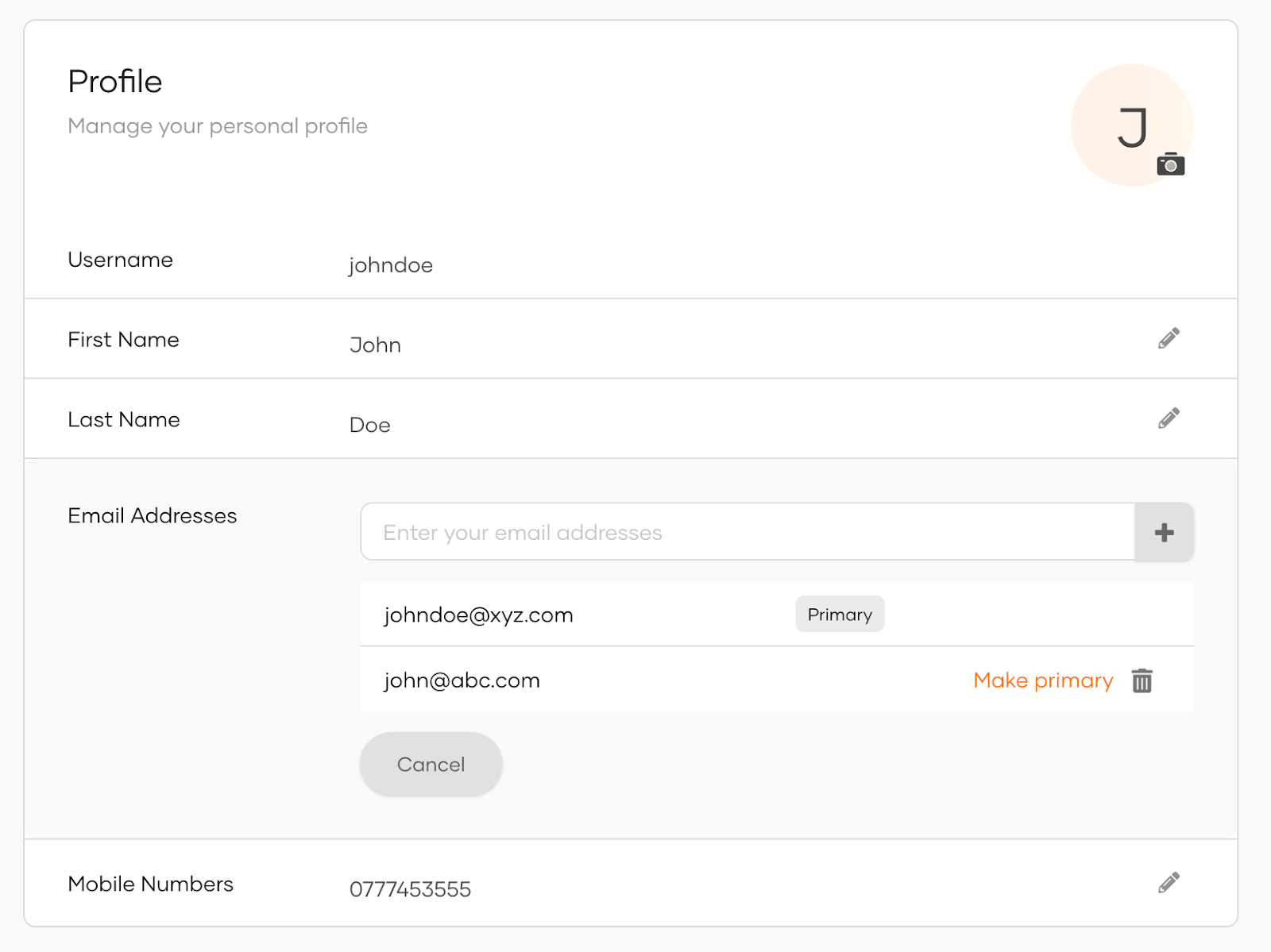
Multiple email addresses and mobile numbers support for user profile
Asgardeo now supports multiple email addresses and phone numbers in user profiles. You can easily add multiple contacts to your profile and select one email address and one mobile number as your primary choices for notifications and other services. This update offers greater flexibility, making it simpler to stay organized and connected.
Documentation:
- 16 Dec, 2024
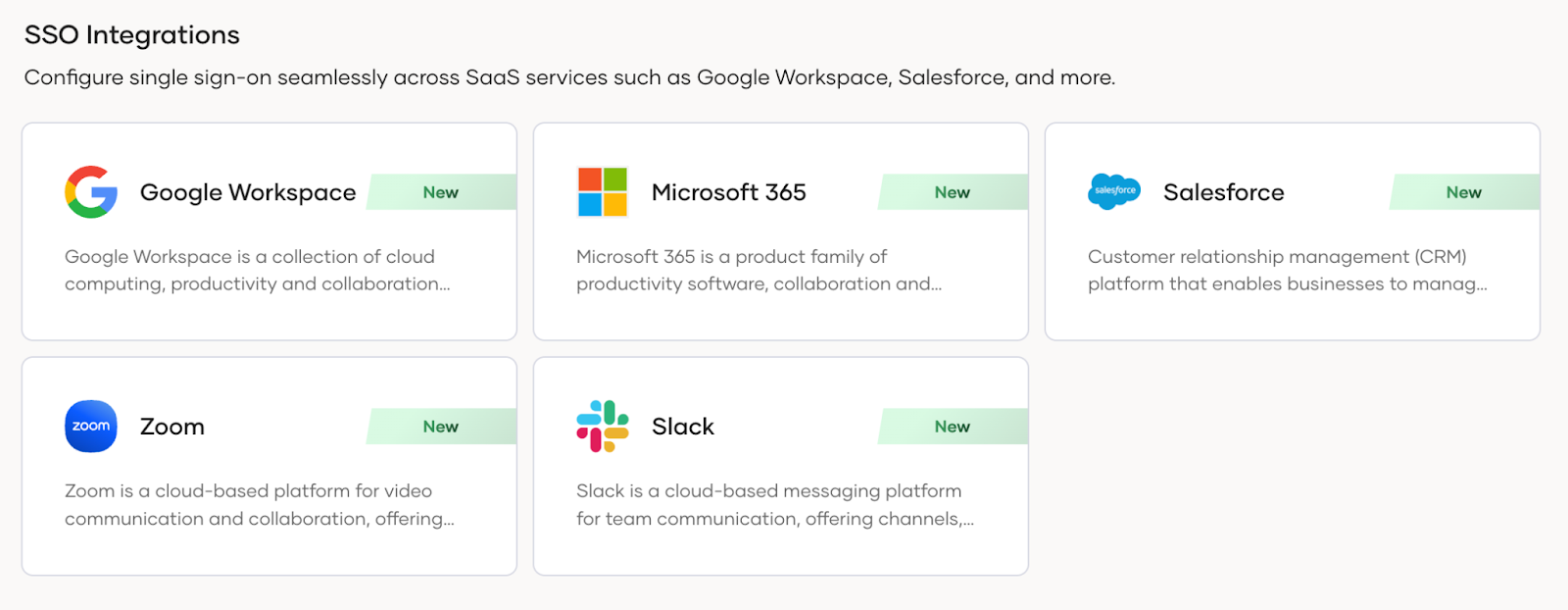
Easy to use SSO Templates for Zoom and Slack
We’re excited to introduce easy-to-use SSO templates for Zoom and Slack. You can now set up SSO effortlessly in just a few minutes for Zoom and Slack. The process is supported by a comprehensive in-app guide and detailed documentation, ensuring a smooth and straightforward configuration experience. We already offer SSO templates for Microsoft Office 365, Google Workspace and Salesforce.
Documentation:
- 16 Dec, 2024
In-built default roles for Asgardeo console
Asgardeo now offers built-in default roles for users accessing the Asgardeo console, ensuring they have the appropriate level of access.
The following roles have been introduced:
- Auditor
- Editor - Applications
- Viewer - Applications
- Editor - Users
- Viewer - Users
- Editor - Connections
This feature provides the best console experience for privileged users. As the organization administrator or owner, you can assign default roles to privileged users based on specific requirements.
Documentation:
- 19 Nov, 2024
Introducing hard limit for scim2/Users/.search API
We are introducing a hard limit on the count parameter for the scim2/Users/.search API. For organizations created after this improvement, the maximum value that can be specified for the count parameter will be capped at 100. Even if a request includes a value greater than 100, the API response will only return up to 100 users.
This improvement ensures optimized API performance and maintains system reliability for all users.
To retrieve additional users beyond this limit, customers will need to implement pagination in their API requests. We recommend that developers update their integrations accordingly to handle this limit and include support for pagination where necessary.
Documentation:
- 19 Nov, 2024
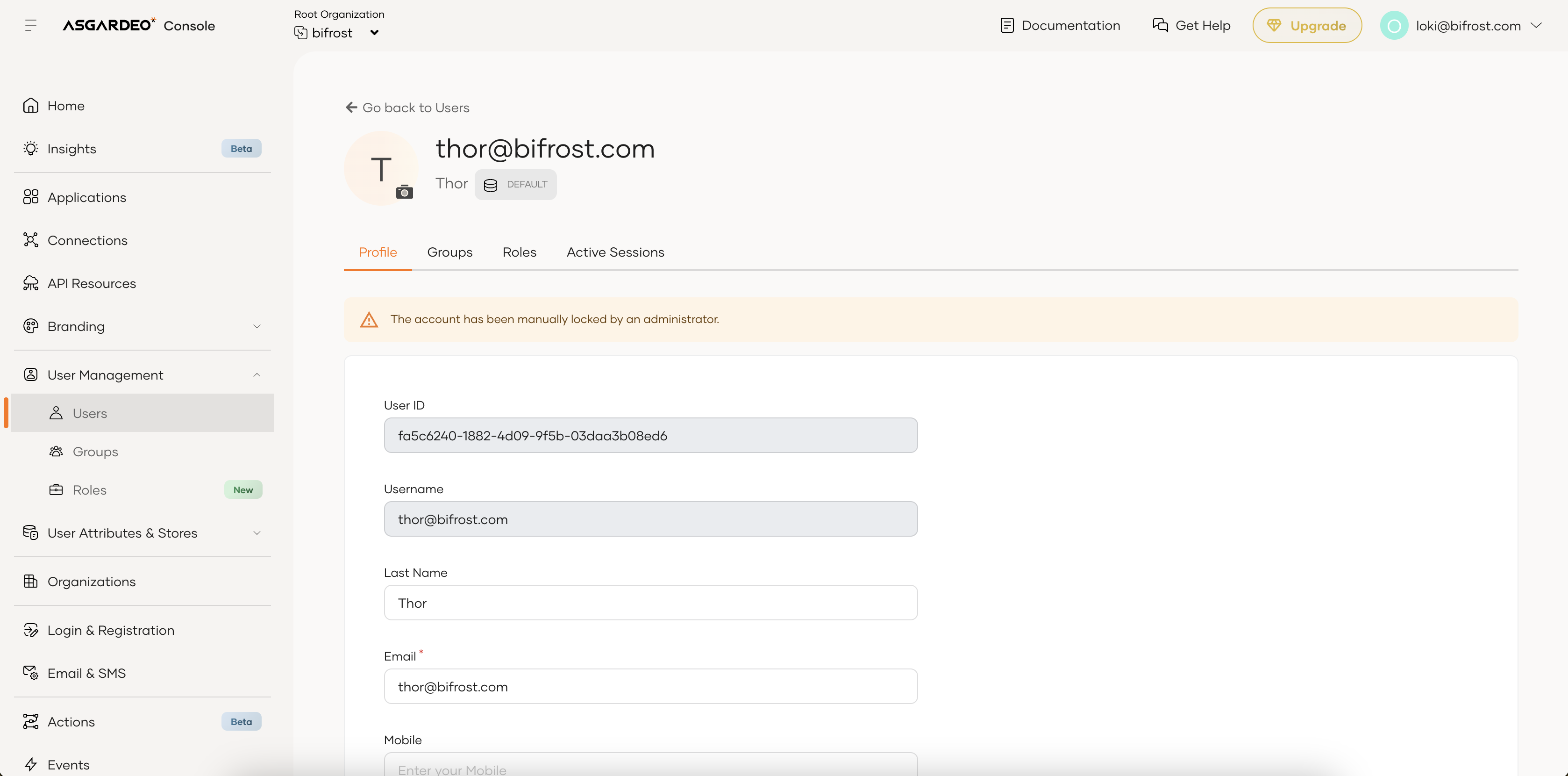
User Account Lock Reasons in User Profile
We are enhancing Asgardeo’s account management by introducing a feature that displays the reason for a user account lock directly within the user profile. Administrators can now view detailed explanations for locked accounts.
Locked reasons can be
- Pending user self-registration verification
- Pending password reset or email verification
- Administrator-initiated locks
- Account locks due to multiple failed login attempts
Additionally, in the users list, locked accounts are indicated with a lock icon. Administrators can hover over this icon to view the lock reason as a tooltip, providing an alternative way to access this information without navigating to the user profile.
This feature simplifies account troubleshooting and improves efficiency, especially for administrators managing a large number of users.
Documentation:
- 20 Nov, 2024
Pre-Issue Access Token Action now supports extended token validation use cases
The Pre-Issue Access Token action has been upgraded to support more flexible validation use cases during the access token flow. Previously, this action could only modify token scopes and attributes before issuing the token.
With this update, you can now validate token scopes, user claims, request context, expiry time, and more. If a validation fails, the action can return a client error directly to the application.
We’ve introduced a new ‘FAILED’ state in the response format for external services implementing an action to return client errors. Use the ‘FAILED’ state to indicate validation failures in order to trigger an appropriate error response to the application.
This improvement gives you more control over token issuance and strengthens validation workflows.
Documentation:
- 21 Nov, 2024
Alternate user attributes handling method for Access Token attributes
We have introduced an improvement to the handling of JWT Access Token attributes
With this enhancement, for new applications, the "Access Token" section now provides an option to explicitly select the attributes to be included in the token. As a result, user attributes configured in the "User Attributes" section will no longer be automatically added as access token attributes.
Existing applications will be marked as outdated because the access tokens they issue still include user attributes configured. To apply the new functionality to these applications, use the outdated application warning banner to update them. After the update, the previously configured user attributes will be automatically added as access token attributes by default, ensuring the application's existing functionality remains intact. You can manage the added access token attributes by adding or removing them from the Access Token Attributes section.
The access token attributes included in the token are no longer bound to scopes. Previously, only the user attributes associated with a scope were added to the token. Now, regardless of the scopes requested, all selected user attributes will be included in the token.
By letting you explicitly select access token attributes, this feature minimizes the exposure of sensitive user information (PII) when sharing access tokens with resource servers and reduces token size for improved performance.
Please note that the behavior of the ID token will remain the same.
Documentation:
- 01 Nov, 2024
Onfido Identity Verification in Asgardeo
Onfido, a leading identity verification service, is now integrated with Asgardeo. This allows you to securely onboard new users with end-to-end identity verification powered by Onfido, ensuring real-time validation using legal documents such as passports, driving licenses, and national IDs.
By leveraging Onfido's advanced verification technology within Asgardeo, you can strengthen fraud prevention measures, enhance compliance, and deliver a seamless user experience—all within a single platform.
Documentation:
- 01 Nov, 2024
Application-Specific Branding
Until now, Asgardeo offered only organization-level branding, which restricted businesses to a one-size-fits-all approach across their applications. Recognizing the need for greater flexibility, we’ve introduced application-specific branding, allowing businesses to create unique, tailored brand experiences for each application directly through the Console. This enhancement not only elevates personalization across login portals and user interfaces but also positions Asgardeo as the go-to solution for businesses seeking to deliver impactful, differentiated user experiences.
Key Benefits:
- Supports unique branding per application, a common customer request.
- Addresses client needs and expands Asgardeo’s appeal with tailored solutions.
Impact:
Ideal for organizations with multiple applications, this feature strengthens user engagement through differentiated branding.
Documentation:
- 01 Nov, 2024
Onboarding SSO Templates for Popular Enterprise SaaS Applications
Asgardeo has simplified the SSO configuration process for popular workforce SaaS applications by providing a dedicated template for each app. Our ready-to-use SSO configuration templates streamline onboarding for enterprise SaaS apps, requiring minimal setup from administrators and offering clear, step-by-step guidance for vendor-side configurations.
Included Templates:
- Google Workspace
- Salesforce
- Office 365
Get users up and running faster with secure, hassle-free SSO integration for your organization’s most trusted applications.
Documentation:
- 01 Nov, 2024
Application Access Token improvements
We have made below enhancements to the application access tokens.
- “sub” claim of application access tokens will be changed to client id of the application.
- Removal of “username” claim from the application access tokens introspection response.
The sub claim in application tokens now uses the application's client_id rather than the application owner’s user ID. Previously, the sub claim reflected the application owner’s username. This updated behavior will apply automatically to new OIDC applications. For existing applications, you can update them via the console to adopt this latest functionality.
Application access tokens’ introspection response was enhanced by removing the username claim as this field is not relevant for machine-to-machine communication. The value of the field was previously set as the application owner's user ID. With this update, the username field will no longer be included in the token response. This change will automatically apply to new OIDC applications. Existing applications can be updated via the console to adopt this latest functionality.
Documentation:
- 01 Oct, 2024
Enhancements to httpGet and httpPost Functions
We are announcing several enhancements to the httpGet and httpPost functions in the Asgardeo conditional authentication script!
With this improvement, users can now invoke APIs secured with various authentication methods, including basic authentication, API key, bearer token or client credentials grant with few simple steps. You just need to specify the authentication type, endpoints, and secrets to seamlessly and securely integrate external APIs into your conditional authentication workflows.
Additionally, diagnostic logs are now available to help troubleshoot failures when invoking external APIs.
Documentation:
- 01 Oct, 2024
Email Domain-based Organization Discovery for Login Flows
With this improvement, you can use your customer or partner organization user’s email in the “login_hint” query parameter to seamlessly direct users to their organization’s login page. This enhancement simplifies the login process and improves the login user experience, especially when you capture the user’s email through your own user interfaces.
Documentation:
- 01 Oct, 2024
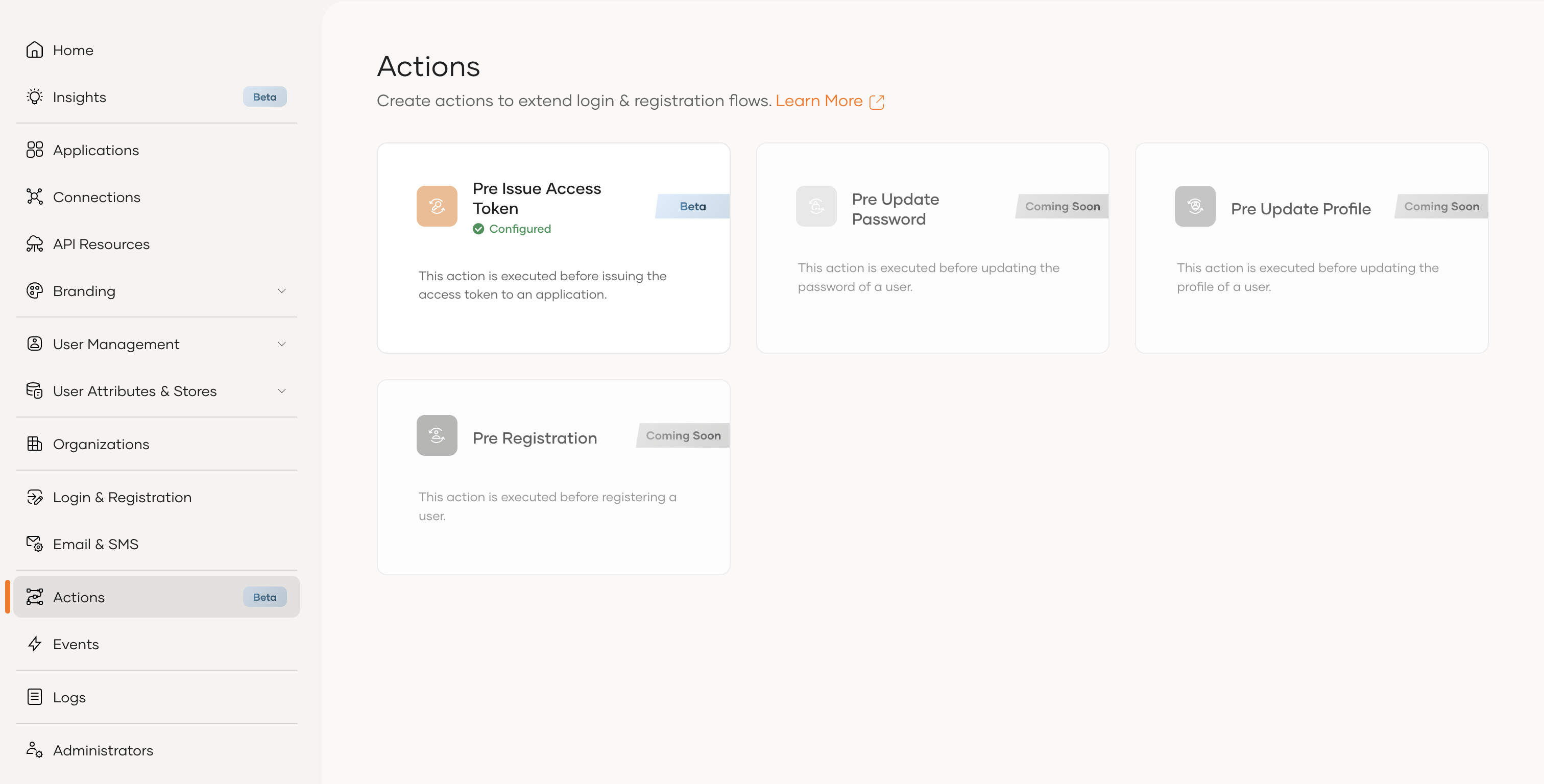
Actions to Customize and Extend, User on-boarding, Login and Account Management Flows
We’re excited to announce the introduction of Actions, a powerful new feature that allows you to customize specific flows in Asgardeo such as user on-boarding, login and account management by integrating with an externally hosted HTTP endpoint. enable you to modify and extend the behavior of flows to better suit your unique needs.
As the first of many extensions to come, we’ve released the Pre-Issue Access Token Action in Beta. This feature lets you modify access tokens or perform additional checks before they are issued, providing enhanced control over the token issuance process.
Stay tuned for more extensions in the future!
Documentation:
- 02 Sep, 2024
Passkey Support for App-Native Authentication
We are excited to announce the introduction of passkey support for app-native authentication! With this feature, users can enjoy a faster and more secure login experience by authenticating to their mobile apps using passkeys. App-native authentication is an API-based authentication mechanism that allows developers to seamlessly integrate authentication directly within a native app's environment.
Documentation:
- 01 Sep, 2024
User Impersonation
We are excited to announce the launch of User Impersonation, a powerful feature designed to streamline customer support, testing, and troubleshooting processes. This feature allows system administrators or support staff to temporarily access a user’s account, with the user's consent and the administrator's approval, without asking the user's login credentials.
This feature not only enhances the support experience but also offers peace of mind, knowing that user privacy is maintained, and impersonation access is temporary, controlled, and well-audited.
Documentation:
- 01 Sep, 2024
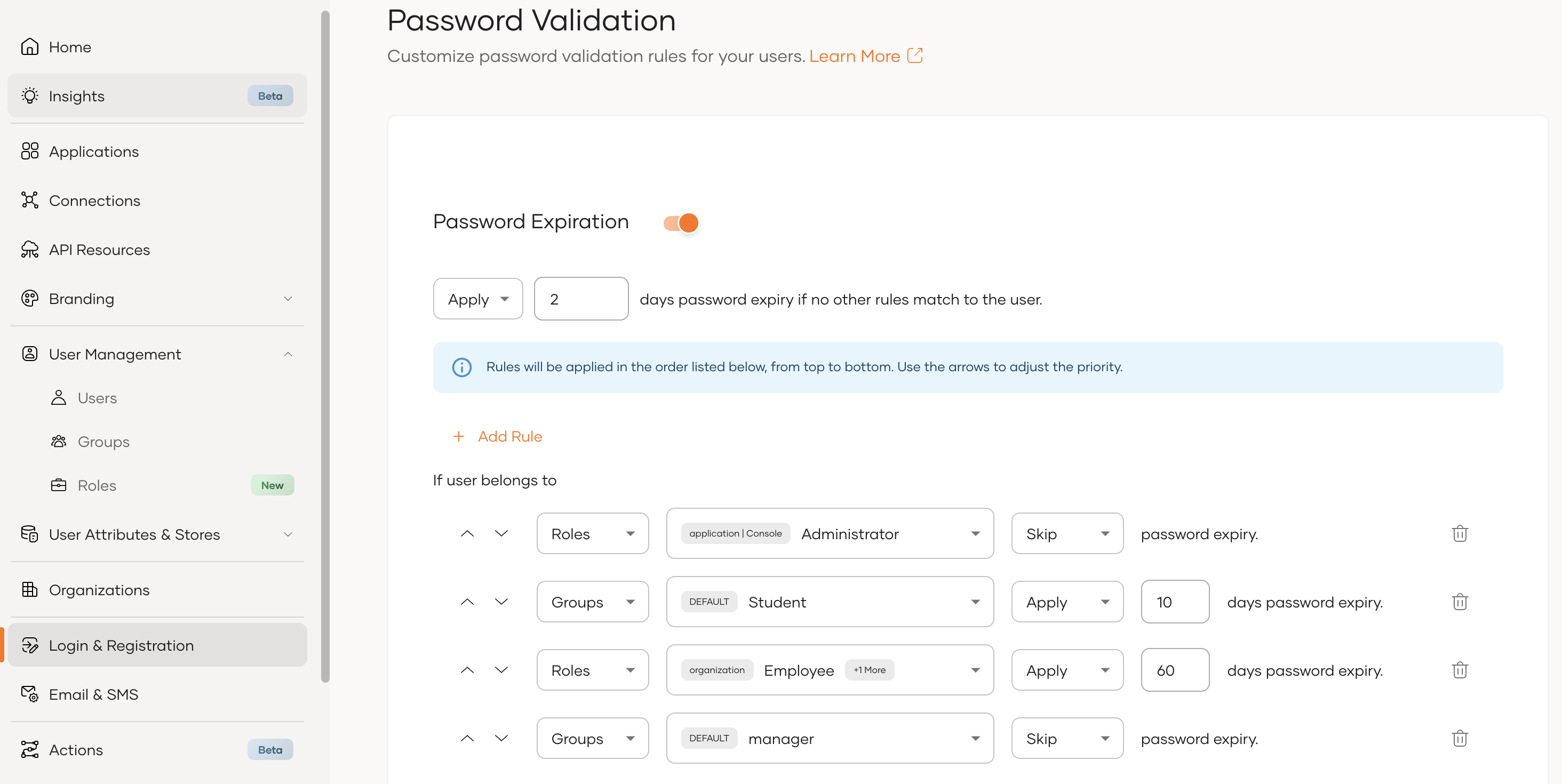
Rule-Based Password Expiry
We're excited to introduce rule-based password expiry! This enhancement allows administrators to set password expiration rules specifically tailored to user groups and roles, offering a more flexible and precise approach to password security. With this feature, expiration policies can be effectively targeted, ensuring the right rules are enforced for each user segment.
Documentation:
- 01 Sep, 2024
Organization Filtering Based on Meta Attributes
We have extended the organization filtering capabilities of Asgardeo to include meta attributes. With this enhancement, you can now filter organizations not only by attributes, such as name, ID, and parent organization name, but also by meta attributes enabling more granular and effective organization management.
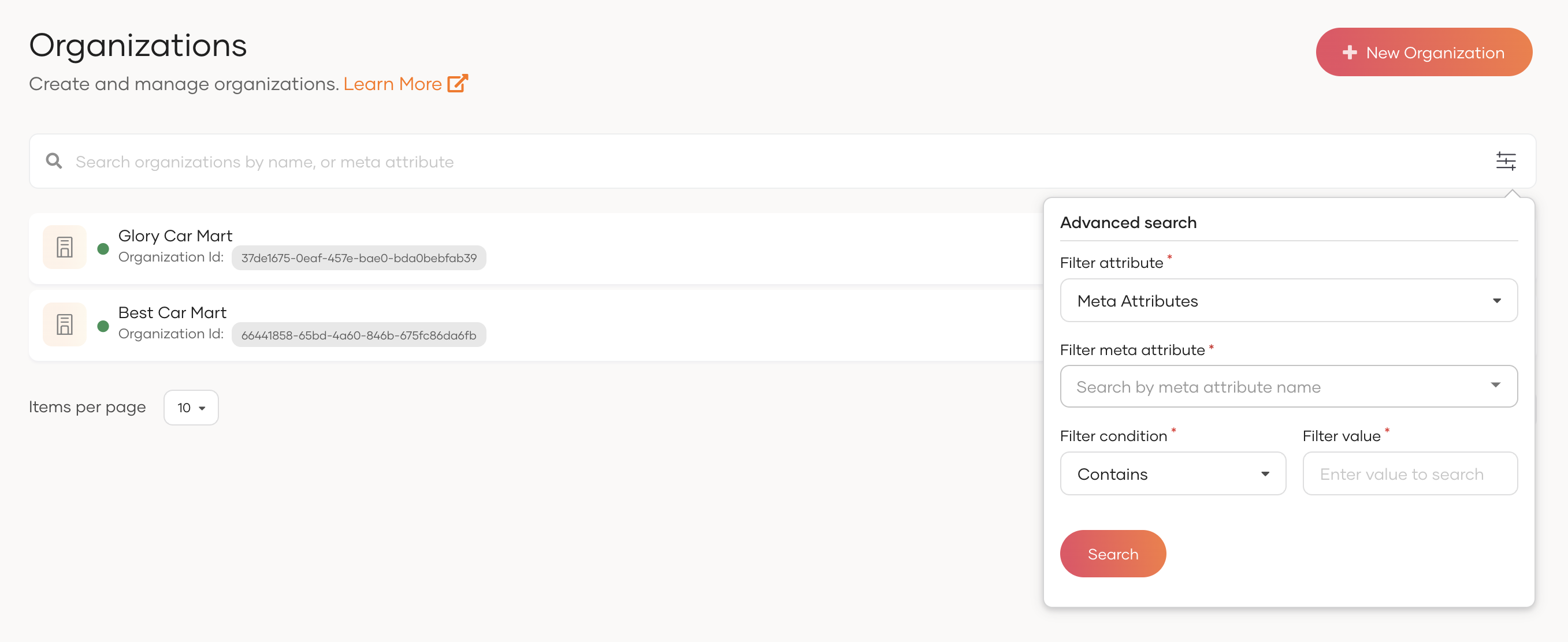
Documentation:
- 01 Aug, 2024
Adaptive Authentication Utility function to Mask Sensitive Content in Logs
We are thrilled to introduce the new getMaskedValue function for Asgardeo conditional authentication scripts! This powerful addition is designed to enhance security by allowing developers to mask sensitive information, such as Personally Identifiable Information (PII), in their adaptive authentication script logs.
- Enhanced Privacy: This function helps protect user privacy by obscuring sensitive data in logs. This is crucial for maintaining confidentiality and adhering to data protection regulations.
- Customizable Masking: Developers can customize which parts of the data to mask, ensuring that sensitive information is adequately protected while still allowing for effective troubleshooting and analysis.
Documentation:
- 01 Aug, 2024
On-Demand Silent Password Migration
We are thrilled to introduce the Asgardeo On-Demand Silent Password Migration, enabling a seamless transition of your users' credentials from an existing Identity Provider to Asgardeo.
As businesses evolve, organizations may need to migrate from a legacy Identity Provider to a modern solution like Asgardeo. One of the main challenges during this transition is the transfer of user credentials. Because credentials are stored differently across systems, a password stored in one system may not be directly usable in another. Asgardeo On-Demand Silent Password Migration addresses these challenges by ensuring a smooth and secure migration process.
- Seamless User Experience: Users can continue logging in with their existing credentials without resetting passwords.
- Silent Transition: Passwords are migrated silently during the first successful login attempt.
- Uninterrupted Authentication: If the user's password hasn't been migrated yet, Asgardeo securely authenticates against the legacy IdP and completes the migration in real-time.
How It Works:
When users log in to the application, they are redirected to the Asgardeo login screen to enter their legacy IdP credentials. If their password has not been migrated yet, Asgardeo authenticates the credentials with the legacy IdP. Upon successful authentication, the password is silently migrated, and the user is redirected back to the application, authenticated through Asgardeo.
Upgrade to Asgardeo today and enjoy a hassle-free transition with our On-Demand Silent Password Migration feature!
Documentation:
- 01 Aug, 2024
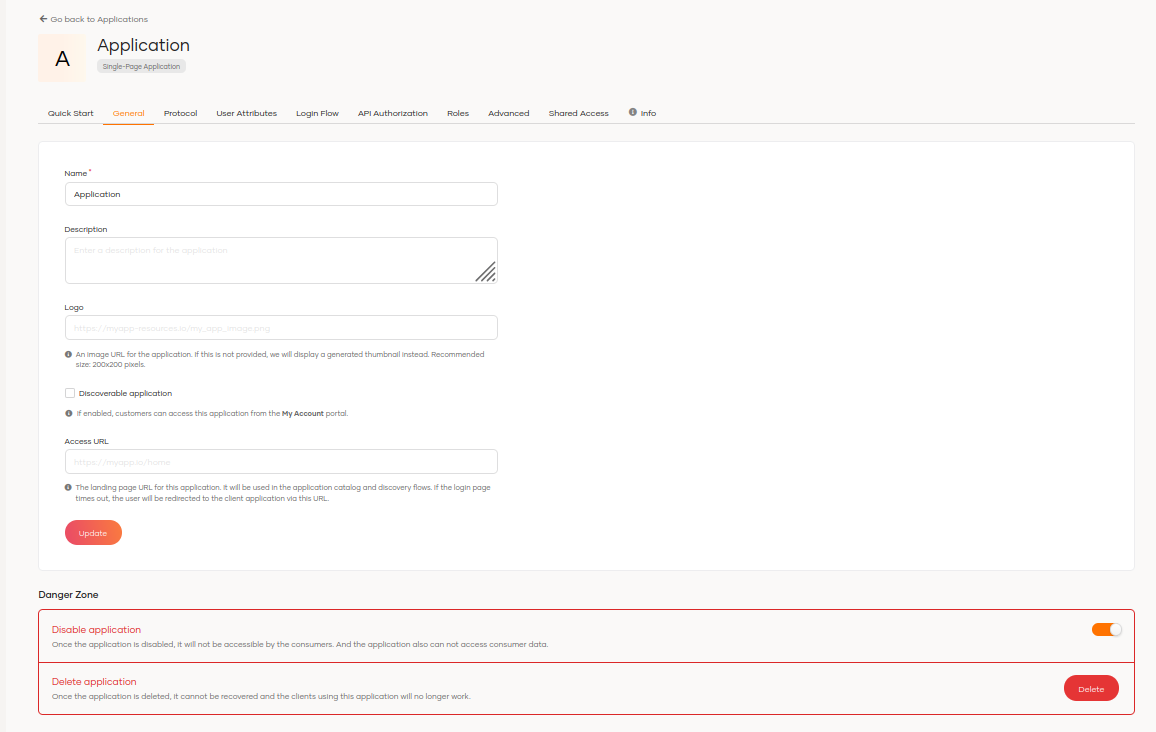
Capability to Disable an Application
We are excited to announce a significant update aimed at enhancing the security and integrity of our application and improving ongoing maintenance processes.
Organizations today face constant risks from potential cyber attacks that can lead to unauthorized access to sensitive information. Such incidents jeopardize the privacy and security of both the organization and its users. To proactively mitigate these risks, we are implementing the following measures:
- Disabling Access to Compromised Applications/Maintenance
- Preventing Access to User Information: While we already take steps to protect user information, this new feature introduces an additional layer of security. Specifically, when the application is disabled or undergoing maintenance, it will no longer be able to access user information—even if the user has previously given consent.
- Token Invalidation: Invalidate all previously issued tokens (e.g., JWTs) to ensure they can no longer be used to authenticate requests.
Documentation:
- 02 Jun, 2024
Enhanced Configuration Capabilities for the Self-service Portal
We’ve enhanced the configuration capabilities for the self-service portal. Now, administrators can configure the login flow with greater flexibility and share the self-service portal with B2B organizations just as seamlessly as they do with other applications in the organization.
Documentation:
- 02 Jun, 2024
Fine Grained Access Control for Asgardeo Management APIs
We’ve enhanced the access management capabilities of Asgardeo management APIs. With this improvement, organizations now can define fine-grained access controls for management APIs, allowing for more precise and secure management of Asgardeo resources.
Documentation:
- 02 Jun, 2024
Machine-to-Machine API Authorization
Our latest update introduces the capability to register Machine-to-Machine (M2M) applications, providing robust access control for non-interactive apps using the client credentials grant. This includes IoT devices, CLI tools, and more, allowing for flexible and specific access control. This enhancement enables secure machine-to-machine communication while enforcing granular access, authorization, and security requirements.
Documentation:
- 02 Jun, 2024
Organization Level Roles
Asgardeo now supports creating roles at the organization level, allowing shared access control across all applications within the organization. This new role management capability centralizes access control, eliminating the need to duplicate roles across multiple applications.
Documentation:
- 02 Jun, 2024
Asgardeo B2B CIAM Update: Organization APIs, Email Domain-based Organization Discovery and more!
Our latest upgrade contains major feature updates for Asgardeo B2B CIAM offering enhancing both security and user experience.
Enhancements for B2B Application Authorization
We have introduced a new API category named “Organization APIs”. These APIs simplify the management of organizational-level resources in your B2B SaaS applications with API authorization and Role Based Access Control. Now, you no longer need to create repetitive roles in each organization to manage organizational-level resources. Instead, you can simply create roles in your root organization where the B2B SaaS application is registered with organization API scopes and share them with organizations.
Documentation:
- Organization APIs: https://wso2.com/asgardeo/docs/apis/organization-apis/
-
Support RBAC for B2B applications
https://wso2.com/asgardeo/docs/guides/organization-management/api-authorization-for-b2b/
Email Domain-based Organization Discovery
We are pleased to introduce the email domain-based organization discovery functionality tailored for B2B SaaS solutions. This feature facilitates seamless user routing to respective organization logins based on their email addresses.
Documentation:
Invite Users from Parent Organization
We have now enabled seamless collaboration between parent organizations and their customer/partner organizations through parent organization user inviting capability. Furthermore, administrators can manage the groups and roles of invited users on an organization-wide basis.
Documentation:
Empower Branding Autonomy for Organizations
Traditionally, the branding of customer/partner organizations is inherited from the primary B2B business organization. With our latest improvements, organizations now have the freedom and flexibility to tailor their branding to better reflect their own identity and value. Whether it's adjusting logos, color schemes, or messaging, the power is now in their hands!
Documentation:
Console access for B2B Organization Administrators
We have enhanced the Asgardeo Console to support seamless delegated administration for B2B organization administrators. This update enables administrators to efficiently manage and provide delegated administration within their respective organizations. By leveraging the Console, admins can streamline administrative processes, ensuring smoother operations and enhanced control over organizational management.
Documentation:
MyAccount access for B2B Organization Users
We have enhanced Asgardeo MyAccount self-service portal by making it available to B2B organization users as well. If your customer or partner organizations handle user management within Asgardeo, you can utilize the enhanced out-of-the-box selfcare application. Further, MyAccount portal can be customized with the organization's branding and tailored login flows based on each organization's preferences.
Documentation:
- 10 Apr, 2024
App-Native Authentication
We are pleased to introduce the “App-Native Authentication” feature for Asgardeo now.
When developing applications (especially native/mobile apps) developers look at implementing their login flows within the apps itself where they target more on UX.
To cater to this requirement, App-Native Authentication capability is introduced in which it will provide the app developer the capability to implement a complete authentication capability within the application.
Key Highlights:
- A flexible API containing all necessary details to render UIs inside the application itself.
- Supports handling authentication orchestration logic at Asgardeo without taking that overhead to the application (e.g: Based on the device the user logs in to the app, prompt the second factor)
- APIs are provided closer to OAuth 2.0/Open ID Connect standards rather than providing proprietary APIs
Documentation:
https://wso2.com/asgardeo/docs/guides/authentication/add-application-native-login