WSO2 Empowers Innovation: Transforming 700+ Companies
Across sectors and geographies, digitally driven organizations rely on WSO2 to deliver awesome digital experiences quickly, easily, and securely. Discover their stories.
Read Customer Stories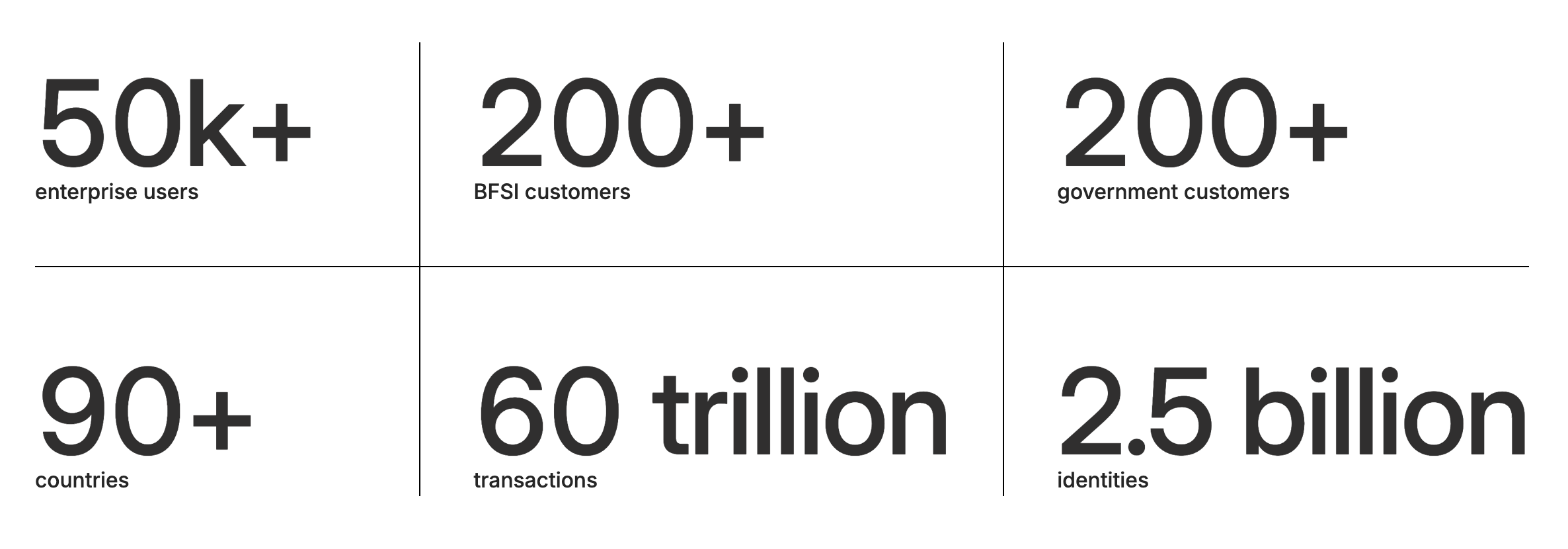
We Help Customers Achieve Measurable Results
Want to Know More?
For more information on how WSO2 empowers global customers, speak to one of our sales team.